Adylkuzz: The New Malware Threat
With much of the world still reeling from the WannaCry attack of last week, analysts and researchers have discovered a new threat. Researchers at Proofpoint discovered the threat on Monday this week that uses the same SMB exploit as WannaCry. The new threat, termed Adylkuzz, is not ransomware but rather a Cryptocurrency Mining Botnet. Adylkuzz makes use of the same alleged NSA hacking tools EternalBlue which took WannaCry from a purely amateur hour ransomware to the threat that made headlines infecting over 200,000 systems from over 150 Countries. Adyllkuzz further employed DoublePulsar another of the dumped hacking tools in its propagation.
The going wild of the abovementioned NSA hacking tools by the Russian hacking group “The Shadow Brokers” will undoubtedly have massive ramifications for the cyber security industry and the public as a whole. While WannaCry was a shot across the bow as to the seriousness of threats particularly when one saw how a simple ransomware bug when combined with NSA tools, could infect the British National Health Service, US package delivery giant FedEx, Spanish telecoms giant Telefonica, and Germany's Deutsche Bahn rail network. Adylkuzz, on the other hand, turns infected systems and by default their unwitting users into accomplices to financial crime on a grand scale. Little is known yet of the true scale of this attack but due to its more sophisticated nature than WannaCry, Adylkuzz may be significantly larger in scale.
Overview
Adyllkuzz used the above mentioned hacking tools, EternalBlue and DoublePulsar, to leverage the Windows vulnerability (MS17-010) in Microsoft Server Message Block (SMB) on TCP port 445 to spread the malicious payload in much the same way WannaCry did. Adyllkuzz, however, was much harder to detect. This is due in part to it not being ransomware, thus leaving no ransom note or encrypted files which would make detection obviously far easier. Another reason Adyllkuzz was much harder to detect results from the malware itself. Once deployed Adyllkuzz will stop potential instances it of already running and block SMB communication to prevent further infection. Initially, the malware was deployed will discover the relevant IP address and then download the mining instructions, cryptominer, and cleanup tools. At any one given time, it appears there are multiple Adylkuzz command and control servers hosting the cryptominer binaries and mining instructions.
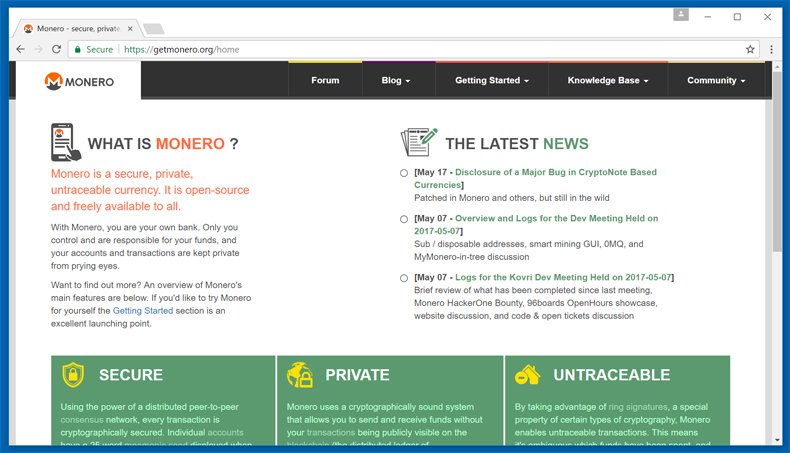
Currently, Adyllkuzz appears to be mining the cryptocurrency Monero, this may be due in part to the currencies inbuilt anonymity features. To this extent, Monero saw a surge in use when it appears to be adopted as the currency of the AlphaBay darknet. An advantage of using Monero is that it is less resource heavy than Bitcoin which now requires high-performance machines dedicated to mining. This makes Monero far more easily distributed across a botnet. With one Monero being the equivalent of approximately 27 USD, through the monitoring of certain accounts it has been estimated that the organization using Adylkuzz has made over 43,000 USD. Other estimates put this figure much higher.

In an interesting turn of events, it appears Adylkuzz may have prevented other unpatched systems been infected by WannCry. As the program SMB ports and it is estimated that Adylkruzz may have infected systems as early as April this year, this would have prevented WannaCry from installing on a system already infected with Adylkuzz. This may have been done in an attempt to prevent other malware and ransomware from using resources necessary for the cryptocurrency mining.
EternalBlue and DoublePulsar
This is now the second campaign to leverage EternalBlue and DoublePulsar, it is safe to assume that more campaigns will use these tools. As was mentioned above these tools were released into the Wild by the hacking group “The Shadow Brokers” in April as part of a massive dump. The same hacking group has threatened another dump to happen in June this year. One shudders to think what may be included in the future dump. While, these tools appear to be in the mainstream media headlines and making for interesting workplace discussions, what are they?
EternalBlue exploits the vulnerability mentioned above in older versions of Windows. Microsoft did release a patch for this vulnerability, however, for whatever reason, over 200,000 systems did not download it. Many of those systems were found in Industries which use ICS applications. Essentially, this zero-day exploits the version 1 (SMBv1) server in various older versions of Microsoft Windows and allows it to accept specially crafted packets from remote attackers, allowing them to execute arbitrary code on the target computer.
DoublePulsar is essentially a backdoor which allows infected machines to distribute malware, send spam, and launch attacks on other computers. It is installed with EternalBlue and in this instance, DoublePulsar is used to deploy the final payload for Adylkuzz. The use of these tools prompted Microsoft to patch Windows XP and Windows Server 2003, products it had stopped supporting in 2014. It is advised that administrators and the public at large make sure they are up to date on downloading and installing these patches to prevent further infection.
Due to these tools, which many believed were developed by the NSA as cyber-spying tools, been released into the wild, they have given opportunists the ability to cause havoc. We have seen this with WannaCry. Although Adyllkuzz does not appear as malicious, perhaps as it is not as blunt as ransomware in achieving its specific set objectives, it is not less serious. It makes the unwary accessories to the crime and provides a roadmap for other to follow who may develop far more malicious code. This is particularly frightening when considers another huge dump of sophisticated hacking tools may be on the way. Cyber-security as an industry is becoming an exciting and most definitely frightening industry to work in now and potentially more so in the near future.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion