News Archive May 2014
Monthly Cyber Security News Archive: May 2014 Summary
Table of contents:
- More Open Source Security Software Woes
- Microsoft Warns Users of New Internet Explorer Vulnerability
- Sefnit Malware Now More Sophisticated
- Ransomware Evolves
- Zeus Disguised as PayPal Email
- Norwegian Facebook Virus Spreading Quickly
- Change your eBay Password Now!
- BlackShades Malware Bust Shows Just How Dangerous the Trojan Really Is
- Fake Heartbleed Removal Tool Circulates as Spam Email
- Banking Trojan Disguised as Popular Instant Messaging App for Android
More Open Source Security Software Woes
03.05.14
Recently, the Heartbleed bug made headlines around the world when a serious vulnerability in the extremely popular OpenSSL standard was discovered that allowed hackers to hijack secure server sessions. While the majority of Web servers affected by Heartbleed have already been fixed, there is another threat to open source security software. OAuth and OpenID are both log-in tools used by many big-name websites including Facebook, Microsoft and LinkedIn. Most users are familiar with OAuth 2.0 as the pop-up window that grants a variety of web and mobile applications access to Facebook or other social media outlets.
Wang Jing, a student at the Nanyang Technological University in Singapore, first discovered the vulnerability. Known as “Covert Redirect”, this vulnerability can masquerade as a log-in popup using the affected site’s domain.
The vulnerability actually works when someone clicks on a malicious phishing link. A Facebook log-in window appears asking the user to authorize Facebook access for the malicious application. The difference between this threat and other phishing schemes is that Covert Redirect uses the real site information for authentication.
Unfortunately, the released information is released to the hacker instead of the legitimate website. Everything from email addresses, contact lists and birth dates are immediately accessible by the hacker. Some reports even indicate that the exploit can give the attacker full control of the affected Facebook account.

When used by hackers specializing in identity theft, Covert Redirect could provide most (if not all) information required to steal a victim’s identity including answer to common security questions used to authenticate banking sessions and other personal transactions.
Another danger presented by the Covert Redirect flaw is that whether or not the users authorizes the malicious app, the victim is redirected to any website of the hacker’s choosing. This could be another phishing site or even be a drive-by download attack testing for multiple vulnerabilities before dropping a malicious payload on the victim’s computer without detection.
Interestingly enough, Wang contacted Facebook to report the flaw and was shunned by the social media company. Specifically, Facebook acknowledged some of the risks inherent to using OAuth 2.0 but was quoted as saying “short of forcing every single application on the platform to use a whitelist,” fixing this bug was “something that can’t be accomplished in the short term.” Keep in mind that Facebook isn’t the only major web presence currently relying on OAuth 2.0. Yahoo, PayPal and GitHub also use the open source security service to authenticate users and add additional permissions to existing web services. Some of these services, such as PayPal, claim that they have already incorporated additional security features that protect against this vulnerability and other known security issues with OAuth 2.0 and OpenID. That said, Wang insists that short of incorporating a whitelist of verified redirect URLs, there is no way to protect against this vulnerability and many companies are not interesting in the work involved in this security tactic. At the time of this writing, LinkedIn is the only affected provider that is actively compiling a whitelist of redirect URLs from third party software providers. Until this vulnerability is addressed, only grant access to applications that you explicitly need. Unsolicited permission requests – even if they look legitimate – could very well be the Covert Redirect flaw in action.
Microsoft Warns Users of New Internet Explorer Vulnerability
05.05.14
People still using Microsoft’s Internet Explorer now have another reason to be worried. A previously unknown security flaw has been detected that affects all active versions of the popular web browser. The vulnerability is present in all versions of IE from IE6 to IE11 (the current release) and piggybacks on a known Flash exploit that bypasses security protections built into the Windows operating system. Officially referred to as CVE-2014-1776, the vulnerability allows for remote code execution in a targeted attack environment. This means hackers can install malicious software directly on the machine without the knowledge or consent of the user.
The attack relies on a new vulnerability known as “use after free.” Basically, when memory is released a small amount of data corruption normally occurs. The vulnerability takes advantage of this data corruption to bypass Windows Data Execution Protection (DEP) and Address Space Layout Randomization (ASLR) according to FireEye, an Internet security firm. FireEye originally noticed the vulnerability when it was used to target both financial and defense institutions using Internet Explorer.
Other possible uses for this vulnerability include executing remote code from malicious or spoofed websites that could drop a variety of dangerous payloads including banking Trojans such as Zeus and Citadel.
The way Internet Explorer access objects in memory that have already been deleted or that have not been properly allocated allows hackers to bypass all remote code execution security measures in both IE and the Windows OS and execute arbitrary code on the victim’s computer. Although this vulnerability officially affects all current versions of Internet Explorer, actual attacks have only been reported on versions 9, 10, and 11. Since these represent the majority of active Internet Explorer installations browsing the Web, this is not surprising. In all, this vulnerability affects approximately 26% of Web browsers currently in use around the world. This blog recently reported that Microsoft as of early April the venerable Windows XP operating system would no longer receive updates from Microsoft.

The software giant unexpectedly announced that even XP would receive a security update for this vulnerability due to the serious nature of possible exploits and the fact that every version of Internet Explorer is currently susceptible to this threat.
According to a Microsoft spokesperson, customers with automatic updates enabled will not need to take any action for the security updates patching this vulnerability to be downloaded and installed. That said, many Windows updates to not officially take effect until a reboot has been performed.
Restarting the computer after installing these updates ensures that all security patches have been successfully installed. While it’s refreshing to see Microsoft providing a security patch for Windows XP machines, the company cautions that future security vulnerabilities probably won’t be patched in the 12 year old operating system. Officially, Microsoft still recommends that users upgrade to a modern OS such as Windows 7 or Windows 8.1 to continue receiving important security updates in the future. For now at least, XP users are safe…until the next big vulnerability is discovered.
Sefnit Malware Now More Sophisticated
07.05.14
Security experts recently uncovered a new version of Sefnit, malware that first made headlines late last year when it was thought that millions of machines would become infected with Sefnit in a span of just a few months. Researchers at the Microsoft Malware Protection Center (MMPC) analyzed Sefnit in January and declared that the Sefnit malware family has been used successfully for a variety of illicit purposes including generating rogue ad-clicks (to defraud advertising companies) since 2011. Previous versions of Sefnit have relied on the Tor network to evade detection, but the authors of Sefnit realized that Tor does not work well as a Command & Control (C&C) channel because high traffic on the anonymous browsing network can drastically slow down the performance of the botnet. The most recent version of Sefnit does not rely on Tor. Instead, it uses a direct connection to C&C servers via a Plink connection.
Since Plink is legitimate software solution that rewards users with point for shopping at various merchants, most antivirus and firewall software doesn’t detect the open channel as malware.
In addition to being used as an ad-click generator, Sefnit has also been observed connecting to Bitcoin mining operations – essentially taking over the GPU of an infected computer and using it to solve complex algorithms as part of a Bitcoin mining pool.
Sefnit is also commonly associated with search result hijacking scams. In these scams, victims are redirected to predetermined search results no matter what is entered into the search engine text field. Typically, the hijacked search results all point to malicious websites full of Flash and Java exploits waiting for unsuspecting users to arrive. Recently, Microsoft reclassified to other programs as malware: Rotbrow and Brantall. Both of these programs are now being used in conjunction with Sefnit to bypass many antivirus programs and trick unsuspecting users into inadvertently installing the Sefnit botnet. In the past, both of these programs were considered legitimate. Rotbrow purports to be a safeguard against browser add-ons and Brantall is supposedly a generic installer for legitimate programs.

The only thing either of these programs appear to do is install Sefnit behind most malware protections included in the operating system and antivirus software. As the Bitcoin mining “gold rush” winds down, hackers have been repurposing Sefnit to work as a Litecoin mining rig instead. Whether attempting to mine Litecoins or Bitcoins, the additional stress of the machines GPU can make performing simple tasks difficult at best.
To protect yourself from Sefnit, Rotbrow and Brantall, avoid peer-to-peer file sharing sites as this is one of the common ways the malware is distributed.
Also, avoid downloading and installing any third-party installation software as Windows is more than capable of installing all legitimate programs without a third-party solution that could be packed full of malware. The newest iteration of Sefnit (officially referred to as Sefnit.BW) nearly tripled the worldwide infection rate at the end of last year. Millions of computers remain infected with this botnet. Many of the infected machines are dormant – but for how long is anyone’s guess.
Ransomware Evolves
11.05.14
Not long ago this blog covered a malware threat known as Cryptolocker – a ransomware variant that encrypts a victim’s hard drive data using an RSA-2048 encryption algorithm (read: impossible to crack without the decryption key). Once the hard drive data has been successfully encrypted, the victim is forced to pay a ransom to receive the decryption key from the attacker or lose their data forever. The problem with ransomware is that it is impervious to current antivirus solutions. Once the program has been installed and personal data encrypted, there is literally nothing that can be done to save the data other than to pay the ransom (which can range from a few dollars to a few hundred in most cases).
While Cryptolocker was a relatively successful malware campaign, hackers are now upping the ante with new variations that are even more dangerous. One newer ransomware variation is known as CryptoWall.
While Cryptolocker relies on a graphical user interface (GUI) to let victims know what’s going on, CryptoWall drops the GUI. Instead, it opens a webpage after the hard drive has been encrypted and leaves a text file in every encrypted directory.
Victims are forced to install Tor or another layered encryption browser to pay the attacker directly. Previous ransomware versions used a payment processing “middleman”, but CryptoWall circumvents the need for a payment processor and increases the profit potential for hackers. Perhaps even more alarming is the newest iteration of ransomware known as DirCrypt. Rather than attacking specific file extensions (like Cryptolocker and Cryptodefense), DirCrypt encrypts all files on the hard drive and concerts them into Rich Text Format (RTF) documents with a *.enc.rtf extension. The malware doesn’t even notify victims that an encryption lock is in place.
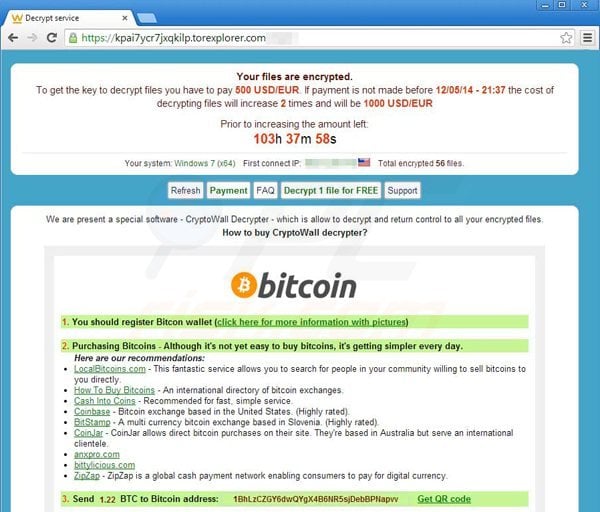
Rather, a document that has been encrypted must be opened to see the contents of the RTF file complete with instructions for paying the ransom and receiving the decryption key. Another difference with DirCrypt is that it actively checks for new files and folders written to the infected hard drive or files modified after encryption has started and encrypts them as well. Cryptolocker, CryptoWall and Cryptodefense only encrypt files once during initial installation meaning that newly created files are safe. Since DirCrypt actively encrypts new files, it is even more difficult (if not impossible) to use the infected computer for anything until the ransom has been paid and decryption key received from the attackers.
Unfortunately, this type of malware is becoming extremely popular with underground cyber criminals as it is a very lucrative business model.
Most malware can be removed once detected using a variety of antimalware tools, but ransomware works differently and practically forces people to pay the ransom (which is set by the hackers deploying the threat) or else trash the computer and all personal data contained within it. Many antivirus suites successfully detect known variations of ransomware, but to be safe, do not download any unsolicited files or attachments and always check to make sure all OS and antivirus updates are installed promptly to prevent ransomware being installed as a drive-by download via a malicious website.
Zeus Disguised as PayPal Email
12.05.14
The extremely dangerous Zeus Trojan is no stranger to this blog. Neither are the countless phishing emails disseminated by eager hackers every day. However, what happens when both of these threats are combined into a single, well-designed scam? Recently, a variation of Zeus known as Spyware.Zbot.ED was spotted as part of a mass phishing campaign that appears to be targeting existing PayPal users. The spam email looks identical to an actual PayPal communication (unlike other phishing emails with grammatical errors and bad graphics), but all of the links lead directly to a malware-serving website complete with a dangerous version of the Zeus banking Trojan. The email appears to notify the recipient that they have received a payment from a customer and even includes details about the item and the amount of the transaction.
Obviously, if the recipient does not sell any such item it should serve as a warning that the email is a scam, but the promise of a “Payment Received” notification from PayPal often clouds the judgment of the potential victim enough to at least click on one of many embedded links. Every link in this fake email redirects the user to hxxp://hoodflixxx.com/PP_det.html ->hxxp://62.76.43.78/p2p/PP_detalis_726716942049.pdf.exe where a payload containing Zeus is dropped onto the machine if any number of known vulnerabilities are present.
Once executed, the program starts listening on ports 9296 and 3198 while simultaneously contacting over 20 different Command & Control servers located at various IP addresses. Like most variations of Zeus, this malware variant targets confidential information on infected computers including system information, online credentials and banking details.
This version of Zbot is responsible for millions of dollars in theft around the world as hackers obtain online banking credentials and initiate wire transfers to offshore accounts before the victim is even aware that they have been hacked.
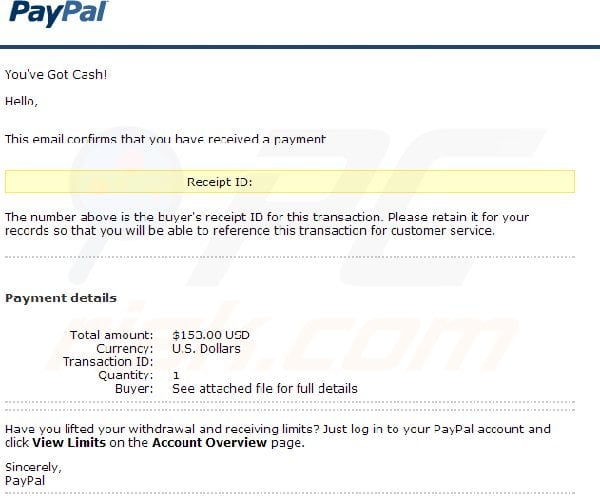
At this time, the threat seems to be primarily targeting computer users in the United States, but there have also been infection reports in the European Union. In addition to the threat presented by a Zeus infection, the spam email also attempts to gather PayPal credentials from users using a spoofed PayPal sign-in page to fool victims into entering username and password combinations for valid PayPal accounts. This occurs while Zeus is downloaded and executed in the background.
Unfortunately, PayPal does not offer customers many of the security features afforded to traditional online banking customers. This means that hackers can easily withdraw the funds from a compromised account without the knowledge of the victim.
That said, PayPal is usually quick to freeze account assets if a security breach is detected – although there is no guarantee that PayPal will catch the breach in time. Obviously, people who receive this message and do not use PayPal to process payments for online sales should be instantly suspicious of this spam email campaign. If you do use PayPal, it is much safer to use the Web browser on the computer to navigate directly to PayPal.com rather than follow a potentially malicious link embedded within an email.
Norwegian Facebook Virus Spreading Quickly
15.05.14
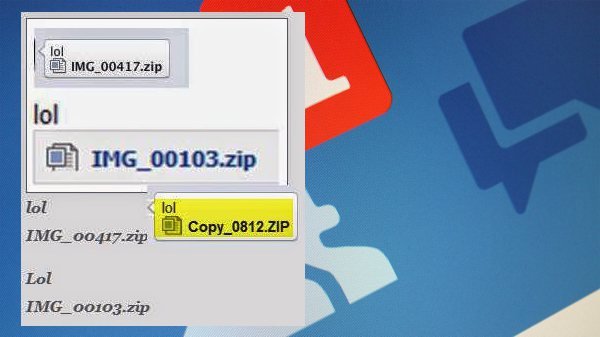
In the last few days, a new malware threat has been detected that targets users of the popular social media platform Facebook. Security experts in Norway discovered the threat but the global nature of social media means this new threat could be targeting victims in the United States very soon. The threat is so serious that Vidar Sandland from the Norwegian Centre for Information Security (NorSIS) has called the malware a “Norwegian phenomenon.” Unlike most Facebook scams that require users to click on a link usually leading to a malicious website full of drive-by downloads and phishing schemes, the new virus is transmitted via Facebook Instant Message. The message looks like any other private Facebook message but at this time the message comes from an unknown sender.
In the future, the hackers behind this scam could hack legitimate Facebook accounts and send the message to all “Friends” in the compromised account. This would significantly increase the number of infections as people are less weary of clicking on links from people they know. The text of the message simply reads “LOL” and includes a file labeled as a picture. When looking at the file, however, it is actually a self-executable ZIP file containing a Java program that immediately extracts and installs itself when clicked.
As is the case with many new malware creations, this virus isn’t designed to steal personal information or hold personal documents and files for ransom. Rather, the malware immediately begins mining for multiple crypto currencies including Bitcoin and Litecoin once installed. The malware does not notify the victim of any infection. In fact, the only way to tell if a machine has been infected is when performance problems begin to take over.
Mining for crypto currencies requires a large amount of processing power (usually the Graphics Processing Unit or GPU is used for best results). As the malware attempts to solve complex mathematical algorithms using the hardware resources of the infected machine, the computer is no longer capable of functioning smoothly during normal operations.
Other telltale signs of infection are if the computer suddenly becomes much noisier as the fan works extra hard to keep the GPU cool. If an infected computer successfully solves the algorithm (either by itself or as part of a mining pool), it is awarded all or part of a block of coins. In some cases, these blocks can be worth $10,000 or more each. Although mining for crypto currencies is perfectly legal, the competitive nature of the business means that most people cannot afford the expensive specialized hardware required to actually turn a profit. By deploying a powerful virus like this through a very popular media platform, the hackers could have millions of computers working to solve crypto currency algorithms – hardware worth millions of dollars in processing power. Of course, this money is sent directly to the hackers as it is discovered and the victims are left to deal with increased power consumption, slow computer performance and excessive hardware usage that could lead to failure.
Fortunately, the virus is relatively easy to remove using popular antivirus software or even directly through the command line. The problem is that only the most astute computer users even realize there is a problem as most modern computers have enough processing power to perform mining operations in the background with only a marginal performance decrease.
Either way, these hackers stand to become extremely wealthy from this virus – especially if it makes its way to the US and other densely populated countries. Avoiding this scam is simple: do not click on any links through the Facebook Instant Messaging service unless you are 100% sure of the messages origin.
Change your eBay Password Now!
18.05.14
Online auction giant eBay confirmed Wednesday that its corporate network was hacked by an unknown group of assailants. During the attack, a database containing users’ personal information (including passwords to access the eBay site) was compromised. eBay claims that there is no evidence to suggest that user financial information was accessed during the attack, but if you are familiar with the popular e-commerce site you probably realize that with the correct password, a hacker has easy access to most payment information stored on eBay as well as access to mailing addresses, phone numbers and possibly even more personal data including Social Security numbers because eBay requires this information from users planning to sell items on the site.
Another concern is that eBay owns PayPal; easily the most popular payment method used on eBay by both buyers and sellers. According to PayPal, that data is stored separately on a secure network and that all financial data is encrypted; however, it doesn’t mean a hacker couldn’t fraudulently purchase items using PayPal credentials stored within the account. Although making an eBay purchase using PayPal requires a user to enter PayPal login credentials during the checkout process, many eBay users maintain the same username and password combinations for both sites.
The breach occurred between late February and early March and the initial forensic analysis performed by eBay security personnel suggests the hackers were able to gain access to several eBay employee accounts which provided almost unlimited access to the corporate network without detection.
At this time, eBay is urging all customers to change login passwords using “email, site updates and other marketing channels.” eBay communications also suggest changing the same or similar passwords used for other sites such as PayPal.

EBay insists that there is no evidence that the stolen data has resulted in any unauthorized activity at this time – a statement which is rather hard to believe given that the company only now realized that a breach occurred months ago. It’s worth noting that the stolen passwords are encrypted according to eBay, but all a hacker would need to bypass this is a dictionary program or access to the private encryption key (which they may have found during the breach).
If you are one of the 128 million users of eBay around the world, change your passwords now. If accessed by a hacker, your account provides practically everything needed to completely steal your identity.
Best case scenario, you could end up paying for fraudulent purchases which may or may not be covered by eBay Buyer Protection guidelines or PayPal regulations (PayPal is classified as a payment processor – not a bank – meaning that many of the federal protections afforded to bank customers are not extended to PayPal services). In addition to changing passwords, users should remain vigilant for any unauthorized activity on eBay, PayPal and any other payment methods saved to their eBay account as the full ramifications of this breach may not have been realized quite yet.
BlackShades Malware Bust Shows Just How Dangerous the Trojan Really Is
23.05.14
Law enforcement officials from 19 countries recently collaborated to arrest almost 100 hackers charged with creating, distributing and using a dangerous Trojan known as BlackShades. During the raid, law enforcement personnel searched nearly 360 homes and confiscated over 1,000 storage devices. They also recovered large amounts of cash, illegal firearms and drugs according to Europol (the European Union’s law enforcement agency). BlackShades is a malware variant that works as a Remote Access Tool (RAT). Once installed, the Trojan allows hackers to remotely control a victim’s computer and monitor normal browsing activity, keystrokes and username/password combinations without the knowledge or consent of the victim.
This dangerous program can also remotely activate the victim’s webcam, snoop through files and directories and even encrypt files similar to ransomware programs like Cryptolocker. According to the FBI, BlackShades has been in circulation since 2010 and has been responsible for compromising over 500,000 computers in more than 100 different countries. One of the hackers caught in this bust was an 18-year-old man from the Netherlands who has single-handedly infected 2,000 computers and used the webcams to take compromising photos of both women and girls using the infected computers.
This particular RAT is extremely dangerous because it is so easy to use. In fact, it was actually developed by two men (according to the FBI) with the intention of allowing anyone to become a cybercriminal – even people without previous computer programming or networking experience.
Literally, an individual with no prior coding experience at all can deploy BlackShades within a matter of hours. Once one machine has been successfully infected, the RAT uses “spreader” tools to increase the number of infected machines. These spreader programs use resources from the infected machine to infect other vulnerable computers on the same network and across the Internet. This is why someone with no experience could quickly gain complete remote control of hundreds or even thousands of computers.
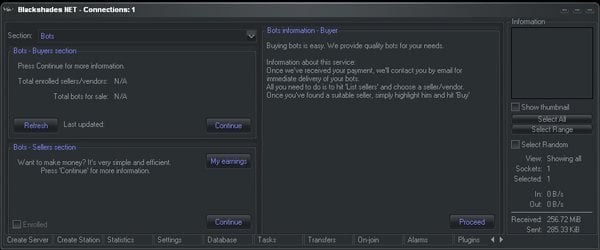
Also, unlike many of the Zeus variants which can cost thousands of dollars for a license, some versions of BlackShades can be purchased for as little as $40. For a slightly higher price, customer also receive access to a live forum where they can receive assistance configuring and deployed BlackShades.
It is estimated that since late 2010, BlackShades has generated over $350,000 in sales and millions of dollars in losses for victims. Online banking details have been stolen and used to empty accounts, compromising pictures have been used as blackmail and personal files have been encrypted for ransom.
This joint law enforcement effort takes many of the major BlackShades players out of the equation, but at the time of this writing the program is still for sale via quite a few popular hacking forums – complete with live forum assistance for those who need extra help becoming a prolific cybercriminal. BlackShades is not a new form of malware, but the recent bust demonstrates just how powerful some Trojans can be (even in the hands of inexperienced hacking “wannabes”). Most legitimate antivirus software already detects this Trojan but make sure all malware definitions are updated frequently and avoid potentially malicious websites to prevent incidental installation of BlackShades or another variant.
Fake Heartbleed Removal Tool Circulates as Spam Email
26.05.14
A little over a month ago, this blog reported the OpenSSL vulnerability that has become commonly known as the Heartbleed bug. The exploit uses a recently discovered vulnerability in OpenSSL’s implementation of the TLS/DTLS heartbeat extension – allowing hackers to read portions of the affected server’s memory. Information compromised during a Heartbleed exploit can include sensitive user information including usernames, passwords and other personal information that can be used (in the wrong hands) to commit an assortment of cybercrimes ranging from identity theft to sending spam emails on behalf of the victim.
The reason why this ‘history’ lesson of Heartbleed is important is because this vulnerability is not a virus or other form of malware. It is simply a vulnerability – which has been fixed by nearly every affected server already – that can expose personal information. It does infect individual computers like a virus, Trojan or Botnet would; however, that hasn’t stopped hackers from creating a new spam campaign that attempts to capitalize on the media craze surrounding the Heartbleed bug.
The spammers behind this campaign are specifically preying on less-savvy computer users who may have come across a headline or two about the Heartbleed bug but do not understand it has nothing to do with their actual computer.
The spam email basically attempts to scare unsuspecting users into downloading and installing “Anti-Heartbleed” software on their machine. This malware attachment is actually an encrypted executable file that once downloaded, installs a clandestine key logger in the victim’s computer.
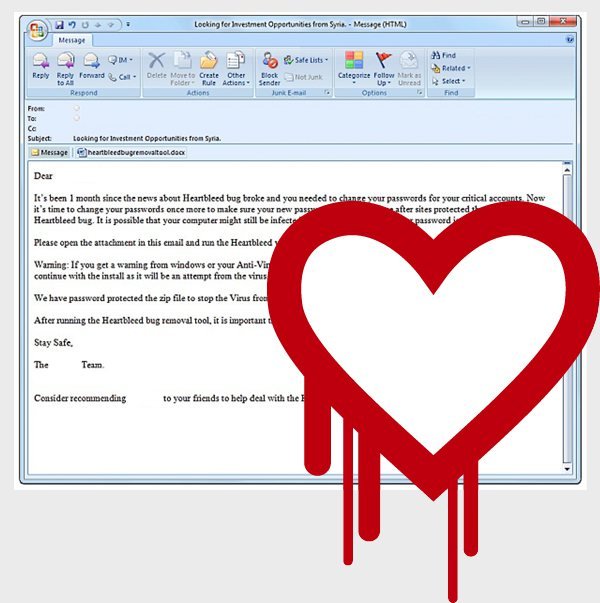
During the installation progress, users even see a progress bar showing a “Heartbleed Bug Scan” in progress before the program tells the user that Heartbleed wasn’t found on the machine.
Unfortunately, the key logging software remains installed – sending keystrokes, screenshots and other personal information to the criminals behind this scam.
One of these emails was intercepted by a leading Internet security company and reads like this:
Dear XXX,
It’s been 1 month since the news of the Heartbleed bug broke and you needed to change your passwords for all critical accounts. Now it’s time to change your passwords once more to make sure your new passwords are in put in place after sites protected themselves from the Heartbleed bug. It is possible that your computer might still be infected by the virus and as such your password is at risk. Please open the attachment in this email and run the Heartbleed virus removal tool inside. Warning: If you get a warning from Windows or your Ant-Virus that the file might harm your computer, please ignore this warning and continue with the install as it will be an attempt from the virus program to stop you from running the tool. We have password protected the ZIP file to stop the virus from removing the program before you can run it. The password is: cleaner. After running the Heartbleed bug removal tool, it is important that you change your password immediately.
Stay Safe,
The XXX Team
As you can see, this spam email is very convincing and is written using relatively good English (unlike make of other spam campaigns this blog has covered in the past). For people unfamiliar with the exact nature of the Heartbleed bug, this email could seem completely legitimate and it even warns users to ignore any warning issued by Windows or antivirus software before executing the program. Once installed, of course, the victim is also prompted to change all passwords but this time, a key logger is installed.
Victims are likely to immediately frequent important sites including social media and banking services where the criminals behind this scam can record any and all password combinations entered before using the stolen information nefariously.
To avoid this threat, never download or install any attachments from an unsolicited source and more importantly, realize that the Heartbleed bug does not affect individual computers so there is absolutely NO REASON to scan your machine for such a virus.
Banking Trojan Disguised as Popular Instant Messaging App for Android
27.05.14
Although WhatsApp – an instant messaging service recently acquired by Facebook – remains the most popular instant messaging application in the Play Store for Android devices, the Chinese-developed WeChat isn’t far behind in terms of number of global users and overall popularity. And it is for exactly this reason that hackers recently targeted this application as a way to deploy a dangerous new type of banking Trojan that is being referred to by security experts as Banker.AndroidOS.Basti.a. The company distributing the authentic version of WeChat – Chinese company Tancent – has declared that they currently have 355 million active WeChat users around the world.
In addition to allowing friends and family to chat using readily available Wi-Fi networks around the world, the legitimate WeChat app also allows users to send payments for goods and services without the high fees often associated with other payment processors.
Users of WeChat are required to enter payment information upon starting the app for the first time as a way to send money to others or simply to unlock additional features within the application. It is for this reason that a yet to be identified group of hackers has created a fake WeChat app that looks identical to the authentic version with one exception: it attempts to steal the financial information entered during app configuration.
Anyone familiar with how applications are installed on an Android device should know that before installation the OS prompts users with the permissions required by the application. The user must agree to these permission requests before installation can continue. The creators of the fake version of WeChat have successfully mimicked the permission requests of the real app as well; making it nearly impossible for a potential victim to tell the difference between the real and fake versions.

Once installed, the app asks users to enter personal information including phone numbers, credit card information, PINs and other pertinent financial data. This data is then sent to an email address that has been hardcoded into the app and first discovered by researchers at Kaspersky Labs. Upon logging into this account, researchers determined that the app already has thousands of victims without any end in sight. This Trojan is made even more dangerous because of the complex obfuscation techniques used by the malware authors. This makes it nearly impossible for mobile antivirus suites to detect the malicious app or to remove it if and when it is discovered.
Finally, this malicious app is capable of receiving SMS messages from the phone and disabling broadcasts on the device. This means that infected users might not receive important SMS messages from online banking services participating in two-factor authentication security methods specifically designed to protect against these phishing tactics.
The only way to avoid downloading this and other potentially malicious fake applications is to ensure that apps are only downloaded directly from the Play Store. Any and all third-party app stores are susceptible to unknowingly disseminating this rogue app and the results can be financially devastating.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion