News Archive December 2014
Monthly Cyber Security News Archive: December 2014 Summary
Table of contents:
- Regin Malware Targets Non-English Speaking Countries...For Now
- Citadel Banking Trojan Revamped to Target Password Management Applications
- CryptoPHP Creates Backdoor for Popular Content Management Systems
- Destover Malware Linked to Sony Pictures Attack
- New POS Malware Discovered Just in Time for the Holiday Shopping Season
- Ransomware Revised Again!
- Holiday Scams Already in Full Force
- Understanding Misfortune Cookie
- Information Stealing Trojan Becomes More Evasive
- ISIS Hunts Victims Using Rudimentary Malware
- Modified Zeus Trojan Targeting Online Banking Systems
Regin Malware Targets Non-English Speaking Countries...For Now
01.12.14
Regin is an extremely difficult to detect malware variant that is already being referred to as the ‘Swiss army knife of clandestine tools’ by security experts worldwide. The good news — if there is any when talking about this dangerous malware variant — is that Regin specifically targets non-English speaking countries. That said, it’s still worth looking at this malware because history has proven time and again that what works in other countries certainly works in the United States and other English-speaking countries around the world. In other words, it’s only a matter of time before Regin (pronounced “region”) makes its way onto domestic soil.
Originally discovered by the well-known anti-malware company Symantec and described in a paper released by the aforementioned last week, Regin is designed to steal secret documents and communications from foreign governments around the world. What makes Regin so special (in fact, Symantec even refers to the malware as “groundbreaking” in its report on the subject) is the targets the malware attempts to infiltrate. Primarily, Regin seeks to infect telecommunications firms, critical infrastructure providers including nuclear power facilities and large corporations such as military contractors and other government-affiliated agencies.
The malware is so effective that it has been working behind the scenes and avoiding detection since 2008 according to Symantec.
Interestingly enough, Regin appears to be designed so that it avoids targeting English-speaking countries including the United States, Canada, the United Kingdom, Australia and New Zealand. This has already led many security experts to compare Regin to Stuxnet — a malware program purportedly created via a joint effort between the United States and Israel as a way to disrupt Iran’s nuclear program. At the time of this writing, most of the detected infections are in Germany, Saudi Arabia, Syria, Brazil, Mexico, Belgium, India and Ireland.
Although many of these countries aren’t sworn enemies of the United States, the complexity of the malare and the fact that English-speaking countries aren’t being targeted at this time does raise questions about the origin and ultimate purpose of this dangerous malware variant. Perhaps the true silver lining of Regin for most PC users is that the malware is unlikely to be used by ‘traditional’ hackers looking to steal consumer identities to make a quick buck. This because security researchers believe that Regin is simply too complicated to copy and repurpose by run-of-the-mill cybercriminals looking to make a quick buck at the expense of the average Internet user.
Although the primary target of Regin appears to be large businesses and government entities, there have been some reports that the malware has targeted individual users; most likely in an attempt to acquire sensitive information including login credentials to corporate assets controlled by the targeted individuals.
That said, there is no denying the fact that Regin is powerful and extremely difficult to detect. If you own or are employed by a business with satellite offices in a targeted country (this mainly applies to military contractors that conduct global business every day), ensure that all sensitive communications are encrypted using the latest security standards to avoid having these messages compromised by Regin on the other end.
Citadel Banking Trojan Revamped to Target Password Management Applications
03.12.14
Citadel is a powerful banking Trojan that has been covered extensively on this blog in the past. A variation of the notorious Zeus Trojan, Citadel came into its own after the original Zeus source code was leaked online last year. While the widespread use of Citadel has waned due to improved detection by most popular anti-malware solutions, it is still a threat that should be remembered every time you open an unsolicited email attachment or visit a website that could be compromised by popular drive-by download exploit kits such as Blackhole.
But now there is yet another reason to fear Citadel as a new variant has been discovered in the wild that could bring Citadel back into the spotlight as a serious threat that could be lurking around every proverbial corner of the Internet. This new threat, which was recently discovered by security researchers at Trusteer, a subsidiary of IBM, doesn’t target the passwords used to log into online banking sessions.
Instead, this modified version of Citadel targets popular password management applications that were specifically designed to circumvent much of the risk associated with entering your password to initiate an online banking session.
Specifically, Citadel 2.0 (as it is being called by some security researchers) activates a keylogging program whenever specific executable files are detected on the operating system of the infected machine. The programs that activate Citadel include Personal.exe, PWsafe.exe and KeePass.exe. Personal.exe is a program associated with the neXus Personal Security Client; an application that provides cryptographic APIs for online applications that communicate with authentication cards inserted in the PC. According to the manufacturer, this allows users to perform sensitive operations from anywhere without fear of the information being intercepted by cybercriminals during transmission. PWsafe.exe works with an open-source password management application called Password Safe.
This application is used by consumers and businesses alike to keep track of and enter passwords automatically. Likewise, Keepass.exe is associated with another open-source password management application called KeePass. Most password management applications (including those mentioned above) are designed to store passwords for numerous web login sessions. In addition, these programs have form-filling capabilities. The idea behind these programs is that the user is protected from filling out this information directly — thereby eliminating the threat typically posed by keylogging software.
Unfortunately, users are usually required to enter a master password for the password management application before the program becomes active during a Web session. It is this master password that this new variation of Citadel is after.
When successfully captured, this master password gives hackers access to all passwords stored within the program as well as any personal details used to fill out Web forms automatically. In many ways, this makes Citadel 2.0 even more dangerous than the original version which only targeted victims actively attempting to log into an online banking session (and even then, only at specific online banking sites as described in Citadel’s source code). Most modern password management systems offer two-factor authentication. To avoid falling victim to this new version of Citadel, ensure two factor authentication is turned on — this should prevent hackers from gaining access to any sensitive personal information stored within the password management system.
CryptoPHP Creates Backdoor for Popular Content Management Systems
06.12.14
Security researchers have recently discovered thousands of plugins and themes for popular content management systems (CMS) including Wordpress, Joomla and Drupal that have backdoors engineered into them that can be used to compromise web servers around the world. The backdoor, known as CryptoPHP, has been added to popular plugins used by webmasters to improve the functionality of websites using the popular CMSs mentioned above. Websites based on Drupal are only susceptible to CryptoPHP via infected themes. Websites based on Wordpress and Joomla, however, are also susceptible to infection via thousands of plugins specifically designed for the platform in question.
The hackers behind this attack use a simple social engineering trick to victimize website administrators into downloading popular plugins and themes that have been infected with CryptoPHP.
Site administrators are often lured into downloading these infected versions via websites that purport to offer pirated versions of plugins that may be out of financial reach for many of these website owners.
Although these “pirated” versions are fully functional, they include CryptoPHP. Unfortunately, most popular CMS platforms do not have adequate anti-malware protection. In other words, CryptoPHP is installed directly on the web server without the knowledge of the site administrator responsible for installing the rogue plugin or theme. What happens next is completely up to the hackers responsible for disseminating CryptoPHP in the first place.

Once successfully installed, CryptoPHP allows hackers to control the web server using a standard command and control (C&C) server, email or even manual control via CryptoPHP’s own user interface. Obviously, the amount of time hackers spend on a particular compromised web site depends on the perceived value of the site in question. The more powerful the site, the more likely it becomes that hackers will leverage CryptoPHP for a variety of nefarious purposes.
Other features of CryptoPHP include:
- Public key encryption between compromised web server and C&C server
- A large, extensive C&C infrastructure comprised of multiple IP addresses (to make detection much more difficult)
- Email communication backup in the event a C&C server is taken down
- Manual control of web server via CryptoPHP’s custom interface
- Ability to remotely update list of C&C servers
- CryptoPHP can also update itself as needed
So far, it seems that most of the sites infected with CryptoPHP are being used as a way to increase search engine traffic to other sites controlled by the hackers behind this malware — primarily using black hat SEO techniques that usually result in the compromised site being penalized by search engine algorithms. Although the exact number of sites currently infected with CryptoPHP is still unknown, FoxIT - the security firm responsible for discovering CryptoPHP — estimates that thousands of sites have already been compromised at the time of this writing.
If you currently manage a website (either personal or professional), you can avoid compromising your own site by avoiding pirated versions of popular plugins and themes.
Although it may be tempting to save a few bucks by downloading pirated versions, the risk of installing CryptoPHP and losing control of your own site simply isn’t worth the risk. Only purchase plugins and themes from reputable sources such as the original creator or through other verified sources such as the plugin store available in the backend of your CMS of choice.
Destover Malware Linked to Sony Pictures Attack
07.12.14
Destover, also known as Wipall, has been identified as the malware used in the attack against Sony Pictures Entertainment late last month. This attack was responsible for wiping the hard drives of numerous PCs within the company’s network before rebooting each infected system and displaying a copy of a bitmap image announcing to employees that the network had been hacked by a group calling itself the Guardians of Peace (GOP). Shortly after the Sony attack made headlines, the FBI issued a warning stating that a destructive – but unidentified – malware attack had been launched against a prominent US business (which was also not named within the warning). Following the breach, an email was sent to the Information Security Media Group by an individual claiming to be the leader of GOP.
This email stated that the group of hackers planned to leak “tens of terabytes” of Sony data that was stolen prior to Destover wiping the hard drives. As of this writing, however, it appears that the hackers have only leaked approximately 30 GB of data including high quality digital versions of unreleased movies and sensitive internal documents containing employee financial information. What security experts have been unable to figure out is exactly how GOP was able to extract so much sensitive data during the breach.
Destover is designed only as a way to wipe hard drives and so far no additional modules have been identified that would have given the group the ability to steal information.
That said, the fact that Destover wipes the hard drive limits the forensic evidence available as security researchers try to put the pieces of this puzzle together. What is known at this time is that GOP was apparently very familiar with Sony’s network topology and architecture prior to the attack. From the bits and pieces of malware left over following the attack, security researchers from AlienVault were able to identify several hardcoded server names specific to the Sony network. 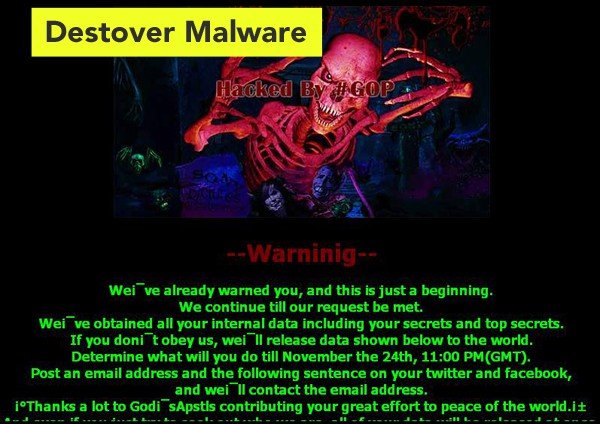
Username and password combinations (also specific to the Sony network) were also found to be hardcoded within this particular distribution of Destover. In other words, it appears that the attack against Sony may have included the work of one or more insiders; although security experts caution that the attack could have been strictly external assuming GOP conducted thorough reconnaissance of the network prior to launching the attack last month.
It is unknown where the hackers calling themselves the Guardians of Peace originate, but IP addresses found within the malware samples released by the FBI point to servers located in Italy, Singapore, Poland, the United States, Thailand, Cyprus and Bolivia.
Most likely, these systems were hacked or compromised via a Virtual Private Network (VPN) as a way to hide the origin of the attack. What this attack proves is that with enough resources and time even some of the most robust networks in the country can be compromised quickly and easily by skilled cyber criminals. As the holiday season draws near, concerns about the safety of corporate networks becomes a paramount concern for security analysts, businesses and consumers alike.
New POS Malware Discovered Just in Time for the Holiday Shopping Season
09.12.14
Security experts recently discovered a new type of point-of-sale malware similar in design to the devastatingly powerful BlackPOS malware which affected target and many other US retailers during the holiday shopping season of 2013. As you may recall from the coverage of the Target breach on this blog last year, the personal details of over 40 million customers were compromised when hackers were able to infect the point-of-sale system with BlackPOS. Compromised information included email addresses, credit card numbers and billing information which was then sold through a variety of “carding” websites around the world.
The newly discovered malware, known as LusyPOS, was originally found on Virus Total – a website where people can submit malware samples to see if they can be detected by a combination of several dozen security applications. The malware has also been seen on various carding websites where people can buy and sell stolen credit card information. What’s most concerning about LusyPOS is that it is available via these underground markets for as little as $2,000. At this relatively low price, it becomes entirely feasible for even inexperienced cyber criminals to launch powerful point-of-sale attacks on retailers during the busiest quarter of the fiscal year.
One trait that is exclusive to LusyPOS is that it uses the Tor network for communication between command-and-control servers and infected POS systems.
Tor encrypts the content sent between both locations which makes detection more difficult while providing another layer of security for the hackers controlling the malware. Although Target was one of the hardest hit retailers last year, Home Depot also fell victim to a malware variant with striking similarities to LusyPOS. According to recent reports, this new malware variant shares many similarities to other well-known POS malware programs including Dexter and Chewbacca.

Many of these malware variants are extremely simple in design, but have been used effectively against a variety of US-based retailers. Chewbacca, for instance, was responsible for infecting the systems of at least 35 retailers last year. It appears that LusyPOS shares some characteristics inherent to Dexter and others commonly associated with Chewbacca to create a new malware threat from existing source code. Perhaps this is why the malware is available for a mere $2,000 – a price point which is sure to appeal to amateur cyber criminals and/or hacking wannabes. Although these groups usually do not pose a serious threat to major corporations, the availability of a powerful POS malware solution means that this holiday shopping season could be even more dangerous for retailers and consumers than 2013 proved to be.
Whether you do most of your shopping in traditional brick-and-mortar locations or via online shopping platforms, the best way to protect yourself from leaked financial information is to remain extremely vigilant throughout the shopping season and into 2015.
Regularly check bank and credit card statements and immediately report any discrepancies to your bank or other financial institution to avoid significant financial losses that may occur if your payment information is stolen by LusyPOS, Dexter, Chewbacca, BlackPOS or some other yet unidentified malware variant specifically designed to target point-of-sale systems of retailers around the country.
Ransomware Revised Again!
12.12.14
This blog has covered many different varieties of ransomware in the past including Cryptolocker, Reveton and CryptoWall (just to name a few). As ransomware continues to be a popular attack venue for cyber criminals, we have seen many variations of similar source code. This phenomenon is not exclusive to ransomware - in fact, most modern malware threats share source code and hackers simply add small variations to make them undetectable by modern antivirus solutions and increasingly savvy PC users. That said, security researchers from SophosLabs recently uncovered a new form of ransomware that is actually new.
This new malware threat, known as VirRansom, is spread in the same way as most other ransomware variants. Specifically, spam email campaigns with malicious attachments are often used to target potential victims or zombie malware (malware which sits dormant on a system until commanded by a C&C server to download the ransomware program) are being used to disseminate this new threat.
But while the distribution methods are the same, the way this malware acts once installed on a target PC is completely unlike any other ransomware that has been seen in the wild.
Most modern ransomware is officially classified as a Trojan or worm. Both of these malware variants simply make copies of themselves on the infected system but do not actively target uninfected files. VirRansom, on the other hand, is a true virus. In other words, it is a self-replicating parasite that spreads on its own and actively seeks other programs which can be modified to include a copy of the virus using the original file as a host.
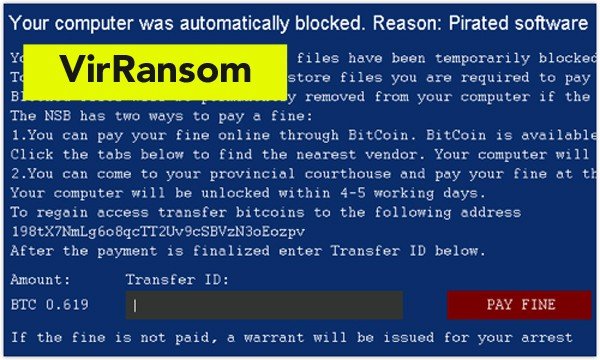
Not only does this technique work extremely well, but it is also very difficult to stop the process of infection once it has begun. This is especially true of this new ransomware threat because it is capable of infecting program (.exe) files as well as ZIP, DOC and JPEG data files. These data files are encrypted, wrapped in an .exe shell and renamed to include the executable extension. The virus also make sure to reset the newly infected file’s icon so that it matches the original file. This technique alone makes it nearly impossible for the average PC user to avoid opening what appears to be a completely safe file from a trusted source. Once a VirRansom file is opened, however, this dangerous piece of malware gets to work. Some of the features that have already been discovered by security experts include:
- permanent installation on the hard drive using random filenames
- creation of a registry entry that allows the virus to run even after logging out or rebooting
- ability to activate itself by loading specific processes into system memory
- actively looks for accessible files that can be infected (including network and removable drives)
- ability to run two distinct malware processes simultaneously that are capable of restarting one another if one process is killed off
- prevents user from accessing any files or folders on the computer until the specified ransom is paid using standard encryption methods
As you can see, this new ransomware threat is much more sophisticated than some of the other ransomware that debuted earlier this year. Like all other ransomware, however, this program will encrypt files and make the computer unusable until the ransom (payable in Bitcoins only) is paid by the victim.
Unfortunately, the fact that this malware possesses the ability to spread within a network autonomously makes it extremely difficult to eliminate once infection has occurred.
While most antivirus software is incapable of detecting VirRansom at this time, virus definitions for most anti-malware solutions should be updated within the next couple of weeks. In the meantime, remain extremely vigilant and avoid downloading any questionable attachment or visiting any potentially malicious websites as either media could contain a copy of this dangerous new ransomware threat. One of the variants of VirRansom is named "Operation Global 3", computer users who are dealing with this infection can follow our removal guide for this threat.
Holiday Scams Already in Full Force
15.12.14
As the holiday shopping season continues to build in these final weeks of 2014, hackers and cyber criminals around the world are up to many of the same tricks they use every year around this time in the hopes of tricking unsuspecting victims into downloading malicious and potentially dangerous malware. One of the most prevalent scams this year is being referred to as “malicious order confirmation emails.” As the name implies, spam email campaigns designed to mimic correspondence from popular retailers are the primary means of disseminating an array of known malware variants including the notorious Asprox Trojan – a dangerous piece of malware that can harvest email credentials and other passwords from infected machines.
The Trojan also turns the infected PC into a zombie that can be used to relay junk email that ultimately perpetuates Asprox malware infections around the world. Another feature of Asprox is a newly deployed scanning module that forces infected PCs to scan the Internet for websites that may be vulnerable to common exploits. When found, these websites are usually targeted by the hackers as an additional host for the malicious links contained within the spam emails used in this campaign.
Although the hackers behind these latest attacks (which initially were detected right around Thanksgiving) could use any retailer for the scam, they have chosen to use some of the largest big-box retailers in the country in the hopes of luring more victims.
As of this writing, Home Depot, Walmart, Target and Costco seem to be the most popular retailers used when sending fake order confirmation emails.
The idea behind this attack is a combination of email attachments – ZIP files containing Asprox and other malware variants – and links to malicious sites using popular exploit kits to remotely install Asprox via known vulnerabilities in popular web browser plug-ins such as Java, Flash and Microsoft Silverlight. While the language of these emails tends to change frequently, a recent malicious email was intercepted that purported to be from Walmart. The email read as follows:
This letter is to advise you about the order we have which is addressed to you. You have 4 days to pick it up in any Local Store of Walmart. Please, follow this link for more information about your order. Walmart is wishing you Happy Holidays!
This email contains a link which redirects victims to a rogue website hosting Asprox that relies on the Blackhole Exploit Kit to create a drive-by malware download situation that focuses on common vulnerabilities and zero day exploits to silently install this dangerous Trojan botnet onto the target PC. Most of these emails contain subject lines such as “Acknowledgment of Order,” “Order Confirmation,” “Order Status,” “Thank you for buying from [insert merchant name here]” and “Thank you for your order.”
To avoid falling victim to the scam, be extremely careful when you receive an email from a retailer this holiday season – even if you have legitimately purchased something from this retailer recently. A legitimate order confirmation email will usually include your personal information and an order number; not just a generic message often containing poorly written English.
If there any doubts about the legitimacy of an email, the best course of action is to open a web browser and navigate directly to that retailer’s website for more information.
Clicking on attachments within the email or links that lead to potentially malicious external websites will most likely lead to infection by Asprox or another dangerous malware variant this holiday season.
Understanding Misfortune Cookie
18.12.14
A security flaw was recently uncovered that could affect 12 million businesses or more in the coming months. The critical software bug, which has been named the ‘Misfortune Cookie’, affects routers, modems and other gateway devices as well as other devices connected to the same network. Devices that could be affected indirectly by Misfortune Cookie include PCs, smartphones, tablets, printers and an assortment of smart devices such as TVs, refrigerators and thermostats. The security flaw resides not in the device, but rather in a web server (RomPager by AllegroSoft) typically embedded in the affected devices firmware.
This web server is used in millions of Internet-enabled devices by practically every leading manufacturer. This server is responsible for rendering the web-based administrative panel used when making configuration changes to the device. Security experts have discovered that RomPager versions 4.34 and below are vulnerable to this bug which got its name when because hackers are able to control the fortune of HTTP requests by modifying and manipulating cookies.
Officially dubbed CVE-2014-9222, Misfortune Cookie works by sending a specially crafted request to the Web server that immediately corrupts the device’s memory – giving the hacker complete administrative control.
With control of the affected device, a hacker could target any and all other devices on that network. At this point, the hacker is able to monitor Web traffic, steal sensitive personal and financial information, change router settings (including DNS settings) and even control webcams attached to the network (directly or indirectly). Although a complete list of affected devices is not yet completed, it is known that at least 200 different routers and/or gateway devices are vulnerable to this exploit.

Some of the popular manufacturers already identified as being affected by Misfortune Cookie include Edimax, D-Link, TP-Link, ZTE, Huawei and ZyXEL. This attack can be executed from anywhere in the world and it does not matter whether the Web-based administration panel is set to be available via the Internet or not – making this attack even more dangerous. Interestingly enough, the version of RomPager affected by this vulnerability is over ten years old. The vulnerability was discovered in 2002 and fixed in a subsequent release (2005).
Unfortunately, many manufacturers continue to use chips that were flashed with this old software version and are still vulnerable to this well-documented exploit at the time of this writing.
Although no attacks have been reported in the wild thus far, it is clear that hackers can leverage this vulnerability at any moment. If you think you may have a router, modem or gateway device affected by Misfortune Cookie, contact the manufacturer immediately to confirm whether or not the device is affected and if so, if a firmware update will be available in the near future. Firewalls and antivirus software cannot prevent this attack; only upgrading the firmware of the router or replacing it with a new model can protect your network from Misfortune Cookie.
Information Stealing Trojan Becomes More Evasive
19.12.14
As hackers continue to look for new ways to mimic the success of previous banking Trojans such as Zeus and the Gameover botnet, there hasn’t been a shortage of potential threats this year (many of them have been covered on this blog). Perhaps to end this year with a bang hackers recently introduced a new – and extremely dangerous – banking Trojan that uses some interesting techniques and continues to evolve into an increasingly dangerous malware threat even as you read this. This threat, known as Vawtrak, was discovered by security research company SophosLabs last month.
Vawtrak has already infected tens of thousands of PCs worldwide and is capable of draining a victim’s bank account extremely quickly due to state-of-the-art anti-detection techniques built into the malware’s source code. Vawtrak is so popular with cyber criminals right now that between the months of September and November of this year, it was reported via multiple sources that Vawtrak was the most widely detected malware infection – beating out any of the popular ransomware variants this blog as covered throughout the year.
While Vawtrak is nothing new to Internet security experts (it is part of the Gozi Prinimalka Trojan family), security researchers recently uncovered multiple new versions of this dangerous malware variant in the wild that have been updated to avoid detection and seek new targets.
These new versions disguise how they communicate with C&C servers to make Web traffic appear less suspicious while simultaneously disguising where, in fact, the C&C servers are located (which makes taking the cybercriminal network behind Vawtrak much more difficult). The C&C servers are hidden within the malware’s source code using pseudorandom numbers produced using a Linear Congruential Generator to scramble data.
This makes it more difficult for anti-malware software to detect suspicious incoming and outgoing transmissions and it also makes it very difficult for security personnel to locate the actual IP addresses of the C&C servers responsible for disseminating configuration files to infected clients. To make it even more difficult to detect this latest version of Vawtrak, the malware will only make outbound C&C requests once a browser is open on the computer. In this way, the traffic generated by the Trojan appears to be a simple HTTP request originating from the Web browser. The other concern about this new iteration of Vawtrak is that a series of new configuration files have been intercepted which indicate that the hackers behind these attacks are actively seeking out new targets.
New configuration files specifically target American banks including Wells Fargo, American Express and Fifth Third Bank as well as banks in the Czech Republic.
Yet undiscovered configuration files could direct Vawtrak to target PCs at the consumer level as well in search of personal and financial data. The most dangerous aspect of this malware is that it is evolving at a rapid pace and by hackers with very specific targets in mind (at least at this time). Like other Trojans, Vawtrak is primarily spread via spam email campaigns relying on infected attachments or links to malicious websites where drive-by downloading techniques are used to deliver the infected payload. Protect yourself from Vawtrak by ensuring all Windows and application updates are installed, maintaining an updated antivirus solution and avoiding any unsolicited emails that appear to be suspicious.
ISIS Hunts Victims Using Rudimentary Malware
21.12.14
It seems that even the notorious terrorist organization known as ISIS has resorted to using malware in its fight against groups it perceives to be hostile. Referred to by security experts as ‘Digital AK-47’, this malware strain has a simple purpose and has only been sent to select targets that publicly speak out against the reign of terror ISIS has been responsible for in many parts of the Middle East. Digital AK-47 was recently intercepted and analyzed by Citizen Lab (a University of Toronto Internet watchdog). So far, the malware has only been sent out to a small number of email addresses specifically targeting members of the group known as Raqqah is being Slaughtered Silently (RSS).
This group is responsible for campaigning against ISIS while being holed up inside territory controlled by the radical Islamic group. The email purports to originate from a Canadian expat group interested in helping RSS in the fight against ISIS. The rogue email contains a link to a malicious URL supposedly containing a report about ISIS activities in the Middle East, but instead redirects victims to a TempSend file sharing account where a ZIP file entitled slideshow.zip can be downloaded.
Interestingly enough, the malicious file does contain a few maps to distract victims, but the main purpose of this malware is a simple spyware program embedded within the archive known as AdobeR1.exe.
When run, this spyware program emails the infected PC’s public IP address to ISIS. Although the program does not provide a backdoor to access the infected system, knowing the public IP address could allow ISIS to use geolocation technology to find RSS members trying to remain hidden from the violent and bloodthirsty regime. Syria’s Internet access is relatively scarce meaning that mapping the IP addresses of particular locations shouldn’t be terribly difficult. In theory, ISIS could locate RSS members based on these IP addresses and launch an attack in an attempt to eradicate opposition within its territory.
That is, of course, is RSS members aren’t familiar with using Tor or a VPN to protect their location from these types of attacks. According to a senior analyst from Citizen Lab, the code used in this attack is very basic and contains multiple bugs. This typically indicates that the malware was developed in-house by ISIS personnel. For instance, this version of AdobeR1.exe only sends out the initial IP address discovered and the emails sent back to ISIS are not encrypted at all.
For lack of a better description, these are simply amateur coding errors which indicate internal development by ISIS affiliates without the programming skills to make truly dangerous malware.
Despite the simplicity of this attack, this malware proves that even the most basic of digital threats can have dangerous – sometimes even fatal – consequences for the victims of the attacks. It is for this reason that security experts call this attack and others like it the digital AK-47 – it is cheap, easy to use and very dangerous when in the hands of militant groups – just like the AK-47 of Russian fame.
Modified Zeus Trojan Targeting Online Banking Systems
28.12.14
Security researchers with Russian-based Kaspersky Labs recently discovered a new banking Trojan that appears to be yet another evolution of the notorious Zeus botnet. According to a report released by Kaspersky last week, the malware is currently targeting over 150 banks and 20 payment processors in 16 different countries – including the United States. Known as Chthonic and officially detected as Trojan-Banker.Win32.Chthonic, this new Zeus variant represents the latest cog in a constantly evolving malware campaign that focuses on major financial institutions around the world.
One of the things that makes this iteration so dangerous (and appealing to cyber criminals) is that it is constructed using a modular architecture. In other words, it is very easy for hackers to extend the functionality of the malware to aid in detection avoidance, create a more powerful keylogging engine or some other purpose that has yet to be discovered. The current version of Chthonic is extremely powerful already.
Features included in the version analyzed by Kaspersky include the ability to steal saved passwords from multiple applications, keylogging functionality (in applications and from Web pages), video and sound recording, form grabbing, code injection (usually during online banking sessions) and remote access to the infected PC using VNC technology to initiate online banking transactions.
Of all these tools, the Web injection module appears to be Chthonic’s primary weapon because it allows the hackers behind the malware to bypass the two-factor authentication used by most online financial institutions. Using this powerful module, attackers can modify Web pages already open in the victim’s browser – inserting additional fields as necessary to extract the personal information required to initiate an online wire transfer.

It is unclear which cybercriminal group is behind this attack, but experts believe that Chthonic may be for sale via the online black market because multiple botnets have been spotted using different C&C servers to relay commands to infected machines. These botnets also target financial institutions in very specific parts of the world; indicating that multiple groups around the world are leveraging the power of this dangerous malware variant at the same time. Banks in the U.S., Spain and the U.K. are being targeted heavily, but some botnets are focusing on financial groups in Russia, Italy and Japan as well.
The names of the banks being targeted haven’t been released at the time of this writing, but payment systems including Alipay, Webmoney and Chronopay have been confirmed as targets in this malware campaign.
Although the delivery method could change at any time, hackers are distributing Chthonic by installing a downloader on the targeted machine. This is accomplished using malicious email attachments that take advantage of known vulnerabilities in Microsoft Office products (CVE-2014-1761 has been used extensively in this attack) or by installing the Andromeda bot via a drive-by download. To avoid infection by Chthonic, ensure Windows and all associated applications are updated, avoid opening emails and/or attachments from unknown senders and use an Internet security solution designed to block drive-by downloads perpetrated by malicious Web sites.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion