New Version of TrickBot Discovered
With WannaCry and Petya attacks slowing down it was only a matter of time till the lessons learned from these attacks would be used by other cyber criminals. The creators of TrickBot have most certainly learnt how to increase the propagation exponentially of the malware using the lessons learnt from this year’s most devastating cyber-attacks.
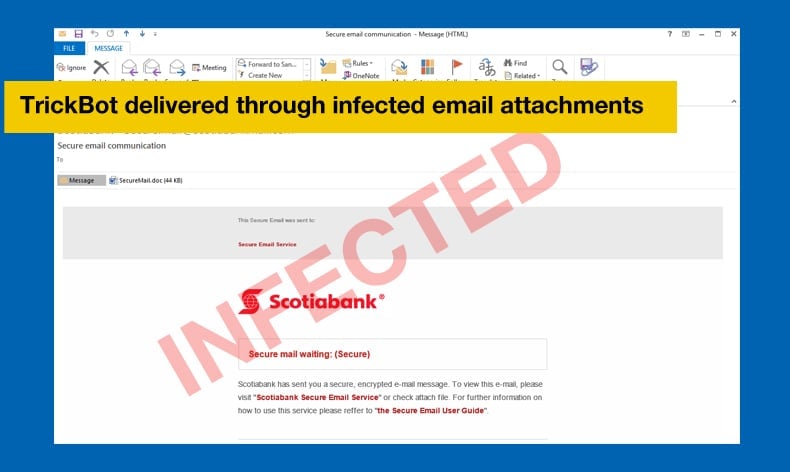
The new version (1000029 or v24) of the credential stealing malware has been found to be using the same SMB exploit famously used by WannaCry and Petya. TrickBot has been stealing credentials from banking institutions towards the end of last year. It has attacked financial institutions across the globe. The favoured attack vector for TrickBot is through email attachments impersonating invoices from a large financial institution.
TrickBot’s less than illustrious history
First detected targeting banks in Australia in September 2016, by November of that year institutions in the United Kingdom were being targeted. After the initial attack campaign researchers at BioCatch determined the malware had five distinct characteristics. Those were the following:
Trickbot combines RAT and redirection techniques to conduct sustained, multi-phased campaigns. The Trojan slowly manipulates victim accounts until ready to deploy a standard Remote Access protocol (VNC) completely invisible to device recognition and geo-location tools. After switching off all active components of the malware, they open a browser from within the genuine victim machine, log into online banking and proceed uninterrupted to empty the victim's account.
The similarities between this new piece of malware and the Dyre banking Trojan have researchers wondering if there’s a connection. For instance, both used a similar loader.
The Trickbot was written in C++, utilizes Microsoft CryptoAPI, and interfaces with Task Scheduler rather than running commands directly.
Trickbot combines user redirection and RAT and has a powerful server-side MITB web injection mechanism that allows it to dynamically inject scripts into the user browser. Trickbot can be detected with behavioural biometrics. The user’s and the Trickbot’s operator mouse behaviour can be differentiated. Perhaps due to the challenging hand-eye coordination of a remote access, the operator normally uses keys to select currencies and scroll up and down, preferring the keyboard to using the mouse. Since its discovery, newer versions of TrickBot continue to surface and attack institutions globally and with the latest version, its deployment does not look to slow in the near future.
The latest version
Researchers at both Flashpoint and MalwareBytes have been tracking and analysing the latest iteration since its discovery. In the latest version, TrickBot can be spread locally across networks via SMB. Unlike WannaCry and Petya it still cannot scan external IPs. Rather the Trojan scans domains for lists of vulnerable servers via the NetServerEnum Windows API and enumerates other computers on the network via Lightweight Directory Access Protocol (LDAP).
Another new feature is that it can be disguised as a setup.exe which is delivered through a PowerShell script to spread through interprocess communication and download additional versions of TrickBot onto shared drives.
In MalwareBytes’ research the following samples were analysed:
- 9aac1e00d62e0b4049781cc5eff99bc7 – main sample (packed)
- 9b3659936354dceb1063a42f15d0f12a – main sample (unpacked)
- 60bd4480035e82393636b0fb60d351ba – bot 32 bit
- ba36cf1afb6b6eed38b0a8d54152335b – bot64 bit
- 74933912ad87ec0b3a1b570a0ea0832b – loader for 64 bit
Downloaded modules (32 bit):
- b6f9ba3fd8af478147c59b2f3b3043c7 – OutlookX32.dll
- ac32c723c94e2c311db78fb798f2dd63 – module.dll (importDll32)
- f8e58af3ffefd4037fef246e93a55dc8 – mailsearcher.dll (mailsearcher32)
- 25570c3d943c0d83d69b12bc8df29b9d – SystemInfo.dll (systeminfo32)
- 5ac93850e24e7f0be3831f1a7c463e9c – loader.dll (injectDll32)
- 69086a1e935446067ecb1d20bfa99266 – core-dll.dll
- b34d36c1c76b08e7b8f28d74fbf808d8 – rtbroker_dll.dll
Based on the analysis of the above-mentioned samples it was determined that the Trojan looks to steal data from:
- Cookies
- HTML5 Local Storage
- Browsing History
- Flash LSO (Local Shared Objects)
- URL hits
The authors of this latest iteration did very little to hide their intentions or even subvert analysts in unpacking the new version. MalwareBytes concluded the following:
TrickBot’s new modules are not written very well and they are probably still under development. The overall quality of the design is much lower than the quality of the earlier code. For example, module.dll is bulky and does not follow the clean modular structure introduced by TrickBot before. Also, they make use of languages and libraries that are easier - Qt instead of native sockets for module.dll, Delphi language for Outlook.dll. Those changes may indicate some changes in the development team - either they gained new members that have been delegated to the new tasks or some of the previous members resigned and has been substituted by lower quality programmers. It may also be possible, that they are doing some prototyping and experiments for the further development. Anyways, as we can see, TrickBot is still actively maintained and it is not going to leave the landscape any soon.
According to Flashpoint, although the latest version of TrickBot is crude it illustrates a possible direction that future versions of the Trojan will take. As with other malware users and administrators are advised to ensure anti-virus software is kept up to date, along with ensuring the latest patches for your operating systems are downloaded and installed and be sure not to open attachments that seem suspicious.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion