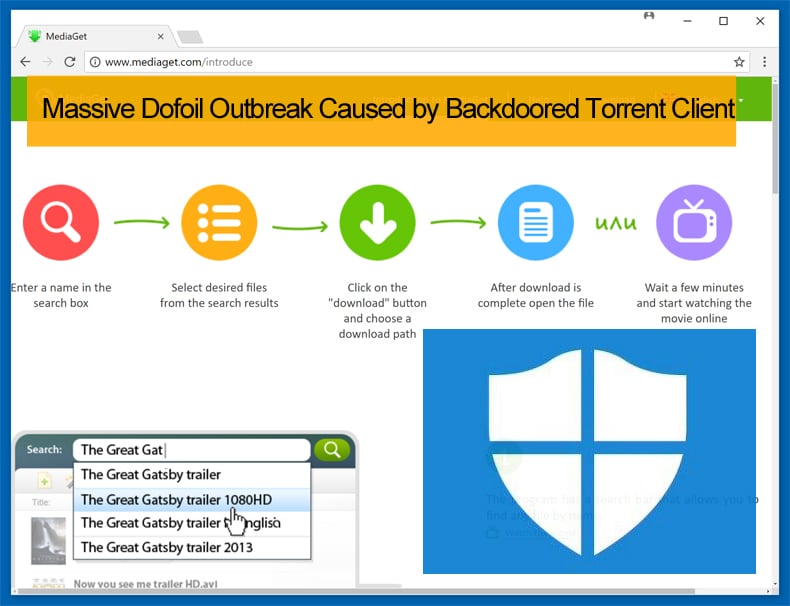
Massive Dofoil Outbreak Caused by Backdoored Torrent Client
On March 7, Microsoft released a report detailing that Windows Defender AV detected and thwarted a massive outbreak of the Dofoil, sometimes referred to as Smoke Loader, trojan. The campaign attempted to infect over 400,000 users in a 12-hour window. The campaign targeted mainly Russian users but instances were detected in the Ukraine and Turkey. Russia made up the vast majority of detected instances with 73% followed by Turkey which accounted for 18% and Ukraine on 4%. On March 13, Microsoft released a follow-up report explaining that the attack was caused by backdoored Russian-based BitTorrent client named MediaGet.
Details Discovered in the Initial Report
In the report released on March 7 researchers at Microsoft explained that Windows Defender AV initially flagged the attack’s unusual persistence mechanism through behavior monitoring, a system that works in conjunction with machine learning to better detect and prevent malware outbreaks. Such an AI-based pre-emptive protection provided against this attack is similar to how layered machine learning stopped an Emotet outbreak last month. Windows explained the system worked as follows:
1. “Within milliseconds, multiple metadata-based machine learning models in the cloud started blocking these threats at first sight.
2. Seconds later, our sample-based and detonation-based machine learning models also verified the malicious classification. Within minutes, detonation-based models chimed in and added additional confirmation.
3. Within minutes, an anomaly detection alert notified us about a new potential outbreak.
4. After analysis, our response team updated the classification name of this new surge of threats to the proper malware families. People affected by these infection attempts early in the campaign would have seen blocks under machine learning names like Fuery, Fuerboos, Cloxer, or Azden. Later blocks show as the proper family names, Dofoil or Coinminer.”
While the response and effective handling of the outbreak is indeed impressive, it is in the researcher's analysis that matters get really interesting. While Dofoil is traditionally considered a trojan what made this attack unique was that the trojan was coupled with a coin miner. This variant of Dofoil used a code injection technique called process hollowing which involves spawning a new instance of a legitimate process and then replacing the legitimate code with the malware in question. With this variant, the now hollowed explorer.exe process then spins up a second malicious instance, which drops and runs a coin mining malware masquerading as a legitimate Windows binary, wuauclt.exe.
The miner itself is a customized miner which supports NiceHash. This means that it can mine different cryptocurrencies. The initial samples analyzed mined Electroneum coins. In order for a coinminer to be successful, it has to be persistent and avoid detection, the miner in this instance modifies the registry in an attempt to remain undetected. To do this the hollowed explorer.exe process creates a copy of the original malware in the Roaming AppData folder and renames it to ditereah.exe. Once that is complete it then creates a registry key or modifies an existing one to point to the newly created malware copy.
The Second Report Detailing How the Attack was Carried Out
While the first report went into great detail how the attack was prevented and the characteristics of the Dofoil variant, almost nothing was mentioned about how the attack was carried out. In the second report, the researchers at Windows contend that Dofoil malware landed on users' computers via a file named my.dat, created by mediaget.exe, the MediaGet BitTorrent client's binary. The researchers also determined that the attack carried out on March 6 was a carefully planned affair with the foundations been laid out in the middle of February.
It was further discovered that hackers broke into MediaGet's infrastructure, and sometimes between February 12 and 19, attackers managed to replace the official MediaGet installer with one that also included the backdoor. The hackers then waited for two weeks to ensure that users would download or update the installer with the backdoor.
As with the coinminer, the hackers paid careful attention in how to hopefully avoid detection. With the attack, the hackers used a stolen digital certificate to sign the malicious MediaGet update to avoid detection. While this is a cunning way of avoiding detection that has been used successfully in the past, the hackers signed the certificate as a third-party software company unrelated to MediaGet, and this proves MediaGet’s innocence and being a victim of such abuse.
Supply Chain Attacks are Frightfully Efficient and Effective
Although this attack was thwarted by Microsoft and their Windows Defender AV, it still illustrates the damage that can be caused by such an attack. These attacks are called Supply Chain Attacks by security researchers and such attacks can be defined as an attack that occurs when someone infiltrates a system via an outside partner or provider. This leaves the system ready to exploit like in the above example the hackers used a legitimate installer to spread their malware variant. This style of attack is becoming increasingly popular as attackers have more resources and tools at their disposal than ever before thanks to leaks and the accessibility of purchasing such tool on the Dark Web. Part of the reason such attacks are efficient and effective is users will update or download software packages without a thought as they trust the source the software comes from. This, in turn, means that the hacker now essentially has access to the software’s user base without relying on spam or phishing email campaign.
Last year the globe saw a Supply Chain Attack that was not successfully prevented. That was the NotPetya attack which was carried out via a tainted update for M.E.Doc, a Ukrainian accounting software program. Another example of a Supply Chain Attack was the Target data breach which occurred in 2014. In the past, other BitTorrent clients have also be abused in a similar way. In those instances the KeRanger ransomware and the Keydnap info stealer malware. Adobe Flash Player has also earned the less than the desired reputation of been continually abused to carry out Supply Chain Attacks.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion