Hackers Attack SWIFT Penetrate System 2nd Time
Hackers have for the second time stolen money from banks using the SWIFT payment system. Now we have some technical details about the first attack.
Usually when hacking news breaks the technical details are not given to the public. Often law enforcement tells the victim to keep those secret. Yet the security community operates in the opposite direction, believing by publishing the details of hacking that other people can protect against those methods. So we explain that here.
SWIFT
SWIFT is the decades old payment system that banks use to write transfer money to each other. It is several orders of magnitude larger than something for consumer use like PayPal. SWIFT is what companies use to move hundreds of millions of dollars around and governments use to make bond payments.
In February hackers convinced the New York Federal Reserve Bank to wire $81 million to a bank in Bangladesh. The Feb was curious about that transaction so they contacted the bank who initiated the transaction to verify that. Hackers made it look like the bank gave its approval.
The Fed is part of the US government and not a private bank. The dominate the US federal financial system and is some regards the financial system for the whole world. So that they were tricked says a lot.
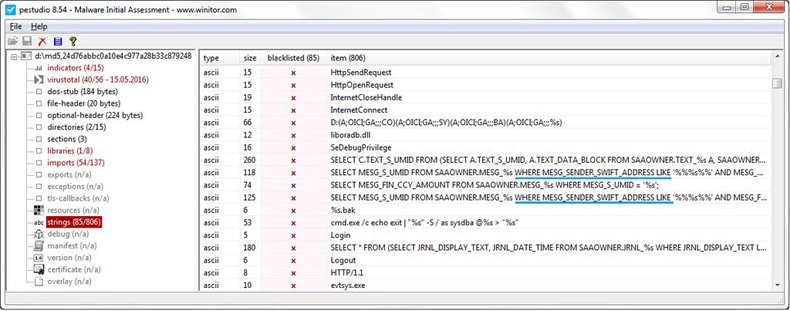
To fake the approvals, hackers planted malware into a PDF reader/writer program that the bank uses to process those. No one said whether that program was Adobe. The malware changed the denial typed into the PDF program to an approval and, poof, $81 million disappeared.
That is incredibly sophisticated.
The hackers also planted malware into the device driver of a printer. The Bangladesh bank also uses a manual printing process to approve transactions. So the hackers added text to the document sent to the printer to show that the transaction was approved and not denied. That too shows a level of sophistication suggesting that a criminal gang is behind this.
The money was wired and then disappeared into bank accounts across the Philippines where such money is usually laundered through casinos there as that can be turned into cash.
Hackers Pull off Second Heist
Now hackers have launched another attack against SWIFT, reports The New York Times. SWIFT is not saying who the victim is.
It would be incorrect to say that hackers have successfully hacked SWIFT. That system runs across private networks and is not attached to the internet. But what the hackers did in both bank heists is they attacked the computers at the endpoint that connect to SWIFT. In other words they went after someone’s desktop PC.

Inside Job
Security researchers have speculated that the this was an inside job as the hackers initiated the wire transfer using valid SWIFT credentials. Plus they knew to a high degree of detail the internal procedures of the bank.
All of this has caused SWIFT to push back against bad publicity and a potential panic by issuing statements. That’s the most important payment transfer system in the word. If hackers can attack that then banks could chose to go back to sending cash physically by having people fly all over the world with paper checks.
The New York Times sounded an ominous warning suggesting this could happen again when they write, “The crime appears to be part of a broad online attack on global banking.”
Looming New Threat
There’s not much that antivirus or other defensive software can do if hackers have paid inside employees to participate in their crime. Hackers in this situation are going after developing nations where there might be more corruption and less effective police and cybersecurity.
When newspapers first wrote about the Bangladesh attack they noted that the bank used a “$10 router.” But that by itself does not make the bank insecure. The main weakness there probably was a breakdown in internal controls. All of this highlights the need to review those frequently.
Also it would have worked better if the bank was using some kind of two-factor authentication. I worked on a a computer programming project at Wells Fargo Bank in the USA on two different occasions. The wire transfer payment system there was called Commercial Electronic Office. Only business customers could use that system to make wire transfers. They were required to use a RSA SecurID key fob to login to the system. That is a physical device. Hackers would not have had that even if they had stolen credentials.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion