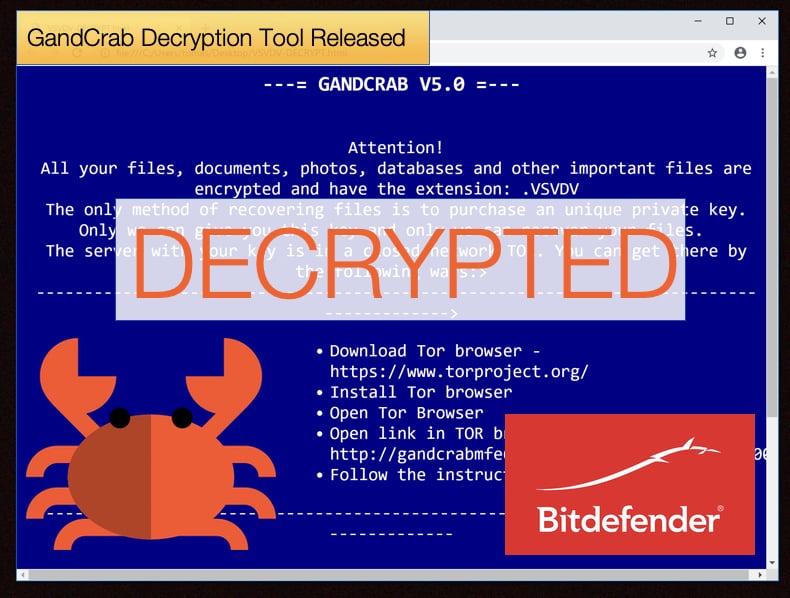
GandCrab Decryption Tool Released
Last week this publication published an article detailing the show of sympathy from the GandCrab ransomware developers to the people of Syria who had been infected. This show of sympathy took the form of the developers releasing the decryption keys for Syrians infected with GandCrab. On the face of it, the show of goodwill did appear as one. Unfortunately, while the keys were released there was now decryptor available to those infected with the ransomware. This meant that the keys were useless for most of the Syrians affected.
If you were of any other nationality you were truly out of luck as you had no decryption tool or key to help decrypt your encrypted files. That was the state of affairs till October 25. Announced via a Europol press release the law enforcement body stated that in a collaborative effort by Romanian police, with counterparts from Bulgaria, France, Hungary, Italy, Poland, the Netherlands, United Kingdom, United States and the security firm Bitdefender a decryption tool had been developed. Importantly the tool works on all but two versions of GandCrab (v 2 and 3). The release of this tool follows a week after the GandCrab developers made public decryption keys allowing only a limited pool of victims located in Syria to recover their files.
Why the fuss?
GandCrab has been in the news a lot recently and for all the wrong reasons. In 2018 security experts have seen multiple attack campaigns often using phishing tactics to distribute the ransomware. Added to this the ransomware is under constant development that incorporates tools to better avoid detection. Since it was first detected in January 2018 is has infected nearly half a million victims. In recent month according to Bitdefender, there has been an increase in businesses been targeted in the hopes of a quicker and bigger payday.
Once GandCrab takes over a victim’s computer and encrypts its files, it demands a ransom ranging from 300 to 6 000 USD. The ransom must be paid through cryptocurrencies currencies known to make online transactions less traceable, such as DASH and Bitcoin. In February 2018, Romanian police developed a decryption tool with the support Bitdefender and Europol. However, the rate of development seen with GandCrab has been aggressive, to say the least. This always meant law enforcement and security researchers were playing catch up. New GandCrab versions are usually released every one or two weeks, and the ransomware was ported to target even older Windows versions, such as XP.
The rapid spread of GandCrab attracted the eyes of other cybercriminals. The developers of the ransomware were not obvious to this and began offering GandCrab as a Ransomware as a Service (RaaS). This allowed those with no technical ability a toolkit for launching quick and easy malware attacks, in exchange for a 30% cut from each ransom payment. In order to further maximize the profits, the GandCrab developers also partnered up with other services, such as the malware crypter service NTCrypt who specialize in malware obfuscation. This enabled different criminal groups to practice their core competencies while working together to earn more illicit profits than they would be able to gather working individually.
Decryption Tool not a Vaccination
The newly released tool is capable of recovering data from GandCrab versions: v1 (GDCB extension), v4 (KRAB extension), and v5 (random 10-character extension, also the current/latest GandCrab version), respectively. This release followed shortly on the heels of an earlier tool released by Bitdefender which was far more limited. This tool was intended for the victims located in Syria. This decryption tool was able to be made due to the release of the decryption keys by the ransomware’s developers.
A representative of the Romanian Police Central Cybercrime Unit told ZDNet that the new decryption tool was “a cryptographic issue rather than an infrastructure issue,” suggesting investigators found a flaw in GandCrab's file encryption routine. Flaws in ransomware encryption schemes is how authorities and cyber-security firms have been able to decrypt most ransomware strains in the past years. The representative further wished to emphasize the motivation behind the tools development as,
“Together, we have understood the perception of this threat, and through joint efforts, we want to support the hundreds of thousands of ransomware victims in Romania and around the world,”
While there is no tool yet for version 2 and 3, Bitdefender is currently working on developing a tool for those versions. It is important to note that the tool is not a vaccination, meaning that it will not prevent future infections. Rather it enables the victim to recover encrypted files. The tool is free to download and can be found at No More Ransom, an organization dedicated to helping victims of ransomware. The victim just needs to click the link according to which version they have been infected with.
Victory for Law Enforcement
The release of the new decryption tool is most certainly a victory for Law Enforcement and indirectly victims who had their files encrypted. That been said both law enforcement bodies and security firms were quick to point out that prevention is better than cure. To that extent Europol provides the following tips to actively prevent infection and becoming a victim:
- Always keep a copy of their most important files somewhere else: in the cloud, on another drive, on a memory stick, or on another computer.
- Use reliable and up-to-date anti-virus software.
- Do not download programs from suspicious sources.
- Do not open attachments in e-mails from unknown senders, even if they look important and credible.
- And if you are a victim, don’t pay the ransom!
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion