PowerPool exploiting Window’s Zero-Day
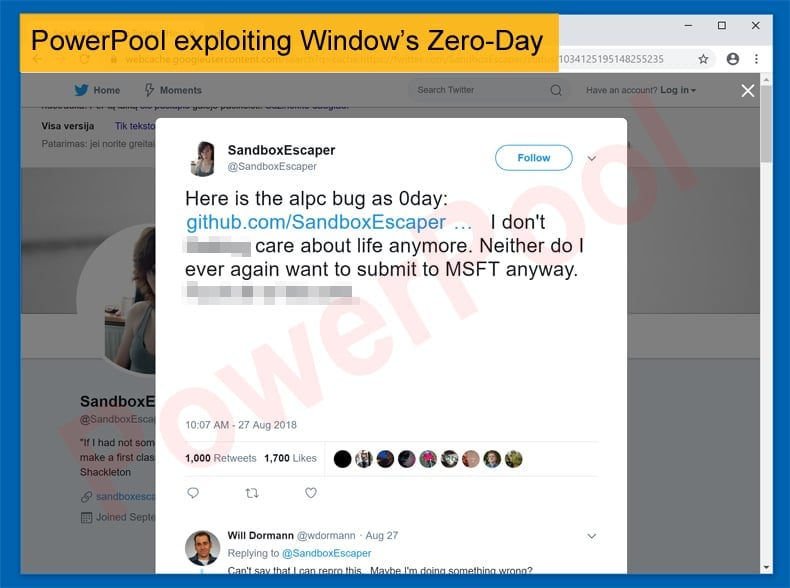
Security researchers at security firm ESET have witnessed the threat group “PowerPool” exploiting a Windows zero-day vulnerability. The vulnerability is being used by the threat group to elevate the privileges of a backdoor in targeted attacks. The flaw was disclosed on August 27 with the proof of concept code been published on GitHub the same day. The information was disclosed by a researcher seemingly frustrated with Microsoft’s bug submission process. The researcher’s Twitter account was no longer accessible shortly after she posted the tweet, but it’s unclear whether it was suspended or deleted. The flaw, however, has been already confirmed by security researchers, including Will Dormann, a vulnerability analyst at CERT/CC. It would seem that PowerPool has also confirmed that vulnerability in light of recent attacks.
SandboxEscaper
As a result of the researcher’s frustration, the security hole was not reported to Microsoft before its details were made public. Named “SandboxEscaper” the flaw affects the Advanced Local Procedure Call (ALPC) interface of the Windows Task Scheduler. Malicious actors with local access to the targeted device can exploit the flaw to escalate privileges to the targeted system by overwriting files that should normally be protected by filesystem access control lists (ACLs). An ACL can be seen as the file system which specifies which users or system processes are granted access to objects, as well as what operations are allowed on given objects. For example, the file system would work similar to this, if a file object has an ACL that contains (Alice: read, write; Bob: read), this would give Alice permission to read and write the file and Bob to only read it. While there is a lot of technical jargon in the above paragraph it is the flaws ability to allow a threat actor to increase privileges on a target system that is most appealing to PowerPool.
The flaw has been proven to work on both Windows 64-bit and 32-bit machines. Meaning that it has been successfully exploited on both Windows 10 and Server 2016. As of yet, Microsoft has yet to release a patch. However, the tech giant has launched an investigation and initially stated that a fix may be released with its regular Patch Tuesday updates, the company may roll out a patch sooner now that the vulnerability has been exploited in malicious attacks. For those worried that they may be or already are the target of an attack, 0Patch has released an unofficial patch and CERT has published an advisory which includes a list of mitigations.
SandboxEscaper is been exploited in the Wild
In an article published by security researchers at ESET, the local privilege escalation vulnerability has been exploited by a newly uncovered group it tracks as PowerPool. Based on the security firm’s telemetry and malware samples uploaded to VirusTotal, the threat actor appears to have leveraged the Windows zero-day against a small number of users located in the United States, the United Kingdom, Germany, Ukraine, Chile, India, Russia, the Philippines, and Poland in what seems to be highly targeted attacks. PowerPool, according to researchers, is using a slightly modified and recompiled code when compared to the proof of concept code disclosed on GitHub.
In the wild, the hackers have successfully managed to overwrite the C:\ProgramFiles(x86)\Google\Update\GoogleUpdate.exe file which is a legitimate updater for many Google applications. The hackers chose this file as it is regularly executed in Windows with administrative privileges, overwriting it with their malware has allowed the attackers to obtain elevated permissions on the targeted system. ESET is of the strong opinion that the attack begins with a malware-carrying email being sent to the targeted user.
In May of this year, a researcher at SANS came across an interesting spam campaign which used Symbolic Link (.slk) files for malware distribution. ESET believes that this method is being employed by PowerPool to infect machines. It is, however, using the technique in a far more targeted way than a typical spam email campaign. Once the malware is delivered via the email it is initially too used to exploit the vulnerability via a backdoor. This can be considered the first stage of deployment and seems to be done for purely reconnaissance purposes. If the infected machine presents an interest to the attackers, the malware downloads a second stage backdoor capable of executing commands on the system, uploading and downloading files, killing processes, and listing folders. The files downloaded by the second stage malware to compromised devices include several open source tools that allow the attackers to move laterally on the network. The list includes PowerDump, PowerSploit, SMBExec, Quarks PwDump, and FireMaster.
Not sophisticated but still Dangerous
ESET describes the attack campaign as “clearly not a state-of-the-art APT backdoor.” Despite this, the security firm did issue a clear warning by stating,
“This specific campaign targets a limited number of users, but don’t be fooled by that: it shows that cybercriminals also follow the news and work on employing exploits as soon as they are publicly available,”
Other than been targeted by PowerPool, the disclosing of the flaw to the public without following proper procedures presents further problems. As a result of the researcher publicly disclosing SandboxEscaper even the most up-to-date version of Windows could be compromised as no patch was released when the vulnerability and exploit were published. This placed many Windows users at risk and highlights why coordinated vulnerability disclosure procedures exist. They exist to prevent his scenarios from happening and help mitigate the risk to users by hackers and other threat groups.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion