Bushido Botnet Offered as MaaS
Hackers offering Malware-as-a-Service (Maas) is not a new trend by any means. Since the first detections of such schemes, their popularity has not seemed to dwindle of the years. This is in part because they allow those less technically minded, or too lazy to develop their own malware, with an option to make a quick buck, albeit an illegal one. MaaS can be defined as the hiring of software and hardware for carrying out cyber attacks. In a majority of instances, the owners of MaaS servers provide paid access to a botnet that distributes malware. Like their more legal cousins, clients of such services are offered a personal account through which to control the attack, as well as technical support.
Security researchers at Fortinet have published details on a recently discovered DDoS-for-hire service built with leaked code that offers easy and cheap access to sufficient power to knock down most targets. Distributed Denial of Service (DDoS) attacks is an attack in which multiple compromised devices attack a target simultaneously, such as a server, website, or other network resources, and cause a denial of service for users. DDoS businesses have been around for quite a while, with the sheer amount of mobile devices it is more common for these to be used to drive attacks.
Thousands of Compromised Devices, for Low Prices
The DDoS-for-hire goes by the name of “ox-booter” and is sold to potential customers as a botnet consisting of over 500Gbps of power and 20,000 bots. When researchers began their analysis it became apparent that these numbers are a slight over exaggeration. Fortinet counted 16,993 bots capable of carrying out attacks at 424.825 Gbps. Bleeping Computer saw even lower figures with 8,000 compromised systems ready to run a DDoS attack at 396 Gbps. For customers wishing to complain I doubt there is an advertising complaints board willing to hear their grievances.
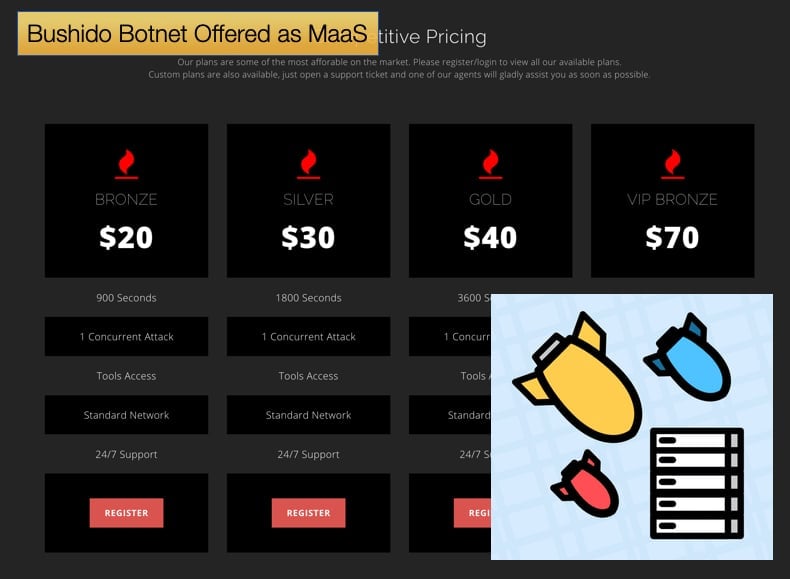
Despite the discrepancy in what is advertised via social media what really caught the attention of researchers was that ox-booter is powered by the Bushido botnet. Since the service has hit the market on October 13, ox-booter carried out over 300 attacks, with peaks of over 50 attacks in some days. In the past four days, an overall decrease in activity has been seen. The daily number of attacks were between 11 and 35 for the four days. Fortinet pointed out that, “Like any other DDoS-for-hire, initiating a DDoS attack is made through a web user interface, which avoids the need for direct contact between the user and the bot master,” Like other such services the 0x-booter service provides targeting for layer 4 and layer 7 of the OSI (Open Systems Interconnection) model, the transport, and the application layers.
The Bushido Botnet
Fortinet discovered the botnet in September of this year and the botnet is believed to be owned by a group going by the name of ZullSec. While it would appear to be a new botnet there is evidence to suggest it is older. The MalwaeMustDie group of security researchers appear to have come across samples of Bushido earlier than Fortinet’s discovery of the botnet. Upon closer examination researchers were able to determine that Bushido was derived from Mirai. As botnets go Mirai is probably as infamous as they come, its source was leaked and has since been used in numerous record-breaking DDoS attacks. One such attack involved the website of renowned security journalist Brian Krebs which was the largest attack at the time.
Bushido is not a complete copy of Mirai, it has more DDoS attack options than Mirai. Further, it compromises devices using a different set of usernames and passwords and includes a list of exploits for known vulnerabilities. While more powerful with better attack options Bushido includes nothing all that original. Fortinet believes that the code for the 0x-booter was based on that of a different DDoS-for-hire service called Ninjaboot, whose code was leaked online. Even though Bushido boasts better attack methods than Mirai, these appear to have been borrowed from another botnet, Owari, whose code also got leaked online. Ox-booter, like Frankenstein’s monster, is an amalgamation of different parts modified slightly to work. This copying of code has allowed hackers to set up shop to provide a service for other cyber hackers, all in the name of turning over a quick profit. Running 300 attacks for the minimum price of 20 USD makes the operators of Ox-booter 6000 USD, all done in half a month.
MaaS and DDoS-for-hire
The Zeus botnet was one of the first examples of a successful MaaS operation. Its creators released a developer’s kit that gave clients on the dark web the ability to not only lease its tremendous network of infected computers but to configure it for their specific purposes. Zeus was also the first to be able to receive commands from any client’s computer. Previously botnets could only be operated from a single command-and-control server. Zeus’ service was eventually disrupted by an FBI investigation in 2010 but has since provided other hackers with a possible business model. This business model promises massive profit from renting out customizable botnets.
This, in turn, has had a major effect on how security firms and law enforcement have had to approach cybersecurity. This is simply because if you have the cash on hand, despite knowing very little about hacking, you can deploy the world’s most advanced bots to attack practically any organization they want to target. Ultimately it means more attacks of which understaffed security firms will have to contend with.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion