Campaign Abusing Windows Narrator Discovered
Researchers have discovered a malware campaign targeting computers throughout Asia which looks to replace Windows Narrator with a malicious version. The malicious version, in turn, grants the attacker not only remote access but almost unfettered persistence. Windows Narrator forms part of Microsoft’s Ease of Access suite which is built into Windows 10 and operates as a screen reader. Narrator is designed to improve the accessibility of machines running Windows 10 so those with low-level vision can use the machine relatively unhindered. The software also replaces the mouse to receive voice commands and is compatible with braille displays.
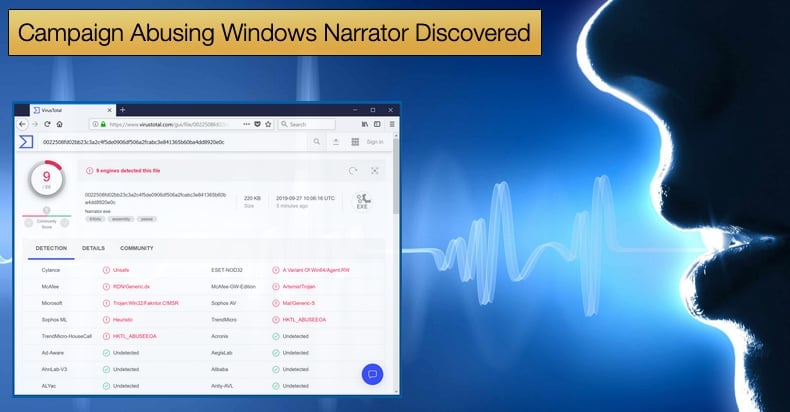
Researchers working for BlackBerry Cylance discovered the campaign and noticed that the campaign targets predominantly systems belonging to technology companies based in Southeast Asia. In a report published by Cylance, it was noted that the attackers use a modified and open source piece of software which grants remote access. Called PCShare by its developers it is currently available via GitHub. The tool is heavily modified and customized for the campaign at hand, featuring a tailored command-and-control (C2) servers, encryption, and proxy bypass functionality. At the same time, all code not deemed useful to the attacker’s goals is removed from the source code.
The highly modified version of PCShare makes use of two techniques to evade detection by anti-virus software. The first been DLL side-loading which is commonly defined as,
“Programs may specify DLLs that are loaded at runtime. Programs that improperly or vaguely specify a required DLL may be open to a vulnerability in which an unintended DLL is loaded. Side-loading vulnerabilities specifically occur when Windows Side-by-Side (WinSxS) manifests are not explicit enough about characteristics of the DLL to be loaded. Adversaries may take advantage of a legitimate program that is vulnerable to side-loading to load a malicious DLL. Adversaries likely use this technique as a means of masking actions they perform under a legitimate, trusted system or software process.”
In demystifying the jargon full definition above a DLL, or dynamic link library file, are files created so that multiples programs can access the file information at the same time, when used in a side-loading attack malware is written to the DLL rather than the disk in an attempt to avoid detection.
In this campaign, the malware is side-loaded with assistance from the legitimate “Nvidia Smart Maximise Helper Host” application that is part of the Nvidia GPU graphics driver. The second technique employed is seen in various stages of memory injection, another method of writing the malware to memory rather than hard disk to prevent detection and analysis. In addition to these techniques, payloads are encrypted depending on their execution path. This is a commonly used tactic to evade analysis by anti-virus sandboxes, for example.
Once the malware has been able to create a backdoor on the target machine it is capable of creating, deleting, renaming and modifying files and directories. Further, the malware, which can be seen as a trojan, can list and kill processes; edit registry keys and values; execute binaries, spawn command-line shells, and can also communicate with its command and control server to drop additional payloads or transfer stolen files. Once the trojan successfully infects a computer, the malware then moves to target and replace Narrator.exe to gain SYSTEM-level permissions via the Winlogon command, which also allows the attackers to spawn any executable. The fake version of Narrator can then launch with a hidden window that waits for hardcoded key combinations known only by the attacker allowing them to execute what they wish when they want. The researchers noted,
“The aim of the attackers is persistent exfiltration of sensitive data, as well as local network reconnaissance and lateral movement. The use of Fake Narrator to gain SYSTEM-level privileges indicates the threat actor is interested in long-term monitoring of the victim, as opposed to one-off data collection.”
Who’s behind the campaign?
The researchers who discovered the campaign and analyzed the malware have not been quick to point the finger. However, it is believed that the campaign may be operated by a Chinese advanced persistent threat (APT) group. Researchers also noted similarities in tactics and techniques used by the group dubbed Tropic Trooper. Such similar tactics include the reusing of publically accessible code. It is theorized that this approach reduces the number of resources needed to develop a viable attack toolset. The group also sometimes referred to as Key Boy is known to be behind campaigns targeting government, healthcare, transportation, and high-tech industries based in Taiwan, the Philippines, and Hong Kong. Tropic Trooper is known to employ DLL side-loading as well as other tactics to gain a foothold in a targeted network. Backing up this belief with evidence researchers concluded,
“Based on the use of numerous Chinese open-source projects and the geographical location of the victims, we suspect the threat actor to be of Chinese origin. The use of PcShare was previously seen in relation to a group called Tropic Trooper, which has been targeting government institutions and heavy industry in the same region since at least 2012. Tropic Trooper (a.k.a. KeyBoy) is known to use a toolset that includes the PcShare backdoor, alongside another popular backdoor called Poison Ivy, and a bespoke one called Yahoyah…With PcShare being an open-source project which could be leveraged by any number of threat actors operating in this region we cannot be completely certain the attack is attributable to Tropic Trooper at this time.”
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion