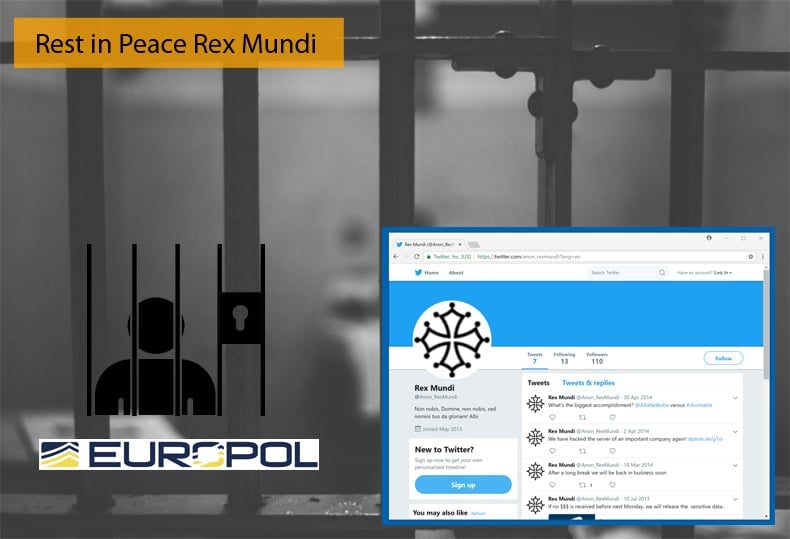
Rest in Peace Rex Mundi
Europol along with French, UK, and Thai police arrested eight people suspected either to have been involved or to have been part of a now infamous hacker group known as Rex Mundi. Meaning king of the world in Latin, the group has been active since 2012. The group became particularly known for hacking into companies' networks, stealing private information, and later contacting the victims to request the payment of a ransom fee. The group was also known for demanding fees for not disclosing the hacks and sometimes also asked for higher sums of money for revealing the security flaw they used to enter the victim's network. This probably seemed like a nice thing to do by the group in light of making the life of a poor CIO hell for a period.
Europol released a statement detailing the international operation supported by Europol and the Joint Cybercrime Action Taskforce (J-CAT) that started almost exactly one year ago. J-CAT whose responsibilities include combating cybercrime via a coordinated, international approach was launched in September 2014 and targets cybercrime, which includes other high tech crime and sexual exploitation of children, in the European Union and outside its borders.
In the statement, it was explained that a 25-year-old coder was arrested on 18 May by the Royal Thai Police based on a French international arrest warrant. This formed the eighth arrest of individuals believed to be associated with Rex Mundi. While the earliest reports of the group’s activities date to 2012, the initial date of the group’s formation is unknown. One hack, in particular, appears to be the nail in the coffin for the group. In May 2017, a British-based company was the victim of a cyber-attack of which a large amount of customer data was compromised. The attack was immediately claimed by Rex Mundi. A few days later, the company received a phone call from a French-speaking person explaining that he was a member of Rex Mundi. To that effect, the person shared a large number of credentials with the company to prove that they had indeed access to the data and was not a prank. He also demanded a ransom of either almost 580 000 EUR for the non-disclosure of the customer data. Alternatively, the company could pay 825 000 EUR for information on the security breach and how to handle it, thus being in character for the groups' modus operandi. For each day the company failed to pay, there would be a further increase in the ransom of EUR 210 000. As is now almost custom for hackers, the ransom was to be paid in Bitcoin.
What followed can only be described as an excellent example of international cooperation. Together the Metropolitan Police in the UK, the French National Police, and Europol were informed of the above incident. Within an hour, Europol’s Operational Centre was able to link the available information to a French national. Five people were arrested in June 2017 by the French authorities. The main suspect admitted his involvement in the blackmail but hired the services of a hacker on the dark web to carry out the cyber-attack. The French National Police arrested two hackers in France in October 2017 and a final accomplice, also a French national with coding skills, was recently apprehended in Thailand.
Group left a Trail of Hacks
Traditionally Rex Mundi has never been shy about their achievements. The group often went to Twitter to brag about their most recent successes. On the social media platform, their recent victims were exposed for all the world to see and often when the victims refused to pay the data was also dumped there. Past victims included AmeriCash Advance, Webassur, Drake International, Buy Way, Hoststar, Websolutions.it, Numericable, Habeas, AlfaNet, Domino's Pizza, and Banque Cantonale de Geneve (BCGE). This was the pattern till 2015 when news that systems of Banque Cantonale de Geneve (BCGE) have been hacked. Rex Mundi managed to exfiltrate data which it then demanded a 10,000 EUR ransom for. It was later revealed that the group managed to download a total of 30,192 private emails that contained sensitive client data. The bank did confirm that no bank accounts had been compromised but as far as the stolen details are concerned, the list includes names, addresses, phone numbers, account numbers, as well as email communication between the customers and the financial institution.
The hack of the Swiss bank appeared to be the last of which the group publically bragged about. As law enforcement started arresting hackers and hacktivists left and right, the group changed its modus operandi and eventually went underground. Operating in such a method meant that the group no longer announced their hacks online, to reporters, or leaking data when companies failed to pay. It can be assumed that the group believed this new tactic would be enough to safeguard them against prosecution. As it would happen this was not to be. It can be assumed that the groups brash and boastful past helped investigators to profile the group despite their recent efforts at remaining in the shadows as it were.
A Strong Message
It will interesting to see if the accused are successfully prosecuted and what punishment they may receive. Cases such as this could help send a strong message to cybercriminals. That is if cybercriminals do not take on board the message that you can be caught far sooner than expected. In 2015, the European Parliament released a study detailing the challenges of prosecuting cybercrime in general. While hackers may read the study and see the potential for not been prosecuted it is probably the opposite they should be worried about. By acknowledging problems, solutions can be found. Perhaps the actions of Europol, the Metropolitan Police, the French National Police, and the Royal Thai Police are an indication that many of those problems already have solutions.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion