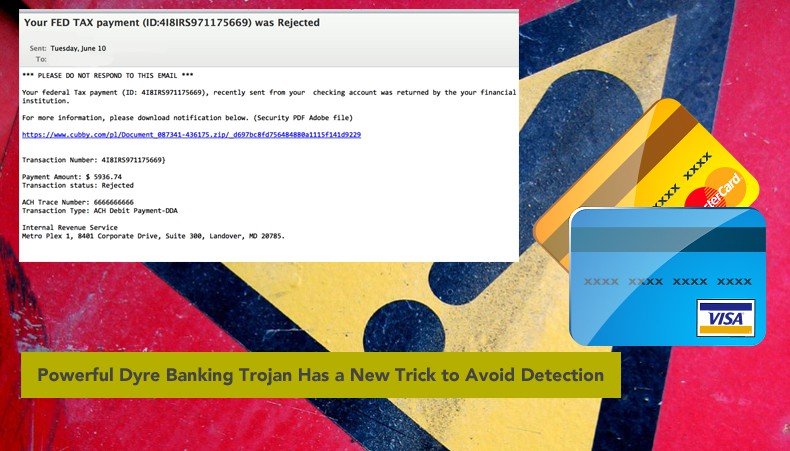
Powerful Dyre Banking Trojan Has a New Trick to Avoid Detection
Perhaps the most dangerous banking Trojan to emerge since the takedown of the Gameover Zeus botnet last summer, the Dyre banking Trojan has been credited with millions of dollars in losses around the world. Although most modern antivirus suites detect the original version of Dyre as of this writing, hackers have been working to update the banking Trojan in an effort to squeeze additional financial gain out of this powerful malware variant. Security researchers from Seculert recently discovered a new version of Dyre in the wild that is capable of avoiding sandbox detection tools. While this may seem like a complicated programming trick, the mechanics behind this evasion technique are really quite simple. Once installed on a PC, this new version of Dyre checks to see how many processor cores the infected machine is running.
If only one core is detected, Dyre assumes it is running in a sandbox and immediately terminates itself – removing all traces of infection from the machine before it can be detected by security analysis tools or the security researchers operating the sandbox environment. Sandbox environments are being used with increased frequency by Web security firms and large corporate IT departments alike as a way to observe the behavior of unfamiliar or untrusted code to detect malware prior to releasing the code to the company intranet. To save system resources, most of these sandbox environments are configured to operate using just one processor and one core.
This means that although Dyre’s new trick may seem rudimentary compared to other evasion techniques that have come to light in recent months, it is extremely effective when it comes to detecting sandbox environments where its true purposes could be easily discovered by a variety of analysis tools.
While many malware variants exhibiting sandbox detection techniques rely on more complicated coding (such as looking for specific processes that would indicate a virtual machine), the authors of this variation of Dyre apparently decided that just counting the cores running on the machine was “good enough” for their purposes.
This latest modification to the original Dyre code is just one of many tweaks and modifications that have been made to Dyre since its initial release last year. Just a couple of months ago, for instance, researchers at IBM discovered a malware campaign in which a Dyre variant – referred to as Dyre Wolf – was used to steal more than $1 million from business in the United States and Europe. In another recent report, this one released by Dell SecureWorks, Dyre was named as the most dangerous banking Trojan to have emerged since the Zeus botnet was taken down by a global task force last year.
Dyre is typically spread via spam email campaigns with malicious payloads attached or by drive-by download techniques that rely on zero-day exploits in popular Web browser plugins including Java, Flash, and Microsoft Silverlight.
To protect yourself from this and future Dyre variants, ensure your OS and all third-party applications are updated regularly, refrain from opening any unsolicited email, and disable plugins that are not explicitly required for daily Web browsing activities.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion