BlackWallet DNS Hijacked…Again
Cryptocurrencies make news headlines at a near daily rate. Often they concern whether Bitcoin is about to reach a new high or the bubble is about to burst. Unfortunately, it seems they make the headlines just as often when it comes to hackers stealing funds from crypto wallets. While many nations have begun debating the dangers surrounding cryptocurrencies, or at the very least what they perceive as the dangers, continued headlines stating how money is stolen can do little for the technology that many have gotten excited about.
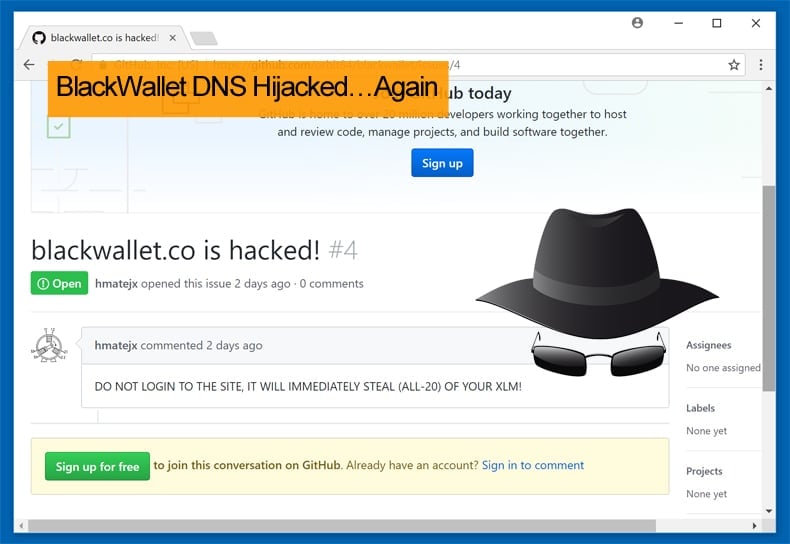
On Saturday, January 13, another instance of a hack came to light. This time an unknown hacker, or hacker group, managed to hijack the DNS (Domain Name Server) for BlackWallet.co, a web-based wallet application for the Stellar Lumen cryptocurrency (XLM). The hacker managed to steal over $400,000 from users' accounts.
DNS hijacking is a type of malicious attack in which an individual redirect queries to a domain name server (DNS), by overriding a computer’s TCP/IP settings. This can be achieved through the use of malicious software or by modifying a server’s settings. Once the individual or individuals performing the DNS hijacking have control of the DNS, they can use it to direct traffic to different websites. There is actually two main types of DNS hijacking. The first being, DNS hijackings that involve infecting computers with malware or DNS trojan attack on software, which instructs computers to no longer translate the user-friendly domain names to the correct corresponding IP addresses but rather the domain determined by the attacker. The second type of DNS hijacking involves hacking certain websites and literally having their DNS addresses changed so that visitors from these websites end up visiting completely different destinations online. The second type is most likely the one suffered by BlackWallet and their legitimate users.
What is known about Saturday’s incident?
Even before BlackWallet employees were able to regain access to their domain while they took down their site, security researcher Kevin Beaumont had analyzed the code. He concluded that “The DNS hijack of Blackwallet injected code…If you had over 20 Lumens it pushes them to a different wallet,” While employees were unaware of what had happened the hacker had made off with 669,920 Lumens. At the time of writing that amounts to 424,936.29 USD.
Given the nature of cryptocurrencies and their associated wallets, the hackers wallet is available to be viewed publicly. The attackers' wallet is located at the "GBH4TZYZ4IRCPO44CBOLFUHULU2WGALXTAVESQA6432MBJMABBB4GIYI" address. While the hackers wallet address is known determining who is behind the attack is incredibly difficult due to the ability to register a wallet anonymously. The BlackWallet team and other XLM owners have tried to warn users via alerts on Reddit, Twitter, GitHub, the Stellar Community and GalacticTalk forums. Despite the numerous warnings users continued to log into the rogue BlackWallet.co domain, enter their credentials, and then see funds mysteriously vanish from their wallets much to their horror.
The Race to Launder the Funds has begun
As of a few hours ago, the attacker started moving funds from the XLM account to Bittrex. Bittrex is a cryptocurrency exchange where the hacker would be able to convert the stolen funds into another digital currency to hide their tracks. As a result, BlackWallet admins are now desperately trying to catch Bittrex's attention to block the hackers' account. According to the BlackWallet admin, the incident took place after someone accessed his hosting provider account. The admin released a statement on Reddit late on Sunday night, within in it the admin took the time to state that, “I am in talks with my hosting provider to get as much information about the hacker and will see what can be done with it,” further it was added, “If you ever entered your key on blackwallet, you may want to move your funds to a new wallet using the stellar account viewer…Please note however that blackwallet was only an account viewer and that no keys were stored on the server!”
BlackWallet’s Recent Security History
In July 2017, BlackWallet warned its users that it had been hacked in a similar fashion. Little is known of those hacks except for BlackWallet’s announcement warning its users they may have their Lumen stolen if they log into the website. It is not only BlackWallet who has been a target for hackers, EtherDelta suffered a similar DNS hijacking incident before Christmas 2017. Classic Ether Wallet and the Etherparty ICO website also suffered DNS hijackings.
Given that wallets are prime targets for hackers, users can institute the following best practices to help keep their funds safe:
- Securing your software wallet is similar to protecting any data on your computer. You have to be a little more paranoid while browsing the Internet, clicking on links and email attachments.
- Mobile users may take advantage of Google authenticator with a single IP in its whitelist, which should be the VPN to access the online exchange.
- It is important to select an exchange that is not only flexible and easy to use but also reputable and secure. Try to follow the news. If industry leaders disengage from a project it should be a worrying signal. Repeated technical problems and strange policies are additional points of concern. Bitcoin withdrawal difficulties will always be a red flag also.
- Do create backups. Kept in a secure place, a backup of your cryptocurrency wallet may save you from hardware failures and a lot of human slipups. It will also let you restore your wallet in case your PC or telephone gets stolen.
- Encrypting the wallet or your hole device enables you to create a password for those attempting to take out any money.
- Although passwords and encryption can protect from thieves, it is not able to put a stop to key-loggers or another malware. It is important to install and keep up-to-date leading antivirus and antimalware solutions. Many of them are free to use.
- Prior to creating an account on any exchange, set up a new email box that you will be using for that specific exchange account.
- Be sure to choose a very difficult and lengthy password, desirably a passphrase. Write it down on paper and store that piece of paper in a secret place.
- Turn on two-factor-authorization not only for login but for any transaction procedures.
- While on social media or forums, do not mention what cryptocurrency exchange or wallet you use.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion