New ZeusVM Tool Allows Anyone to Build a Botnet
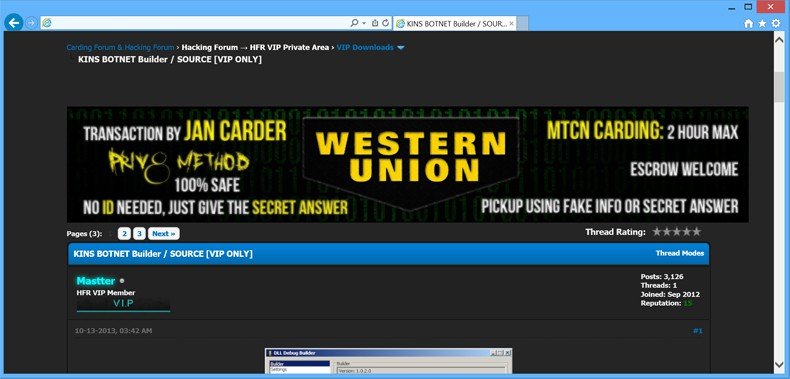
Back in June, security researchers discovered that the source code for both the building tool and control panel of ZeusVM had been leaked to the public. This leak means that anyone can build a Zeus-powered botnet without any programming knowledge. Initially, the leak was kept secret as security researchers from Malware Must Die (MMD) worked to keep these files from becoming widely available. Unfortunately, the leaked source code spread faster than the researchers could have imagined and as a result, MMD made information about the leak publicly available in an effort to alert security professionals around the world about this concerning threat. ZeusVM, sometimes also known as KINS, is a banking Trojan that works by hijacking the Web browser process. Once this process has been hijacked, the Trojan can modify and/or steal information being exchanged between the infected client machine and the server hosting the secure session.
Most of the time, Zeus is used to steal online banking credentials. As a victim logs into an online banking session, everything the victim enters via the keyboard is recorded and sent to the hackers operating the Zeus campaign. With this information, hackers are able to log into the hacked online bank account and initiate wire transfers to accounts in other countries. In most cases, the stolen funds cannot be recovered and unlike debit and credit card fraud, there is often no recourse for victims as far as getting their money back despite evidence indicating that fraud has occurred.
Although banking websites are the most popular target for ZeusVM, other websites can also be targeted as long as the cybercriminals behind the attack add these websites to the configuration file downloaded by the Trojan after initial infection. PayPal is another target popular with many hacking groups as are social media sites including Facebook and Twitter.
Although there may not be any immediate financial gain associated with hacking into a victim’s social media account, these accounts can often provide details necessary to commit identity theft. Also, the password used for the compromised social media site could very well be used by the victim for other services including online banking.
You may recall that the source code for the original Zeus Trojan was leaked back in 2011. Since that time, new versions of this dangerous malware variant have surfaced as hackers try to improve upon the source code for what was once the most feared malware strain being used across the globe. Unlike that leak, however, the leak of ZeusVM does not contain the actual source code for the Trojan. This means that hackers are not able to improve upon this leaked code to create more powerful variants of ZeusVM. That said, all a wannabe hacker needs is the leaked builder and control panel. Using these tools, a cybercriminal can create customized ZeusVM binary files in mere minutes. It does not cost anything to use these tools so there is very little risk for someone interested in the world of malware for profit. The builder allows the attacker to modify things such as the URL of the C&C server used by the Trojan to receive configuration instructions. The control panel is a Web-based application that operates the C&C server. The control panel is also used to send and receive data from any PCs that have been infected by ZeusVM.
Although it isn’t clear who leaked the ZeusVM source code or why it was done, what is known is that these free tools can be used by practically anyone to create a dangerous banking Trojan capable of stealing thousands, perhaps even millions, of dollars. Ultimately, this indicates that a massive surge in banking Trojan infections could be just around the corner (especially now that knowledge of the leaked source code has become public).
There is another threat also detected by MMD that may become a concern for PC users and security researchers in the near future. MMD recently discovered an underground forum selling a new version of KINS (version 3.0) for $5,000. No one has seen the source code for this new threat yet meaning that any new capabilities exhibited by the latest Zeus variant are yet unknown. Based on some of the antidetection techniques currently being used by other malware strains, however, it can be assumed that modern antivirus detection tools will not be able to detect version 3 (at least not for a while).
As has been the case with all Zeus variants before, ZeusVM infects PCs using a few different techniques. Drive-by downloads (where a legitimate site is compromised by hackers and used to exploit popular Web browser plugins like Flash and Java) are a popular choice with hackers. Spam email campaigns relying on malicious attachments are another common infection technique. Finally, ZeusVM can be embedded in other files such as pirated software or even Microsoft Word macro files. Protecting your PC from ZeusVM version 2 (and the soon to be released version 3) starts with ensuring that the Windows OS and all third party applications are updated with the latest security patches.
Since one of the most effective ways for hackers to introduce ZeusVM into a system is to exploit known vulnerabilities in Web browser plugins (specifically Flash, JavaScript, and Java).
If these plugins aren’t needed, disable or uninstall them immediately. If these plugins are required for PC use on a regular basis, ensure that all updates are installed and that automatic updating is enabled to protect your PC from possible zero-day exploits. It seems like Zeus is back and with the discovery of version 3 being sold on the underground market, 2015 could be the next big year for the Zeus botnet. Only time will tell how this threat plays out on the global front as the summer progresses.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion