Ignore the I am a professional programmer who specializes in hacking email scam
![]() Written by Tomas Meskauskas on (updated)
Written by Tomas Meskauskas on (updated)
What is I am a professional programmer who specializes in hacking email scam?
As a rule, scammers behind sextortion email scams claim to have hacked a computer and recorded recipients while they were visiting adult websites. Scammers threaten to publish the video/send it to other people, unless recipients pay a certain amount of Bitcoin to the provided wallet address.
Such emails have to be ignored - they are scams and videos (or other compromising material) that cybercriminals behind them claim to have do not exist.

The scammer behind this sextortion email scam introduces himself as a professional programmer who hacks into computers during his free time. He claims that he hacked the recipient's computer several months ago - he installed a virus that gave him full access to the infected computer.
He also claims that he used a connected webcam to record a video of a recipient while he was visiting some adult page (watching an adult video). The scammer threatens to send that video to all people on the recipient's contact list and social media if a recipient is not going to pay $1350 in Bitcoins to the provided BTC wallet within 48 hours after receiving this email.
There are many similar sextortion scams. Most of them are used to scare recipients into paying a certain amount of money to scammers so they would not spread a video or photo that does not exist. It is important to mention that scammers often use a spoofing technique to trick recipients into believing that their email account or a computer is hacked.
Spoofing technique allows scammers to change the email address of a sender. Typically, scammers make the sender's email address the same as the recipient's.
In one way or another, emails like this one can and should be ignored - scammers behind them do not have any compromising videos or photos.
| Name | I am a professional programmer who specializes in hacking email scam |
| Threat Type | Phishing, Scam, Social Engineering, Fraud |
| Fake Claim | Scammer has recorded compromising video |
| Ransom Size | $1350 in Bitcoins |
| Cyber Criminal Cryptowallet Address | 1NToziZKcJfyxHpwkcxbafwghGasme4NUf, 1MZ6avTVhzxsyZvyNxFVWMutZwjQUhLpYo |
| Symptoms | Unauthorized online purchases, changed online account passwords, identity theft, illegal access of the computer. |
| Distribution methods | Deceptive emails, rogue online pop-up ads, search engine poisoning techniques, misspelled domains. |
| Damage | Loss of sensitive private information, monetary loss, identity theft. |
| Malware Removal (Windows) | To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. |
As mentioned in the previous paragraph, there are many similar sextortion scams. A couple of examples are "I have got two not really pleasant news for you", "I have to share bad news with you", "Within 96 hours I'll ruin your prestige".
It is important to mention that email can be used as a channel not only to extract money (or personal information) but also to deliver malware.
A couple of examples of malspam campaigns are "KIO KOREA Email Virus" and "Socar Email Virus". Typically, they are used to distribute trojans, ransomware, and other malicious software.
How do spam campaigns infect computers?
When cybercriminals use email as a channel to deliver malware, they send malicious files or links designed to download such files. In one way or another, their main goal is to trick recipients into opening a file that is designed to install malicious software.
In order to trick users into opening malicious attachment/file, cybercriminals disguise their emails as important letters from legitimate companies or other entities. A couple of examples of files that cybercriminals usually use in their malspam campaigns are Microsoft Office documents, PDF documents, RAR, ZIP or other archive files, JavaScript files, executable files (like .exe).
Malicious documents opened with MS Office do not install malware unless users enable macros commands (editing/content). Although, malicious documents can install malware automatically if opened with the Microsoft Office version that was released before MS Office 2010 (older versions do not include the "Protected View" mode).
How to avoid installation of malware?
Emails sent from unknown, suspicious addresses should not be trusted. If such emails are not relevant and contain a link or an attachment, then it is likely that they came from cybercriminals who try to trick recipients into installing malware on their computers.
Also, software (and files) should be downloaded from official, trustworthy pages. It is common that Peer-to-Peer networks like torrent clients, eMule, various unofficial pages, third-party downloaders, and other sources of this kind are used to distribute unwanted, potentially malicious software.
Any installed programs must be updated, activated properly. It has to be done using functions or tools that their official developers provide.
Third-party, unofficial tools should never be used. It is common that they are used to distribute malware. Another reason not to use such tools is that it is not legal to activate licensed software with 'cracking' tools.
The operating system should be scanned for malware or any other threats regularly. It is advisable that it would be scanned with a reputable antivirus or anti-spyware software.
If you've already opened malicious attachments, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
Appearance of the email (GIF):

Text in this email:
Subject: Hackers have access to your device. Check details ASAP!
Hello there
Let me introduce myself first - I am a professional programmer, who specializes in hacking during my free time.
This time you were unlucky to become my next victim and I have just hacked the Operating System and your device.I have been observing you for several months.
To put things in a simple way, I have infected your device with my virus while you were visiting your favorite adult website.I will try to explain the situation in more details, if you are not really familiar with this kind of situations.
Trojan virus grants me with full access as well as control of your device.
Hence, I can see and access anything on your screen, switch on the camera and microphone and do other stuff, while you don't even know that.In addition, I also accessed your whole contacts list at social networks and your device too.
You may be questioning yourself - why didn't your antivirus detect any malicious software until now?
- Well, my spyware uses a special driver, which has a signature that is updated on a frequent basis, hereby your antivirus simply cannot catch it.
I have created a videoclip exposing the way you are playing with yourself on the left screen section, while the right section shows the porn video that you were watching at that point of time.
Few clicks of my mouse would be sufficient to forward this video to all your contacts list and social media friends.
You will be surprised to discover that I can even upload it to online platforms for public access.The good news is that you can still prevent this from happening:
All you need to do is transfer $1350 (USD) of bitcoin equivalent to my BTC wallet (if you don't know how to get it done,
do some search online - there are plenty of articles describing the step-by-step process).My bitcoin wallet is (BTC Wallet): 1NToziZKcJfyxHpwkcxbafwghGasme4NUf
Once I receive your payment, I will delete your kinky video right away, and can promise that is the last time you hear from.
You have 48 hours (2 days exactly) to complete the payment.
The read notification will be automatically sent to me, once you open this email, so the timer will start automatically from that moment.Don't bother trying to reply my email, because it won't change anything (the sender's email address has been generated automatically and taken from internet).
Don't try to complain or report me either, because all my personal information and my bitcoin address are encrypted as part of blockchain system.
I have done my homework.If I discover that you have tried forwarding this email to anyone, I will right away share your kinky video to public.
Let's be reasonable and don't make any stupid mistakes anymore. I have provided a clear step-by-step guide for you.
All you need to do is simply follow the steps and get rid of this uncomfortable situation once and for all.Best regards and good luck.
An Italian variant of "I Am A Professional Programmer Who Specializes In Hacking" spam email:

Text presented within:
Subject: Gli hackers hanno accesso al tuo dispositivo. Controlla i dettagli al più presto!
Salve,
Prima di tutto, lascia che mi presenti, faccio il programmatore di professione e mi occupo di hackeraggio nel mio tempo libero.
Stavolta sfortunatamente sei tu la vittima di turno, infatti ho appena hackerato il Sistema Operativo e il tuo dispositivo.Ti osservo da parecchi mesi.
In parole povere ho infettato il tuo dispositivo con il mio virus mentre stavi visitando il tuo sito per adulti preferito.Cercherò di spiegarti la situazione in maniera più dettagliata, se non conosci molto bene questo genere di cose.
Il virus Trojan mi consente l’accesso completo, oltre che il controllo del tuo dispositivo.
Quindi, posso vedere e accedere a qualsiasi cosa sul tuo schermo, accendere la videocamera e il microfono e fare altre cose, senza che tu te ne accorga nemmeno.Inoltre, ho anche avuto accesso alla lista dei tuoi contatti sulle tue reti social e sul tuo dispositivo.
Forse ti starai chiedendo perché il tuo antivirus non ha individuato nessun software dannoso fino a questo momento.
- Allora, il mio spyware usa un driver speciale, che ha una firma che viene aggiornata regolarmente, pertanto il tuo antivirus non riesce a beccarlo.
Ho creato un videoclip che fa vedere come ti trastulli sul lato sinistro dello schermo, mentre sulla parte destra c’è il video porno che stavi guardando in quel momento.
Basterebbero pochi clic del mouse per inoltrare questo video a tutti i tuoi contatti e agli amici dei social.
Sarai sorpreso di scoprire che potrei perfino caricarlo sulle piattaforme online accessibili pubblicamente.La buona notizia è che puoi evitare che tutto questo accada:
Non devi fare altro che trasferire l’equivalente in bitcoin di 1250 EUR al mio portafoglio BTC
(se non sai come si fa, svolgi qualche ricerca online – ci sono numerosi articoli che descrivono l’operazione step-by-step).Il mio portafoglio bitcoin è (BTC Wallet): 1PFwBwH1Cof2FcEhWY2EbZv5Y28TkLiXfU, 15vvkiEwZcTBuzqieWBcbJ6S83g7gcqry3
Una volta ricevuto il tuo pagamento, cancellerò immediatamente i tuoi video perversi, e ti prometto che non mi farò sentire mai più.
Hai 48 ore (2 giorni precisi) per completare il pagamento.
Nel momento in cui aprirai questa e-mail mi sarà inviata automaticamente la notifica di lettura e da quel momento si avvierà il timer.Non disturbarti a cercare di rispondermi, perché non cambierà nulla (l’indirizzo e-mail del mittente è stato generato automaticamente e preso da Internet).
Non provare nemmeno a sporgere denuncia, perché tutti i miei dati personali e il mio indirizzo bitcoin sono crittografati come parte di un sistema di blockchain.
Ho pensato a tutto.Se scopro che hai cercato di inoltrare questa e-mail a chiunque, renderò pubblico il tuo video perverso.
Cerca di essere ragionevole e di non commettere più errori stupidi. Ti ho fornito una guida passo-passo.
Devi semplicemente seguire i passaggi per sbarazzarti definitivamente di questa situazione spiacevole.Saluti e buona fortuna.
A Czech variant of "I Am A Professional Programmer Who Specializes In Hacking" scam email:

Text presented within:
Subject: Hackeři získali přístup k tvému zařízení. Přečti si zavčas podrobné informace!
Ahoj,
Dovol, abych se ti ze všeho nejdřív představil – jsem profesionální programátor, který se ve svém volném čase zabývá hackováním.
Ke své velké smůle ses stal mojí další obětí, které jsem se právě naboural do zařízení a jeho operačního systému.Sleduji tě již několik měsíců.
Zjednodušeně řečeno, zatímco jsi navštěvoval své oblíbené erotické webové stránky, implementoval jsem do tvého zařízení virus.Pokud ses se situací tohoto typu ještě nikdy nesetkal, pokusím se ti vše podrobně vysvětlit.
Plný přístup a kontrolu nad tvým zařízením jsem získal díky trojskému koni.
Proto, aniž bys o tom měl tušení, vidím a mohu přistupovat ke všemu, co vidím na tvém monitoru a můžu aktivovat tvou webkameru, mikrofon a další zařízení.Kromě toho jsem získal také přístup ke kompletnímu seznamu tvých kontaktů na sociálních sítích a také k tvému zařízení.
Možná se teď sám sebe ptáš – proč ale můj antivirus dosud žádný škodlivý software nedetekoval?
- No je to proto, že můj spyware využívá speciální ovladač s pravidelně aktualizovaným podpisem, takže ho tvůj antivirový program nedokáže tak snadno zachytit.
Vytvořil jsem videoklip, v jehož levé části je zachyceno, jak se věnuješ sebeukájení, zatímco v té pravé se přehrává porno video, které jsi při tom v daný moment sledoval.
Stačilo by mi jen několik málo kliknutí myší, abych tento klip přeposlal všem tvým kontaktům a přátelům ze sociálních sítí.
A budeš překvapen, až zjistíš, že jsem ho dokonce zveřejnil na veřejně přístupných internetových platformách.Dobrou zprávou je, že tomu můžeš pořád ještě zabránit:
Stačí převést bitcoinový ekvivalent v hodnotě 25000 Kč do mé BTC peněženky
(pokud nevíš, jak to udělat, veškeré informace si můžeš dohledat online – na internetu najdeš celou řadu článků popisujících tento postup hezky krok za krokem).Moje bitcoinová peněženka je (BTC peněženka): bc1qv4cvcs5l7jv8rcmr3z63snkq3nvfcrkwpu8n9g, 19ss2nD4jUc8vmLUiBCVTYbe5wunUxVgwu, 1M2ptT3eBGX2QVgirxDFcyGV9A81Vy4VpH
Jakmile platbu obdržím, okamžitě tvé hanbaté video smažu a slibuju ti, že už o mně nikdy více neuslyšíš.
Na dokončení platby máš 48 hodin (přesně 2 dny).
Po otevření tohoto emailu mi bude automaticky odesláno potvrzení o jeho přečtení a ihned poté se spustí časový odpočet.Neobtěžuj se pokoušet se na můj email odpovídat, protože to stejně k ničemu nepovede (emailová adresa odesílatele byla totiž vygenerována automaticky a byla pouze převzata z internetu).
Nesnaž se ani podávat na mě stížnost nebo cokoliv hlásit, neboť veškeré mé osobní údaje i bitcoinová adresa jsou šifrovány jako součást systému blockchain.
Svůj domácí úkol jsem zkrátka splnil do posledního puntíku.Jestliže zjistím, že jsi se pokusil tento email komukoliv přeposlat, okamžitě tvé úchylné video zveřejním.
Buďme rozumní a vyhněme se všem zbytečným chybám.
Poskytl jsem ti srozumitelného průvodce, který tě celým procesem krok za krokem provede a vše, co musíš udělat ty, je pouze držet se jeho pokynů a jednou provždy se tak této nepříjemné situace zbavit.Zdravím tě a přeji hodně štěstí.
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
▼ DOWNLOAD Combo Cleaner
By downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by Rcs Lt, the parent company of PCRisk.com read more.
Quick menu:
- What is I Am A Professional Programmer Who Specializes In Hacking spam?
- Types of malicious emails.
- How to spot a malicious email?
- What to do if you fell for an email scam?
Types of malicious emails:
![]() Phishing Emails
Phishing Emails
Most commonly, cybercriminals use deceptive emails to trick Internet users into giving away their sensitive private information, for example, login information for various online services, email accounts, or online banking information.
Such attacks are called phishing. In a phishing attack, cybercriminals usually send an email message with some popular service logo (for example, Microsoft, DHL, Amazon, Netflix), create urgency (wrong shipping address, expired password, etc.), and place a link which they hope their potential victims will click on.
After clicking the link presented in such email message, victims are redirected to a fake website that looks identical or extremely similar to the original one. Victims are then asked to enter their password, credit card details, or some other information that gets stolen by cybercriminals.
![]() Emails with Malicious Attachments
Emails with Malicious Attachments
Another popular attack vector is email spam with malicious attachments that infect users' computers with malware. Malicious attachments usually carry trojans that are capable of stealing passwords, banking information, and other sensitive information.
In such attacks, cybercriminals' main goal is to trick their potential victims into opening an infected email attachment. To achieve this goal, email messages usually talk about recently received invoices, faxes, or voice messages.
If a potential victim falls for the lure and opens the attachment, their computers get infected, and cybercriminals can collect a lot of sensitive information.
While it's a more complicated method to steal personal information (spam filters and antivirus programs usually detect such attempts), if successful, cybercriminals can get a much wider array of data and can collect information for a long period of time.
![]() Sextortion Emails
Sextortion Emails
This is a type of phishing. In this case, users receive an email claiming that a cybercriminal could access the webcam of the potential victim and has a video recording of one's masturbation.
To get rid of the video, victims are asked to pay a ransom (usually using Bitcoin or another cryptocurrency). Nevertheless, all of these claims are false - users who receive such emails should ignore and delete them.
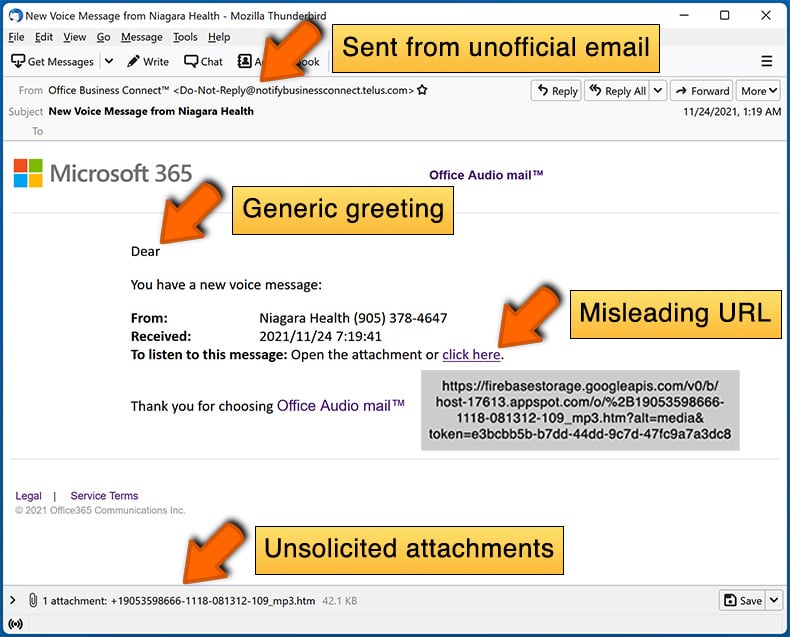
How to spot a malicious email?
While cyber criminals try to make their lure emails look trustworthy, here are some things that you should look for when trying to spot a phishing email:
- Check the sender's ("from") email address: Hover your mouse over the "from" address and check if it's legitimate. For example, if you received an email from Microsoft, be sure to check if the email address is @microsoft.com and not something suspicious like @m1crosoft.com, @microsfot.com, @account-security-noreply.com, etc.
- Check for generic greetings: If the greeting in the email is "Dear user", "Dear @youremail.com", "Dear valued customer", this should raise suspiciousness. Most commonly, companies call you by your name. Lack of this information could signal a phishing attempt.
- Check the links in the email: Hover your mouse over the link presented in the email, if the link that appears seems suspicious, don't click it. For example, if you received an email from Microsoft and the link in the email shows that it will go to firebasestorage.googleapis.com/v0... you shouldn't trust it. It's best not to click any links in the emails but to visit the company website that sent you the email in the first place.
- Don't blindly trust email attachments: Most commonly, legitimate companies will ask you to log in to their website and to view any documents there; if you received an email with an attachment, it's a good idea to scan it with an antivirus application. Infected email attachments are a common attack vector used by cybercriminals.
To minimise the risk of opening phishing and malicious emails we recommend using Combo Cleaner Antivirus for Windows.
Example of a spam email:
What to do if you fell for an email scam?
- If you clicked on a link in a phishing email and entered your password - be sure to change your password as soon as possible. Usually, cybercriminals collect stolen credentials and then sell them to other groups that use them for malicious purposes. If you change your password in a timely manner, there's a chance that criminals won't have enough time to do any damage.
- If you entered your credit card information - contact your bank as soon as possible and explain the situation. There's a good chance that you will need to cancel your compromised credit card and get a new one.
- If you see any signs of identity theft - you should immediately contact the Federal Trade Commission. This institution will collect information about your situation and create a personal recovery plan.
- If you opened a malicious attachment - your computer is probably infected, you should scan it with a reputable antivirus application. For this purpose, we recommend using Combo Cleaner Antivirus for Windows.
- Help other Internet users - report phishing emails to Anti-Phishing Working Group, FBI’s Internet Crime Complaint Center, National Fraud Information Center and U.S. Department of Justice.

▼ Show Discussion