Myfocalfind.com Redirect
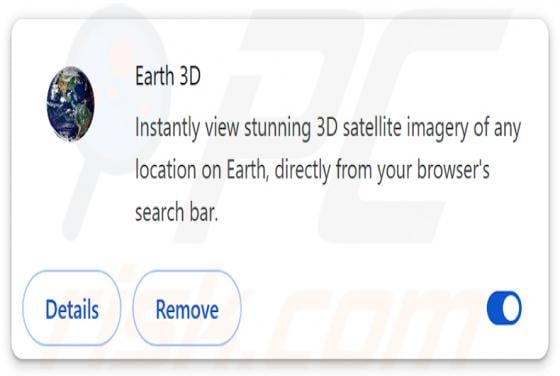
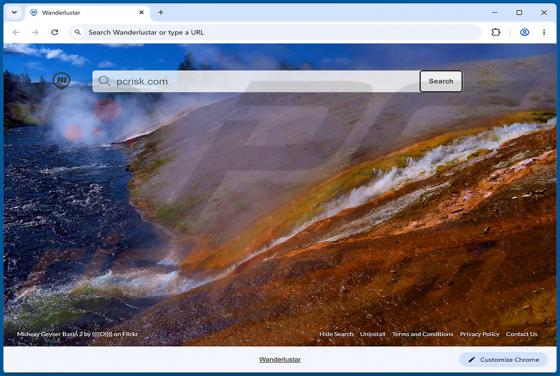
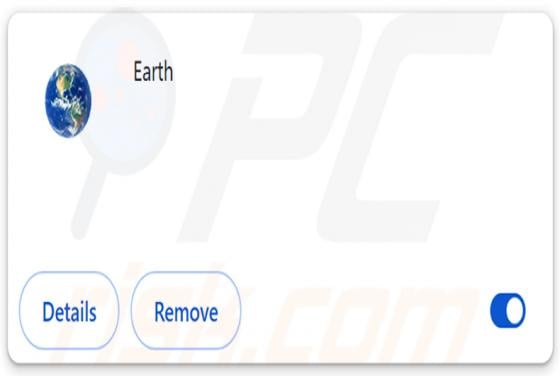
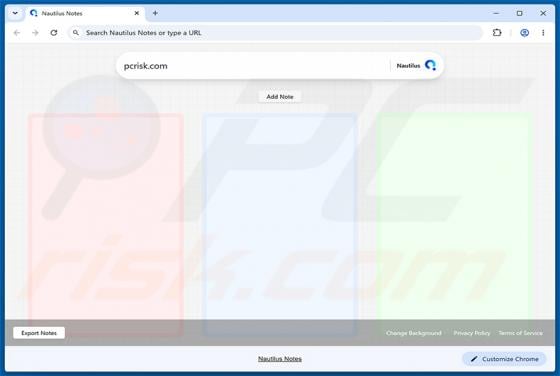
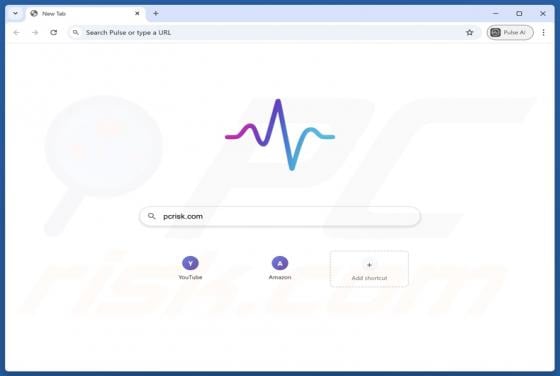
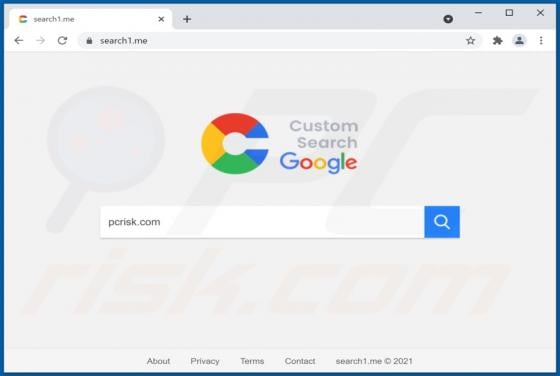
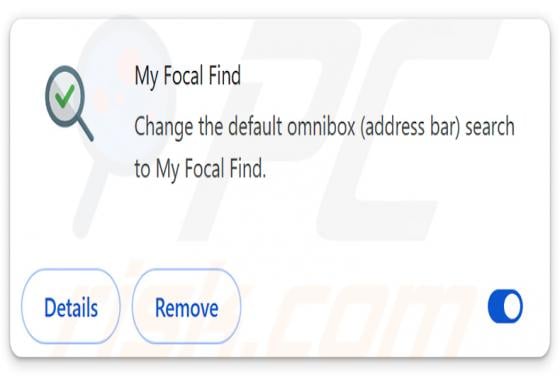
Our researchers found My Focal Find while analyzing a rogue installation setup and noticed that it has the traits of a browser hijacker. Once added to a browser, this extension changes its settings to promote myfocalfind.com, a fake search engine. This article explains what My Focal Find does, ho