Antivirus Action
![]() Written by Tomas Meskauskas on (updated)
Written by Tomas Meskauskas on (updated)
What is Antivirus Action?
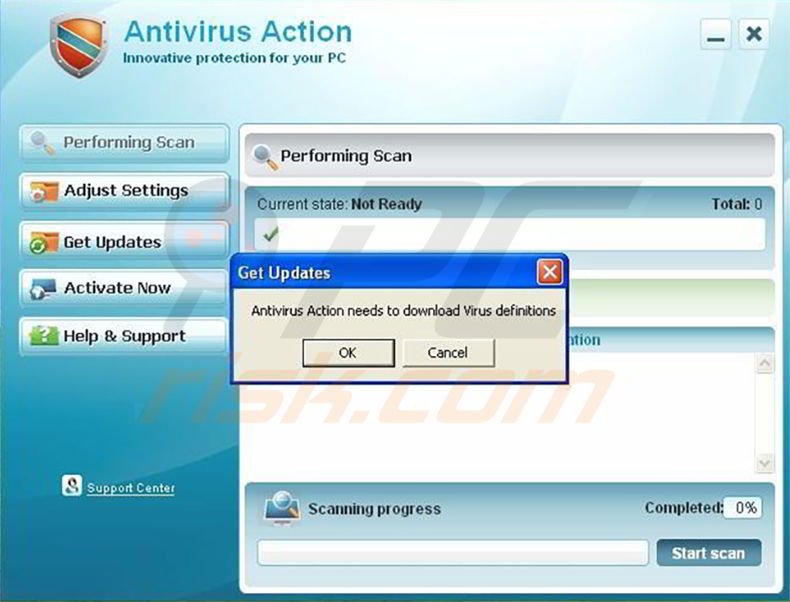
When Antivirus Action infects your computer it will perform fake virus scans and display fake security warnings. This rogue program runs automatically whenever you boot your operating system.
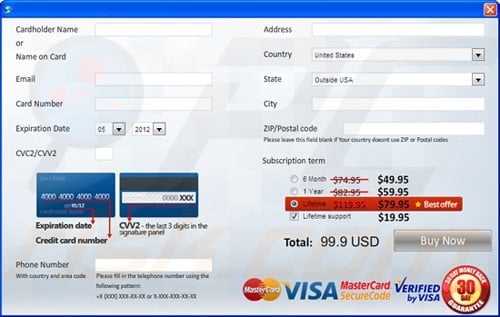
After running a scan, it will report the discovery of many infections and that you need to purchase the software in order to delete the threats. Do not purchase this program, it is a scam. Internet criminals hope that you will fall for their devious scheme designed to encourage you to purchase a license for Antivirus Action.
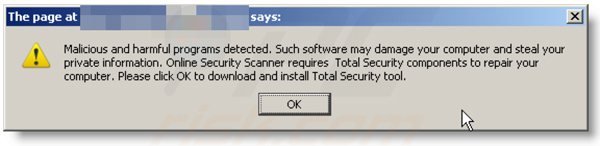
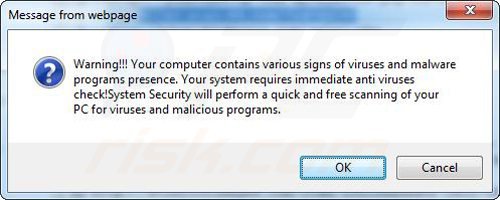
Do not consider doing so; you will loose your money and your PC will remain infected with this rogue program. The following security warnings may appear on your screen (these messages are generated by this rogue program and are fake - Antivirus Action generates them to scare you into believing that your PC is highly infected):
“Windows Security Alert Windows reports that your computer is infected. Antivirus software helps to protect your computer against viruses and other security threats. Click here to scan your computer. Your system might be at risk now.”
“Security Warning Application cannot be executed. The file notepad.exe is infected. Do you want to activate your antivirus software now?”
“Internet Explorer Warning - visiting this site may harm your computer! Most likely causes: The website contains exploits that can launch malicious code on your computer.”
“Suspicious network activity detected. There might be an active spyware program running on your computer.”
“Application cannot be executed. The file notepad.exe is infected. Do you want to activate your antivirus software now?”
“INFILTRATION ALERT. Your computer is being attacked by an Internet virus. It could be a password-stealing attack, Trojan Dropper, or similar.”
All of these security warnings are false. This is simply the method by which Antivirus Action attempts to fool users into purchasing the license.
If you have already purchased Antivirus Action, you should immediately contact your credit card company and cancel the transaction, explaining that you have been fooled into purchasing fake antivirus software.
Commonly, Antivirus Action is propagated via Trojans. If you have recently downloaded some relatively unknown video codecs, this could be the method by which this fake antivirus software infiltrated your system.
After Antivirus Action has infected your computer, it disables other legitimate security programs and this could lead to other attacks and infections. You should remove Antivirus Action immediately when detected on your system.
Antivirus Action is capable of infecting Windows 9x, 2000, XP, Vista, and Windows 7. Follow the removal instructions below to completely remove Antivirus Action.
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
▼ DOWNLOAD Combo Cleaner
By downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by Rcs Lt, the parent company of PCRisk.com read more.
Quick menu:
- What is Antivirus Action?
- STEP 1. Remove Antivirus Action using a software.
- STEP 2. Remove Antivirus Action using Safe Mode with Networking.
- STEP 3. Remove Antivirus Action manually by deleting files and registry entries.
Antivirus Action Removal
NOTE: Some spyware can block the downloading of spyware removers. If You cannot download the above remover using the default location, try one of the alternative download locations below:
- Location 1 (The file is renamed to "iexplore.exe", since most spyware does not block this file)
- Location 2
Antivirus Action manual removal
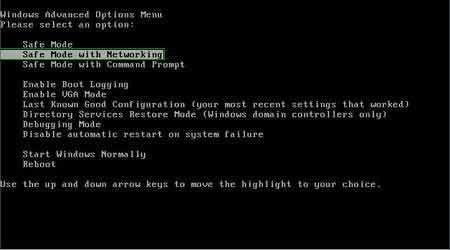
1. Start your computer in Safe Mode. Click Start, click Shut Down, click Restart, click OK. During your computer starting process press the F8 key on your keyboard multiple times until you see the Windows Advanced Option menu, then select Safe Mode with Networking from the list.
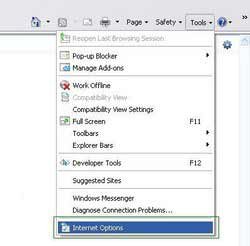
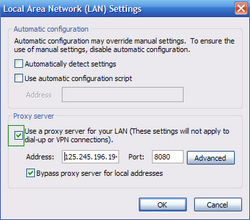
2. Open Internet Explorer, click Tools, and select Internet Options. Select Connections, then click LAN settings, if 'Use a proxy server for your LAN' is checked, uncheck it and press OK.


3. Download HijackThis and save it to your desktop. Some malicious programs are able to block HijackThis, so when you click the download link, in the Save dialog, rename HijackThis.exe to iexplore.exe and only then click the Save button. After saving the file to your desktop, double click it. In the main HijackThis window click the “Do a system scan only” button. Select the following entry (place a tick at the left of the entry):
O4 – HKLM\..\Run: [audpdogk] c:\docume~1\user\locals~1\temp\akotrowvc\bcgcihiagnz.exe
O4 – HKCU\..\Run: [audpdogk] c:\docume~1\user\locals~1\temp\akotrowvc\bcgcihiagnz.exe
After selecting the required entry, click "Fix Checked". After this procedure you can close HijackThis and proceed to the next removal step.
4. Download Hitman Pro (30 day trial) and run a scan, and then download and install a legitimate spyware remover (you can use the download button below) to completely remove the infection.
NOTE: Some spyware can block the downloading of spyware removers. If You cannot download the above remover using the default location, try one of the alternative download locations below:
- Location 1 (The file is renamed to "iexplore.exe", since most spyware does not block this file)
- Location 2
Additional information:
If you are unable to remove Antivirus Action, you can use these manual removal instructions. Use them at your own risk, since if you do not have strong computer knowledge, you could harm your operating system. Use them only if you are an experienced computer user. (Instructions on how to end processes, remove registry entries...)
End these Antivirus Action processes:
%UserProfile%Local SettingsApplication Data[random characters][random characters]agnz.exe
Remove these Antivirus Action registry entries:
HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionInternet Settings "ProxyOverride" = ""
HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionInternet Settings "ProxyServer" = "http=127.0.0.1:33921"
HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionInternet Settings "ProxyEnable" = "1"
HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionRun "[random characters] gnz.exe"
HKEY_LOCAL_MACHINESOFTWAREMicrosoftWindowsCurrentVersionRun "[random characters]agnz.exe"
HKEY_CURRENT_USERSoftwareAntivirus Action
HKEY_LOCAL_MACHINESoftwareMicrosoftWindowsCurrentVersionRun “Antivirus Action”
HKEY_LOCAL_MACHINESOFTWAREMicrosoftWindowsCurrentVersionUninstallAntivirus Action
HKEY_CURRENT_USERSoftware[random characters]
HKEY_CURRENT_USERSoftwareMicrosoftInternet ExplorerPhishingFilter "Enabled" = "0"
Delete these Antivirus Action files:
%Documents and Settings%All UsersStart MenuProgramsAntivirus Action %Documents and Settings%All UsersDesktopAntivirus Action.lnk %Documents and Settings%All UsersApplication DataAntivirus Action %UserProfile%Local SettingsApplication Data[random characters][random characters]agnz.exe
Summary:
The fake antivirus programs (also known as "rogue antivirus programs" or "scareware") are applications that tries to lure computer users into paying for their non-existent full versions to remove the supposedly detected security infections (although the computer is actually clean). These bogus programs are created by cyber criminals who design them to look as legitimate antivirus software. Most commonly rogue antivirus programs infiltrate user's computer using poop-up windows or alerts which appear when users surf the Internet. These deceptive messages trick users into downloading a rogue antivirus program on their computers. Other known tactics used to spread scareware include exploit kits, infected email messages, online ad networks, drive-by downloads, or even direct calls to user's offering free support.
A computer that is infected with a fake antivirus program might also have other malware installed on it as rogue antivirus programs often are bundled with Trojans and exploit kits. Noteworthy that additional malware that infiltrates user's operating system remains on victim's computer regardless of whether a payment for a non-existent full version of a fake antivirus program is made. Here are some examples of fake security warning messages that are used in fake antivirus distribution:
Computer users who are dealing with a rogue security software shouldn't buy it's full version. By paying for a license key of a fake antivirus program users would send their money and banking information to cyber criminals. Users who have already entered their credit card number (or other sensitive information) when asked by such bogus software should inform their credit card company that they have been tricked into buying a rogue security software. Screenshot of a web page used to lure computer users into paying for a non-existent full version of antivirus action rogue and other rogue antivirus programs:
To protect your computer from antivirus action rogue and other rogue antivirus programs users should:
- Keep their operating system and all of the installed programs up-to-date.
- Use legitimate antivirus and anti-spyware programs.
- Use caution when clicking on links in social networking websites and email messages.
- Don't trust online pop-up messages which state that your computer is infected and offers you to download security software.
Symptoms indicating that your operating system is infected with a fake antivirus program:
- Intrusive security warning pop-up messages.
- Alerts asking to upgrade to a paid version of a program to remove the supposedly detected malware.
- Slow computer performance.
- Disabled Windows updates.
- Blocked Task Manager.
- Blocked Internet browsers or inability to visit legitimate antivirus vendor websites.
If you have additional information on antivirus action rogue or it's removal please share your knowledge in the comments section below.
▼ Show Discussion