CryptoDefense Virus
![]() Written by Tomas Meskauskas on (updated)
Written by Tomas Meskauskas on (updated)
What is CryptoDefense?
The CryptoDefense ransomware virus infiltrates operating systems via infected email messages and fake downloads including, for example, rogue video players or fake Flash updates. After successful infiltration, this malicious program encrypts files (*.doc, *.docx, *.xls, *.ppt, *.psd, *.pdf, *.eps, *.ai, *.cdr, *.jpg, etc.) stored on users' computers and demands payment of $500 ransom (in Bitcoins) to decrypt the files.
Cyber criminals responsible for releasing this rogue program ensure it executes on all Windows operating systems (Windows XP, Windows Vista, Windows 7, and Windows 8). CryptoDefense ransomware creates How_Decrypt.txt, How_Decrypt.html, and How_Decrypt.url files within each folder containing the encrypted files.
These files contain instructions regarding how users may decrypt their files, including the use of the Tor browser (an anonymous web browser). Cyber criminals use Tor to hide their identities.
PC users should be aware that while this infection is not complicated to remove, the decryption of files (encrypted using RSA 2048 encryption) affected by this malicious program, is not possible without paying the ransom.
At time of research, no tools or solutions capable of decrypting files encrypted by CryptoDefense existed. Note that the private key used to decrypt the files is stored within CryptoDefense command-and-control servers, which are managed by cyber criminals. An ideal solution is to remove this ransomware virus and restore your data from a backup.
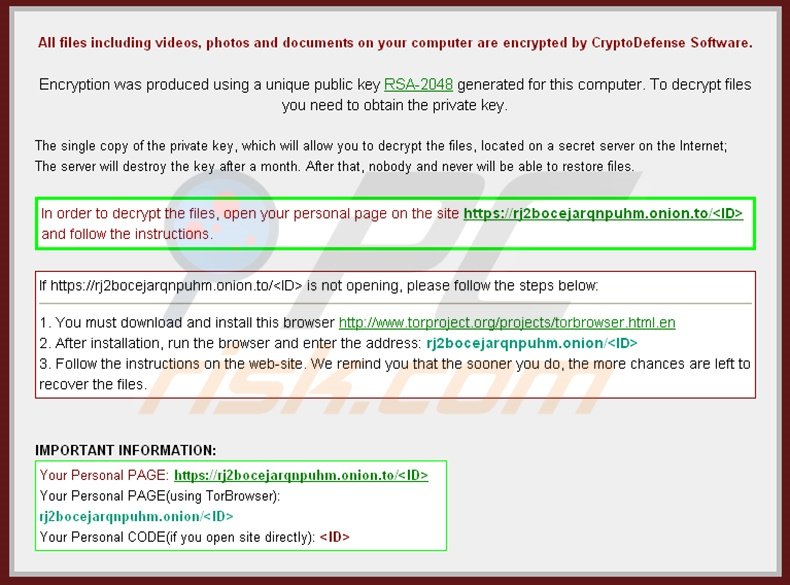
Screenshot of a message presented within the How_Decrypt.txt, How_Decrypt.html, and How_Decrypt.url files:
Ransomware infections such as CryptoDefense (including CryptorBit and Cryptolocker) make a strong argument to maintain regular backups of your stored data.
Note that paying the ransom as encouraged by this ransomware is equivalent to sending your money to cyber criminals - you will support their malicious business model, and furthermore, there is no guarantee that your files will be decrypted.
To avoid computer infection with ransomware infections such as these, express caution when opening email messages, since cyber criminals use various catchy titles to trick PC users into opening the infected attachments, for example, "Scanned Image from a Xerox WorkCentre".
Research shows that cyber criminals also use P2P networks and fake downloads containing bundled ransomware infections to proliferate CryptoDefense.
Message presented in How_Decrypt.txt, How_Decrypt.html and How_Decrypt.url files:
All files including videos, photos and documents on your computer are encrypted by CryptoDefense Software. Encryption was produced using a unique public key RSA-2048 generated for this computer. To decrypt files you need to obtain the private key. The single copy of the private key, which will allow you to decrypt the files, located on a secret server on the Internet; The server will destroy the key after a month. After that, nobody and never will be able to restore files. In order to decrypt the files, open your personal page on the site hxxps://rj2bocejarqnpuhm.browsetor.com/UOs and follow the instructions.
If hxxps://rj2bocejarqnpuhm.browsetor.com/UOs is not opening, please follow the steps below:
1. You must download and install this browser hxxp://www.torproject.org/projects/torbrowser.html.en
2. After installation, run the browser and enter the address: rj2bocejarqnpuhm.onion/UOs
3. Follow the instructions on the web-site. We remind you the the sooner you do, the more chances are left to recover the files.
Screenshot of an infected email message used in CryptoDefense distribution:
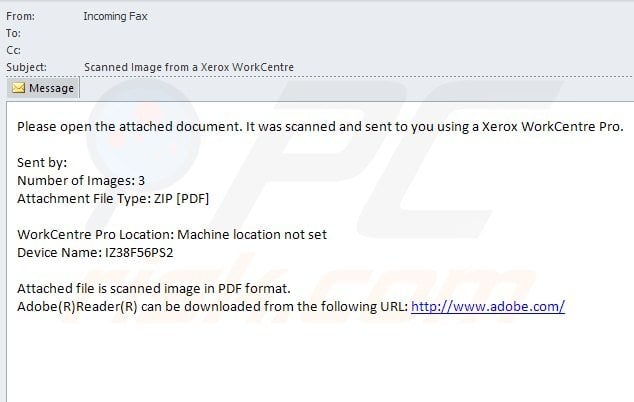
Text presented in the infected email messages:
From: Incoming Fax
Subject: Scanned Image from a Xerox WorkCentrePlease open the attached document. It was scanned and sent to you using Xerox WorkCentre Pro.
Number of Images:3
Attachment File Type: ZIP [PDF]WorkCentre Pro Location: Machine location not set
Device Name: IZ38F56PS2Attached files is scanned image in PDF format.
Screenshot of a ransom payment page:

Message presented in the ransom payment page:
Your files are encrypted. To get the key to decrypt files you have to pay 500 USD/EUR If payment is not made before [date - time] the cost of decrypting files will increase 2 times and will be 1000 USD/EUR. We are present a special software - CryptoDefense Decrypter - which is allow to decrypt and return control to all your encrypted files. How to buy CryptoDefense decrypter?
1. You should register Bitcoin waller
2. Purchasing Bitcoins - Although it's not yet easy to buy bit coins, it's getting simpler every day.
3. Send 1.09 BTC to Bitcoin address: 1EmLLj8peW292zR2VvumYPPa9wLcK4CPK1
4. Enter the Transaction ID and select amount.
5. Please check the payment information and click "PAY".
Note that at time of writing, there were no known tools available to decrypt files encrypted by CryptoDefense without paying the ransom.
By following this removal guide you will be able to remove this ransomware from your computer, however, the affected files will remain encrypted. We will update this article as soon as there is more information regarding the decryption of the compromised files.
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
▼ DOWNLOAD Combo Cleaner
By downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by Rcs Lt, the parent company of PCRisk.com read more.
Quick menu:
- What is CryptoDefense?
- STEP 1. "CryptoDefense" virus removal using safe mode with networking.
- STEP 2. "CryptoDefense" ransomware removal using System Restore.
CryptoDefense virus removal:
Step 1
Windows XP and Windows 7 users: Start your computer in Safe Mode. Click Start, click Shut Down, click Restart, click OK. During your computer starting process press the F8 key on your keyboard multiple times until you see the Windows Advanced Option menu, then select Safe Mode with Networking from the list.
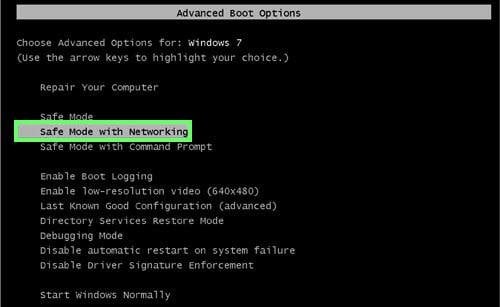
Video showing how to start Windows 7 in "Safe Mode with Networking":
Windows 8 users: Start Windows 8 is Safe Mode with Networking - Go to Windows 8 Start Screen, type Advanced, in the search results select Settings. Click on Advanced startup options, in the opened "General PC Settings" window select Advanced startup. Click on "Restart now" button.
Your computer will now restart into "Advanced Startup options menu". Click on the "Troubleshoot" button, then click on the "Advanced options" button. In the advanced option screen click on "Startup settings". Click on the "Restart" button. Your PC will restart into Startup Settings screen. Press F5 to boot in Safe Mode with Networking.
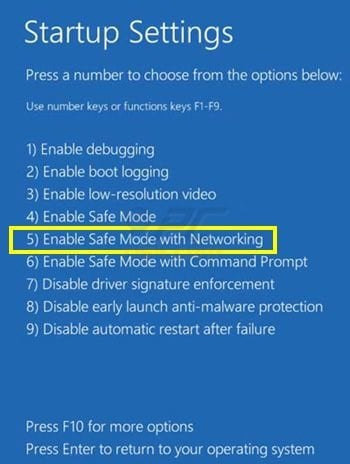
Video showing how to start Windows 8 in "Safe Mode with Networking":
Step 2
Log in to the account infected with CryptoDefense virus. Start your Internet browser and download a legitimate anti-spyware program. Update the anti-spyware software and start a full system scan. Remove all entries detected.
If you cannot start your computer in Safe Mode with Networking, try performing a System Restore.
Video showing how to remove ransomware virus using "Safe Mode with Command Prompt" and "System Restore":
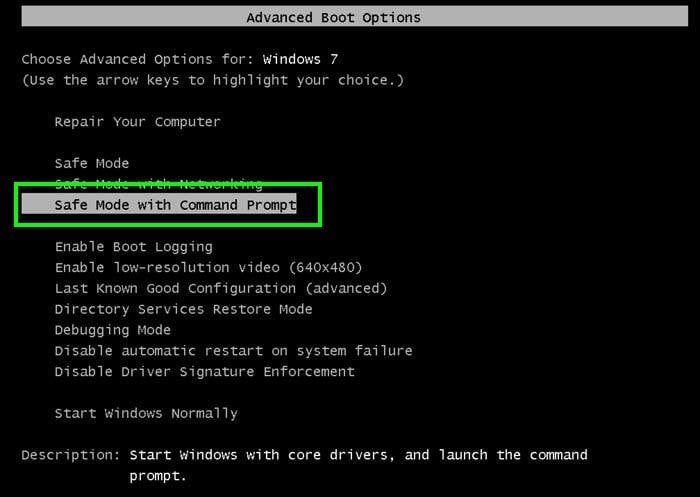
1. During your computer starting process, press the F8 key on your keyboard multiple times until the Windows Advanced Options menu appears, and then select Safe Mode with Command Prompt from the list and press ENTER.
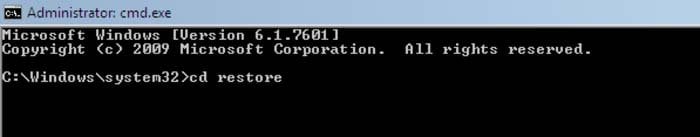
2. When Command Prompt mode loads, enter the following line: cd restore and press ENTER.
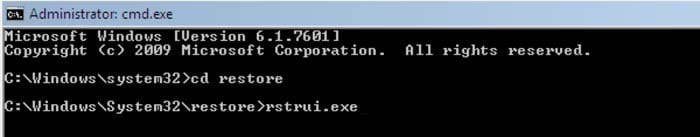
3. Next, type this line: rstrui.exe and press ENTER.
4. In the opened window, click "Next".
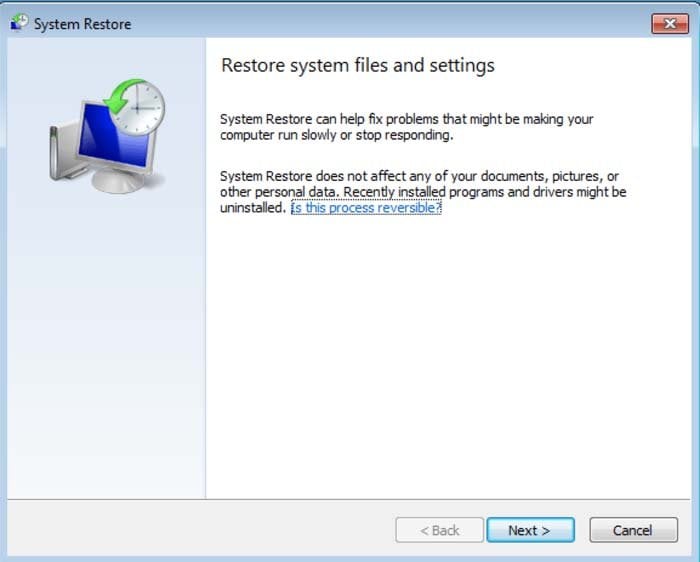
5. Select one of the available Restore Points and click "Next" (this will restore your computer system to an earlier time and date, prior to the CryptoDefense ransomware virus infiltrating your PC).
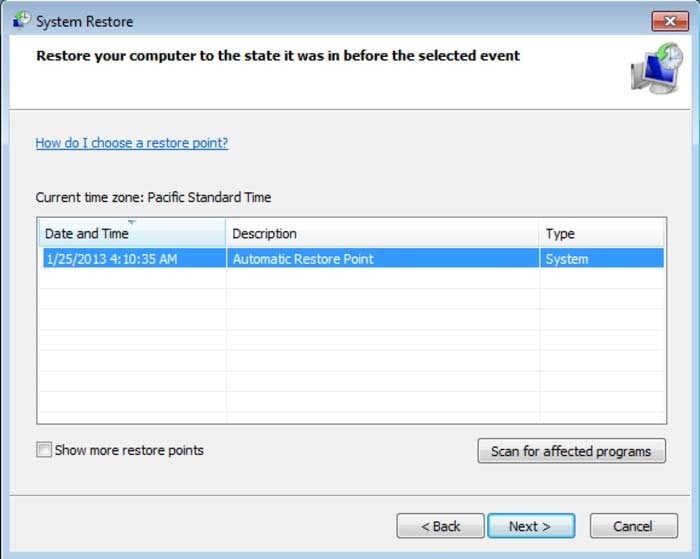
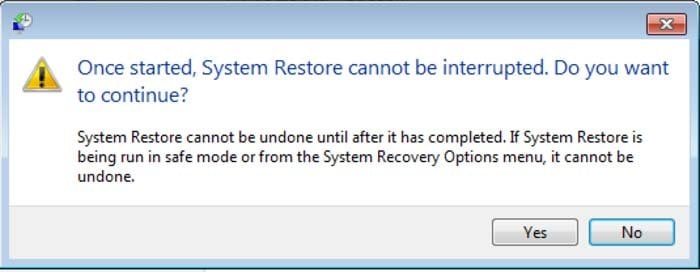
6. In the opened window click "Yes".
7. After restoring your computer to a previous date, download and scan your PC with recommended malware removal software to eliminate any remaining CryptoDefense files.
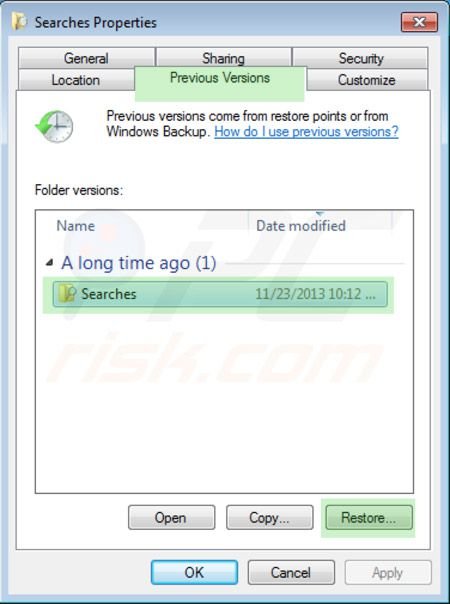
To restore individual files encrypted by this ransomware, PC users can try using Windows Previous Versions feature. This method is only effective if the System Restore function was enabled on the infected operating system. Note that some variants of CryptoDefense are known to remove Shadow Volume Copies of the files, so this method may not work on all computers.
To restore a file, right-click on it, go into Properties, and select the Previous Versions tab. If the selected file has a Restore Point, select it and click the "Restore" button.
If you cannot start your computer in Safe Mode with Networking (or with Command Prompt), boot your computer using a rescue disk. Some variants of ransomware disable Safe Mode making its removal complicated. For this step, you require access to another computer.
Other tools known to remove CryptoDefense ransomware:
▼ Show Discussion