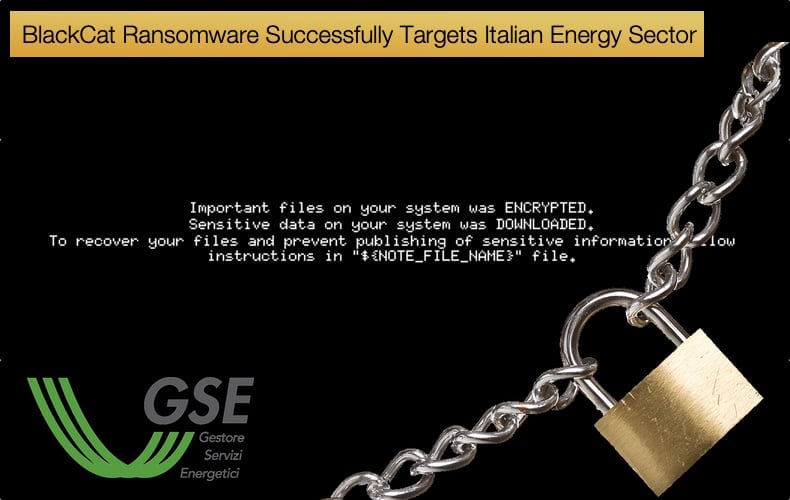
BlackCat Ransomware Successfully Targets Italian Energy Sector
Towards the end of August, an attack hit the systems of Italy's energy agency the Gestore dei Servizi Energetici SpA (GSE). The company is publicly owned and specializes in generating electricity from renewable resources across Italy. In a statement to Bloomberg, a spokesperson for the company at the time of the attack stated,
“GSE’s IT systems and websites were shut down to protect the data, the statement said. The agency’s role as a gas buyer of last resort for Italy’s electricity network hasn’t been hampered…Italian police and cybersecurity authorities are still assessing the extent of the attack and what kind of data have been compromised,”
The above statement was about all the information the public had access to for some time.
The drip feeding of information to the public following cyber attacks is nothing new and almost always new information will come up following investigations by security researchers and cybersecurity journalists.
For many digging up more information involves looking at known hacker forums and ransomware websites that announce new victims.
According to Bleeping Computer, the BlackCat ransomware group added a new entry to its dark web data leak site claiming to have stolen roughly 700GB of files from the Italian energy agency's servers.
The announcement by BlackCat’s operators was made before GSE released its statement. BlackCat is also tracked as ALPHV by several security firms and researchers.
The attackers claim that the data stolen contains highly confidential data including contracts, reports, project information, accounting documents, and other internal documentation.
GSE is not the only company in the energy sector that has suffered an attack by BlackCat ransomware operators.
Right at the start of August, the ransomware gang announced that they had successfully attacked Creos Luxembourg S.A., a company that is a natural gas pipeline and electricity network operator in the central European country.
The attack resulted in online portals being unreachable and several services were impacted in the wake of the attack. The company’s parent company Encevo released a press statement noting,
“The Encevo Group wishes to inform you that its Luxembourg entities Creos (manager of the network) and Enovos (energy supplier) were victims of a cyberattack on the night of July 22 to 23, 2022. The Encevo Group crisis unit was immediately triggered and the situation is currently under control. We are bringing together all elements necessary for understanding and complete resolution of the incident. Nevertheless, this attack has a negative impact on the operation of the customer portals of Creos and Enovos. We apologize to our customers for the inconvenience and We are doing our best to restore service as soon as possible. Creos and Enovos emphasize that the supply of electricity and gas is not affected and that the breakdown service is guaranteed. [Translation by Google]”
BlackCat’s Experienced Affiliates
Unfortunately, BlackCat has been adopted by several highly skilled and experienced affiliates associated with some of the world’s most prolific financially motivated hackers.
The ransomware itself is motivated as a Ransomware-as-a-Service, meaning that affiliates will compromise, infect, steal data, then encrypt data using the ransomware created by a separate developer.
Typically, affiliates, malware developers, malware admins, and third parties who achieve initial access to targeted corporate networks will all split the proceeds from the crime.
In this regard, BlackCat boasts two infamous threat groups as affiliates. The first is FIN12 described by the security firm Mandiant as,
“...FIN12, an aggressive, financially motivated threat actor behind prolific ransomware attacks since at least October 2018. FIN12 is unique among many tracked ransomware-focused actors today because they do not typically engage in multi-faceted extortion and have disproportionately impacted the healthcare sector. They are also the first FIN actor that we are promoting who specializes in a specific phase of the attack lifecycle—ransomware deployment—while relying on other threat actors for gaining initial access to victims. This specialization reflects the current ransomware ecosystem, which is comprised of various loosely affiliated actors partnering together, but not exclusively with one another.”
According to Microsoft, in a report on BlackCat, FIN12 who in the past has distributed several other ransomware strains including Hive, Conti, and Ryuk, began distributing BlackCat payloads in March 2022.
The switch to BlackCat is believed to be a response to Hive’s encryption keys being leaked and the gang is no longer confident they can ensure payment using Hive.
The second notable threat actor deploying BlackCat is tracked by Microsoft as DEV-0504, colloquially the group has gone by REvil Gang and now BlackCat Gang. For those tasked with defending IT infrastructure the group typically follows the following attack pattern:
- Entry vectors are gained by the affiliate remotely signing into devices with compromised credentials, such as into devices running software solutions that allow for remote work remains a popular choice.
- The attackers use their access to conduct network discovery on the domain to find vulnerable machines and infrastructure.
- Lateral movement is the next hurdle, often attackers will use the initial compromised account when looking to spread laterally.
- Sometimes credential theft is done with tools like Mimikatz and Rubeus.
In defending against BlackCat, Microsoft notes that,
“In the BlackCat-related incidents we’ve observed, the common entry points for ransomware affiliates were via compromised credentials to access internet-facing remote access software and unpatched Exchange servers. Therefore, defenders should review their organization’s identity posture, carefully monitor external access, and locate vulnerable Exchange servers in their environment to update as soon as possible. The financial impact, reputation damage, and other repercussions that stem from attacks involving ransomware like BlackCat are not worth forgoing downtime, service interruption, and other pain points related to applying security updates and implementing best practices."
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion