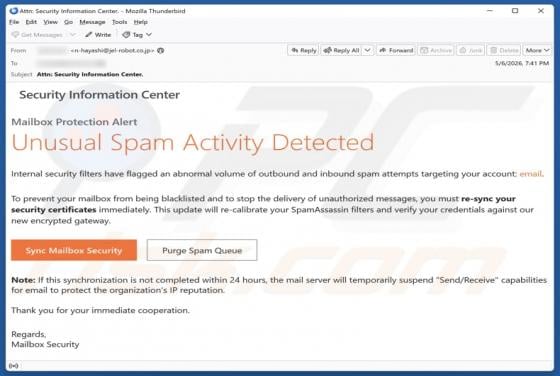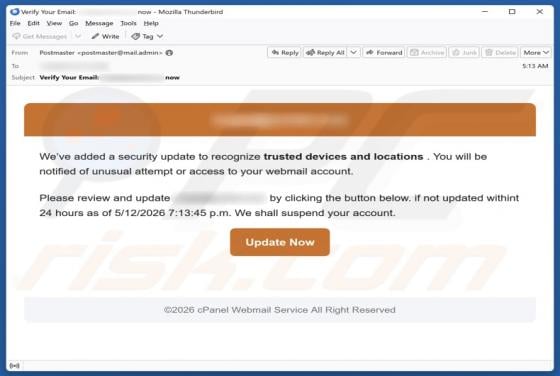
Security Update To Recognize Trusted Devices And Locations Email Scam
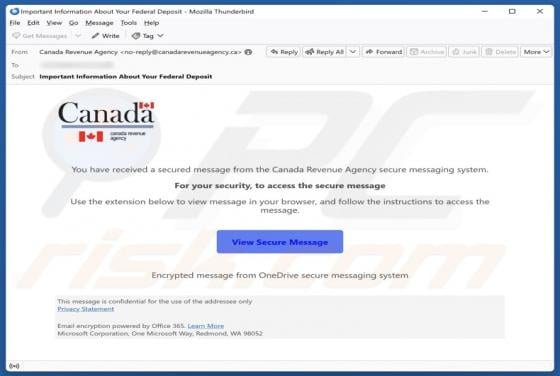
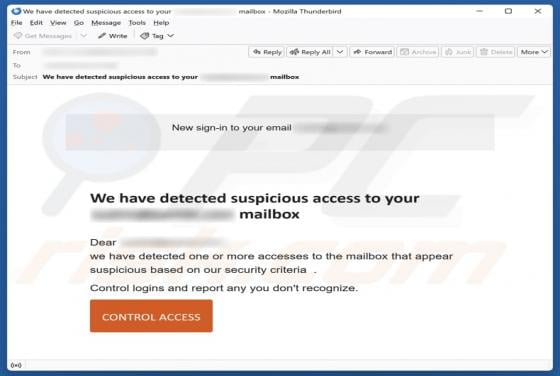
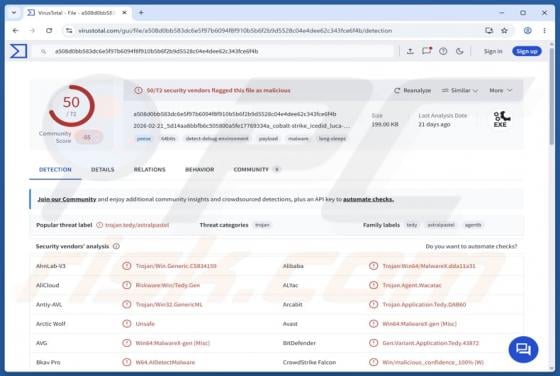
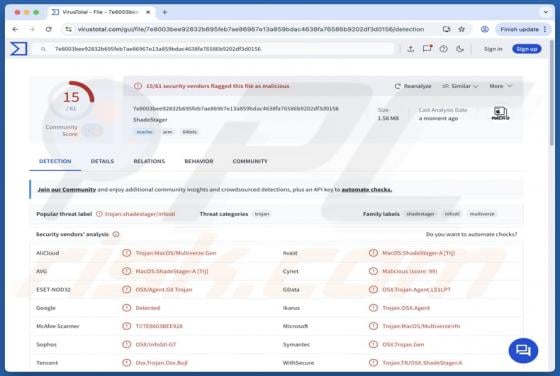
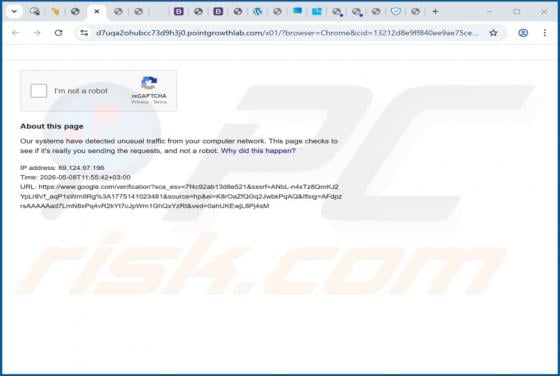
Our inspection has revealed that this is a scam email posing as a security-related notification from the email service provider. Its purpose is to lure recipients into a fraudulent page designed to pilfer personal information. Stolen details can be used to hijack personal accounts and for other ma