New Malware Exploits User Account Control (UAC)
According to Microsoft, the User Account Control (UAC) security feature built into all modern Windows OS release is designed to help defend your PC against both hackers and malicious software. Whenever a program attempts to make a change to the PC, UAC notifies the user and asks for permission. When this occurs, users can allow the changes, decline the changes, or click a button that displays additional details about the program attempting to make the change and what specific changes the program is attempting to make. Unfortunately, many people simply choose ‘Yes’ without clicking the ‘Show details’ button first and this is exactly how a new proof-of-concept malware known as ShameOnUAC deceives victims. In most cases, UAC works very well. It often stops potential malware threats by not allowing installed malware to make any significant changes to the PC without the consent of the user. Of course, like most other PC security considerations, effectively using UAC means that the user must know when to allow changes via the privilege escalation prompt and when to decline these changes (i.e. when an unknown program attempts to make changes via the UAC prompt).
ShameOnUAC was developed by the Cylance SPEAR Team while the group was researching potential ways to subvert programs during privilege escalation via UAC. To understand how this malware works, it helps to understand how UAC works as it was originally intended by Microsoft:
1. A user asks Windows Explorer to launch a program using administrative privileges.
2. Since Explorer is running without admin privileges, it requests that the Appinfo service launch the program as admin.
3. Appinfo, in term, launches Consent, prompting the user to confirm the program using a secure interface
4. The user is asked to select ‘Yes’ or ‘No’
5. If Yes, Consent tells Appinfo to launch the program with admin privileges. If No, access is denied and the program is not executed.
Once ShameOnUAC malware has been installed on the PC, the exchange differs because the ShameOnUAC shell within Windows Explorer asks Appinfo to launch a legitimate program. The difference is that this request also includes arbitrary commands that could perform an assortment of nefarious tasks. The only way a potential victim can tell the difference is to read the ‘Show Details” button when the UAC prompt appears. That is, of course, if the user actually understands the rogue commands that have been added to the request for a legitimate program made by ShameOnUAC.
According to Microsoft, the Appinfo service was designed to facilitate the running of applications with admin privileges. In other words, when a program needs administrative privileges to operate, Appinfo triggers the UAC prompt that asks users whether they want the program to make changes or not. Cylance designed UAC to target cmd.exe (Windows Command Prompt) and regedit.exe (Windows Registry Editor), but Derek Soeder – a researcher for Cylance – states that “more targets are surely possible.”
When it comes to exploiting the Windows Command Prompt, ShameOnUAC ensures that the user still receives the expected admin command prompt once ‘Yes” is clicked on the UAC prompt. The difference is that the malware is allowed to run a command of its own first…with admin privileges.

ShameOnUAC works slightly differently when it comes to exploiting regedit.exe. In this case, the malware forces regedit.exe to install a separate .reg file before calling upon Appinfo. This results in a second [hidden] elevation request. According to Soeder, this additional request causes Appinfo to run a separate instance of the consent.exe process. This instance, however, runs as SYSTEM; in other words, with administrative privileges. This allows the ShameOnUAC library to run prior to prompting the user. The malware library then modifies the parameters sent to the ‘rogue’ consent.exe instance – in turn suppressing the consent prompt. Although the user still sees the Registry Editor window, ShameOnUAC has already executed commands with SYSTEM privileges. This means that the malware has already done its damage without the need for the user to actually click ‘Yes’ on the UAC prompt (because by this time the malware has already executed malicious code with admin privileges).
What makes this malware iteration so dangerous is that there is no way to mitigate the threat of becoming victim to this exploit because ShameOnUAC isn’t a vulnerability, it’s a feature. As such, it’s unlikely that a patch will be made available any time in the near future; unless Microsoft completely reinvents the way it implements UAC at the administrative level.
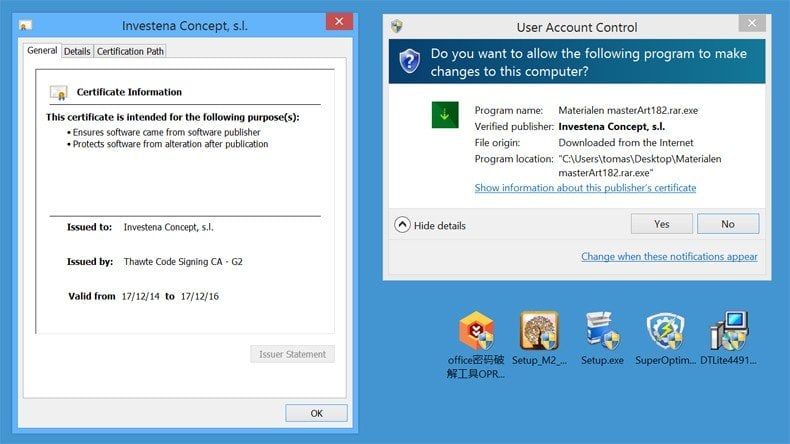
This threat is also concerning because it demonstrates that users could be unintentionally elevating malware from a mere dangerous to “game over”, according to Soeder. In every instance, the information that would alert a user to the threat is available if only users would get into the habit of checking the ‘Show Details’ box for any UAC elevation request. Although ShameOnUAC is a proof-of-concept malware threat that hasn’t been seen in the wild yet, the fact that security researchers from Cylance have published a detailed report about their findings means that ShameOnUAC could be implemented into a dangerous malware campaign in the near future. The only way to protect yourself from ShameOnUAC or any other malware threat that exploits the UAC service is to take a good look at the details of any privilege escalation request that appears. If there are any commands that don’t seem familiar or if the prompt is asking for permission to run a legitimate program that you haven’t explicitly opened, there is a good chance that this vulnerability is being exploited right before your eyes. Always decline any UAC privilege escalation request that seems suspicious as declining the request could be the very thing that protects your PC from yet unknown exploitation as a result of this inherent Windows vulnerability.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion