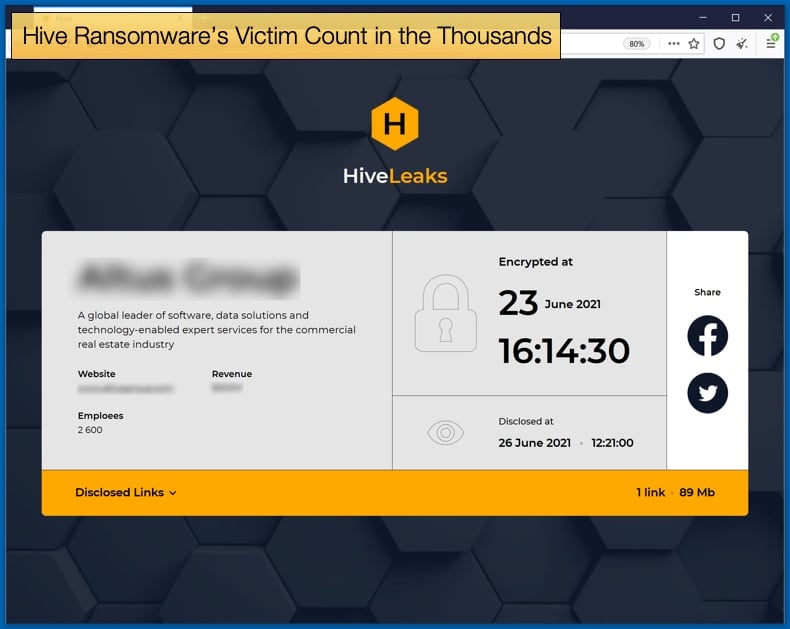
Hive Ransomware’s Victim Count in the Thousands
According to the Federal Bureau of Investigation (FBI), the Hive gang has successfully extorted over 100 million USD from approximately 1300 victims dating back to July 2021. Unfortunately, those that refuse to pay are likely to experience further ransomware payloads down the line, which is in line with recent Hive tactics and can be seen as an escalation in the famed double extortion tactic prominent in the ransomware space.
Summarizing Hive’s basic tactics, a joint advisory released by the FBI stated,
“As of November 2022, Hive ransomware actors have victimized over 1,300 companies worldwide, receiving approximately US$100 million in ransom payments, according to FBI information. Hive ransomware follows the ransomware-as-a-service (RaaS) model in which developers create, maintain, and update the malware, and affiliates conduct the ransomware attacks. From June 2021 through at least November 2022, threat actors have used Hive ransomware to target a wide range of businesses and critical infrastructure sectors, including Government Facilities, Communications, Critical Manufacturing, Information Technology, and especially Healthcare and Public Health (HPH).”
How Hive affiliates gain access to targeted IT infrastructure depends primarily on the affiliate and the target itself. Security researchers have seen HIve affiliates gain initial access through single-factor logins via Remote Desktop Protocol (RDP), virtual private networks (VPNs), and other remote network connection protocols.
Other Hive affiliates have also managed to bypass multi-factor authentication on FortiOS servers that were vulnerable to disclosed vulnerabilities are were not patched.
Hive affiliates have also gained access to IT infrastructure through the tried and tested way of phishing emails used to steal credentials users are tricked into handing over.
Later stages of the phishing attack made use of the following Microsoft Exchange Server vulnerabilities:
- CVE-2021-31207 - Microsoft Exchange Server Security Feature Bypass Vulnerability
- CVE-2021-34473 - Microsoft Exchange Server Remote Code Execution Vulnerability
- CVE-2021-34523 - Microsoft Exchange Server Privilege Escalation Vulnerability
To remain undetected once initial access is granted Hive affiliates will typically look to complete the following steps according to FBI officials:
- Identify processes related to backups, antivirus/anti-spyware, and file copying and then terminate those processes to facilitate file encryption.
- Stop the volume shadow copy services and remove all existing shadow copies via vssadmin on the command line or via PowerShell.
- Delete Windows event logs, specifically the System, Security, and Application logs.
Once persistence is achieved the affiliate will look to steal sensitive information and data from the victim’s networked infrastructure.
The stolen data is exfiltrated in a variety of ways including a combination of Rclone and the cloud storage service Mega.nz. Once data is successfully exfiltrated data is encrypted and a ransom note is delivered.
The next steps have been summarized by the FBI as follows,
“Once the victim organization contacts Hive actors on the live chat panel, Hive actors communicate the ransom amount and the payment deadline. Hive actors negotiate ransom demands in U.S. dollars, with initial amounts ranging from several thousand to millions of dollars. Hive actors demand payment in Bitcoin…Hive actors have been known to reinfect—with either Hive ransomware or another ransomware variant—the networks of victim organizations who have restored their network without making a ransom payment.”
ARCrypter Goes Global
In other ransomware news, a ransomware strain known for targeting victims in Latin America is taking a new global approach to targeting victims. Called ARCryptor, the ransomware was initially discovered by Chilean threat analyst Germán Fernández and was used in an attack against a government agency in Chile last August.
No following the release of a report by BlackBerry the ransomware strain, which appears not to based on any previous strain, is targeting organizations as a far away from Latin America as China and Canada. Bleeping Computer has confirmed that victims are also popping up in victims in Germany, USA, and France.
While the threat actors claim to steal data during their attacks, the ransomware operation does not currently have a data leak site that they use to publish data for unpaid victims.
At this time, little is known about the operators of ARCrypter, their origin, language, and potential links to other ransomware gangs. BlackBerry researchers concluded,
“We have not identified any evidence to attribute this malware to any previously known threat actor or threat group. While both campaigns targeted Latin American countries, currently there is no evidence in the code suggesting that a local threat actor could be the culprit…In early August 2022, an unknown ransomware variant which BlackBerry named ARCrypter was found targeting Latin American institutions. At this point, we have witnessed that the threat actor behind it has expanded its operations to other countries like China and Canada. The research conducted for this report has helped uncover two sets of files – a malware dropper and file encryptor.”
For more information on the indicators of compromise for both ARCrypter and Hive both BlackBerry and the FBI have published extensive lists and information for those looking to defend corporate IT infrastructure.
There has been somewhat of a surge in ransomware activity in recent months, prompting administration staff to be alert for any possible intrusion by a malicious actor.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion