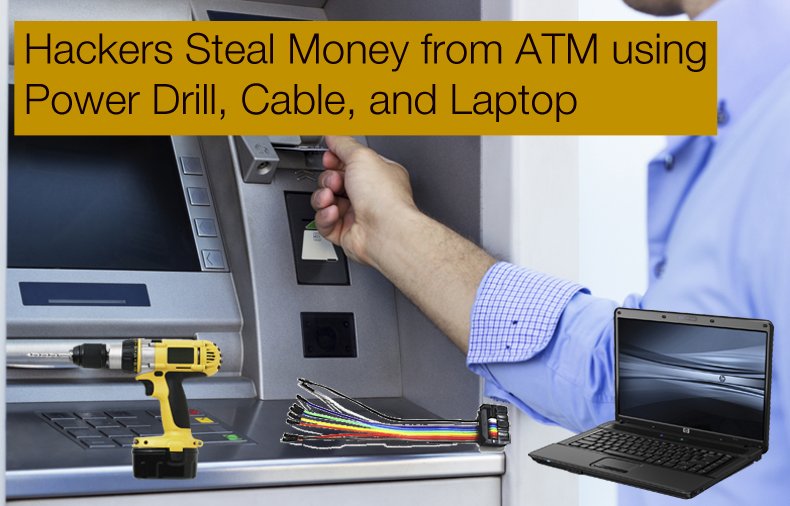
Hackers Steal Money from ATM using Power Drill, Cable, and Laptop
Last year hackers were caught on camera using their smartphones to empty ATMs. The thieves stole $2.2 million USD before they fled the country. Nixdorf, the ATM maker, said three different strains of malware were found on the devices. Software on the smartphone enabled the malware.
Security researchers speculated how the hackers were able to load the malware. Some said that networking devices on the device have well-known default passwords. Another said all you needed to do was attach a USB device and boot from that.
Now hackers have done some variation of both by drilling an 8 cm hole into the front and then passing a cable inside and connecting that to a 10-pin connector. They then connect the cable to a computer and send instructions that causes the machine to dispense cash.
Security researchers showed how the hackers probably figured out how to decrypt the network protocol used on the device. The researchers used a logic analyzer and oscilloscope to find that the encryption was very simple to break. It was a simple XOR cipher. Or they could have used any of the many ATM technical manuals that have been leaked online, like this one from NCR.
Elsewhere in the world, hackers have stolen cash from ATMs using other approaches that have largely gone away due to hardening measures taken by banks and by arrests gangs that had been travelling around the world doing this. First, they were filling the machines with compressed air until they burst open.
That took some while to perfect as at first the hackers blew up the cash as well. Then hackers replaced the ATM card reader with their own card reader. Then they installed tiny cameras to record the pin when bank customers took out their cash.
But those techniques, largely used in developing nations, do not work so well without a lot of boots on the ground, because the amount that you can withdraw from an ATM in many poorer countries is limited to a few hundred dollars to limit ATM gunpoint holdups.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion