Do not trust emails claiming you will be sent an ATM card with millions on it
Phishing/ScamAlso Known As: "ATM Card" spam email
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What kind of email is "ATM Card"?
Our inspection of the "ATM Card" email uncovered that it is spam. The letter claims that the recipient will be sent an ATM card with over three million US dollars on it, and they are asked to provide their personal information for delivery purposes. However, it is possible that this phishing scam will also request bogus payments.
"ATM Card" email scam overview
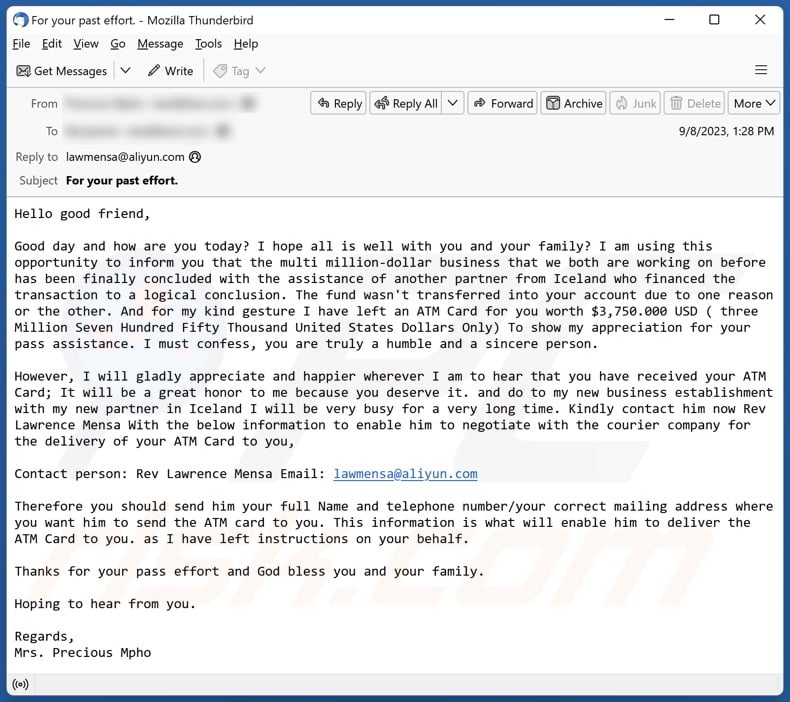
The spam email with the subject "For your past effort." (may vary) is meandering and vague. The supposed sender identifies the recipient as a "good friend", and informs that their joint efforts in the "multi million-dollar business" venture have been concluded with the assistance of a partner from Iceland.
For the recipient's previous support, they will be sent an ATM card with 3,750,000 USD on it since a bank transfer did not go through. The sender requests the recipient to contact the Icelander partner to facilitate the ATM card delivery. The letter targets the following information – full name, mailing address, and telephone number.
It must be stressed that all these claims are false; this mail is a scam. It is not unlikely that once entangled in the scheme, the victim will be requested to provide more private data (e.g., additional personally identifiable details, finance-related account log-in credentials, credit card numbers, etc.).
Furthermore, the victim may be asked to pay fake fees for the delivery of the nonexistent ATM card, i.e., directly transfer money to the scammers.
To summarize, by trusting an email like "ATM Card" – users can experience severe privacy issues, financial losses, and even identity theft.
If you have provided your log-in credentials to scammers – immediately change the passwords of all possibly exposed accounts and inform their official support. And if you've disclosed other private information (e.g., ID card details, passport scans/photos, credit card numbers, etc.) – contact the appropriate authorities without delay.
| Name | "ATM Card" spam email |
| Threat Type | Phishing, Scam, Social Engineering, Fraud |
| Fake Claim | Recipient will be sent an ATM card with $3,750,000 on it. |
| Symptoms | Unauthorized online purchases, changed online account passwords, identity theft, illegal access of the computer. |
| Distribution methods | Deceptive emails, rogue online pop-up ads, search engine poisoning techniques, misspelled domains. |
| Damage | Loss of sensitive private information, monetary loss, identity theft. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Spam campaigns in general
We have examined thousands of spam emails; "Overdue Invoice", "How I Earned Bitcoins", and "Central Bank Of Nigeria" are merely a couple examples of our latest finds.
Spam mail is used to promote various scams and even to proliferate malware. These emails can be full of errors or be competently disguised as messages from genuine companies, institutions, organizations, service providers, authorities, and other entities.
Due to how prevalent spam mail is and how well-crafted it can be – we highly recommend being careful with incoming emails, DMs/PMs, SMSes, and other messages.
How do spam campaigns infect computers?
Spam emails/messages can include malicious files as attachments or download links. These files can be archives (ZIP, RAR, etc.), executables (.exe, .run, etc.), documents (PDF, Microsoft Office, Microsoft OneNote, etc.), JavaScript, and so forth.
The malware download/installation chain is initiated once such a file is opened. However, these formats may need additional interaction to jumpstart system infection processes. For example, Microsoft Office documents require users to enable macro commands (i.e., editing/content), while OneNote files need them to click embedded files or links.
How to avoid installation of malware?
We strongly recommend exercising caution with incoming emails, PMs/DMs, SMSes, and other messages. Attachments or links found in dubious/irrelevant mail must not be opened, as they can be virulent.
It is important to use Microsoft Office versions released after 2010 since they have the "Protected View" mode that prevents automatic macro execution.
However, malware is not proliferated exclusively via spam mail. Therefore, we also advise being vigilant when browsing since fake and malicious online content usually appears legitimate and harmless.
Furthermore, all downloads must be performed from official and verified sources. Another recommendation is to activate and update programs by using genuine functions/tools, as illegal activation ("cracking") tools and third-party updaters can contain malware.
We must emphasize that having a dependable anti-virus installed and kept up-to-date is essential to device and user safety. Security software must be used to run regular system scans and to remove threats and issues. If you've already opened malicious attachments, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
Text presented in the "ATM Card" spam email letter:
Subject: For your past effort.
Hello good friend,
Good day and how are you today? I hope all is well with you and your family? I am using this opportunity to inform you that the multi million-dollar business that we both are working on before has been finally concluded with the assistance of another partner from Iceland who financed the transaction to a logical conclusion. The fund wasn't transferred into your account due to one reason or the other. And for my kind gesture I have left an ATM Card for you worth $3,750.000 USD ( three Million Seven Hundred Fifty Thousand United States Dollars Only) To show my appreciation for your pass assistance. I must confess, you are truly a humble and a sincere person.
However, I will gladly appreciate and happier wherever I am to hear that you have received your ATM Card; It will be a great honor to me because you deserve it. and do to my new business establishment with my new partner in Iceland I will be very busy for a very long time. Kindly contact him now Rev Lawrence Mensa With the below information to enable him to negotiate with the courier company for the delivery of your ATM Card to you,
Contact person: Rev Lawrence Mensa Email: lawmensa@aliyun.com
Therefore you should send him your full Name and telephone number/your correct mailing address where you want him to send the ATM card to you. This information is what will enable him to deliver the ATM Card to you. as I have left instructions on your behalf.
Thanks for your pass effort and God bless you and your family.
Hoping to hear from you.
Regards,
Mrs. Precious Mpho
Other examples of emails from "ATM Card" spam campaign:
Sample 1:
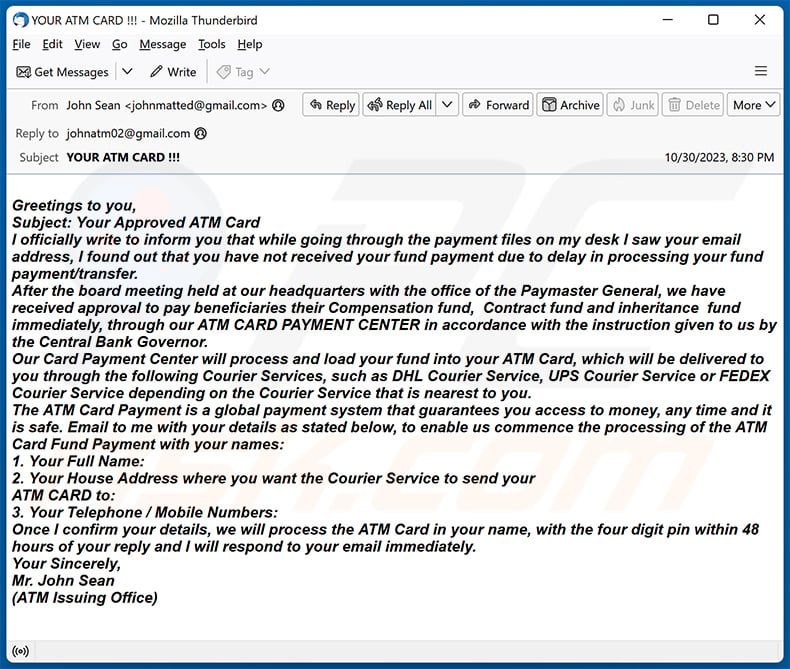
Text presented within:
Subject: YOUR ATM CARD !!!
Greetings to you,
Subject: Your Approved ATM Card
I officially write to inform you that while going through the payment files on my desk I saw your email address, I found out that you have not received your fund payment due to delay in processing your fund payment/transfer.
After the board meeting held at our headquarters with the office of the Paymaster General, we have received approval to pay beneficiaries their Compensation fund, Contract fund and inheritance fund immediately, through our ATM CARD PAYMENT CENTER in accordance with the instruction given to us by the Central Bank Governor.
Our Card Payment Center will process and load your fund into your ATM Card, which will be delivered to you through the following Courier Services, such as DHL Courier Service, UPS Courier Service or FEDEX Courier Service depending on the Courier Service that is nearest to you.
The ATM Card Payment is a global payment system that guarantees you access to money, any time and it is safe. Email to me with your details as stated below, to enable us commence the processing of the ATM Card Fund Payment with your names:
1. Your Full Name:
2. Your House Address where you want the Courier Service to send your
ATM CARD to:
3. Your Telephone / Mobile Numbers:
Once I confirm your details, we will process the ATM Card in your name, with the four digit pin within 48 hours of your reply and I will respond to your email immediately.
Your Sincerely,
Mr. John Sean
(ATM Issuing Office)
Sample 2:
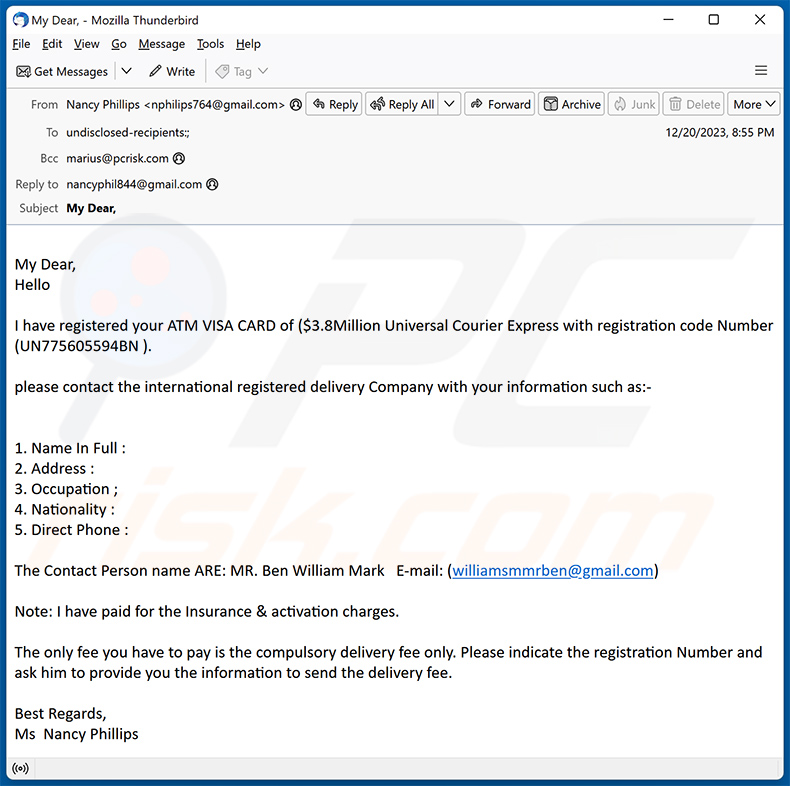
Text presented within:
Subject: My Dear,
My Dear,
HelloI have registered your ATM VISA CARD of ($3.8Million Universal Courier Express with registration code Number (UN775605594BN ).
please contact the international registered delivery Company with your information such as:-
1. Name In Full :
2. Address :
3. Occupation ;
4. Nationality :
5. Direct Phone :The Contact Person name ARE: MR. Ben William Mark E-mail: (williamsmmrben@gmail.com)
Note: I have paid for the Insurance & activation charges.
The only fee you have to pay is the compulsory delivery fee only. Please indicate the registration Number and ask him to provide you the information to send the delivery fee.
Best Regards,
Ms Nancy Phillips
Sample 3:
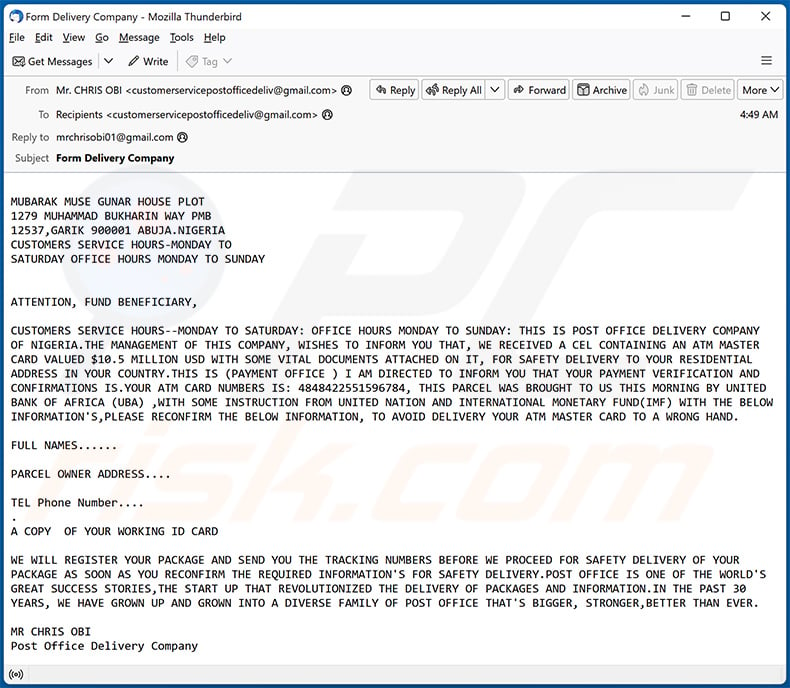
Text presented within:
Subject: Form Delivery Company
MUBARAK MUSE GUNAR HOUSE PLOT
1279 MUHAMMAD BUKHARIN WAY PMB
12537,GARIK 900001 ABUJA.NIGERIA
CUSTOMERS SERVICE HOURS-MONDAY TO
SATURDAY OFFICE HOURS MONDAY TO SUNDAY
ATTENTION, FUND BENEFICIARY,CUSTOMERS SERVICE HOURS--MONDAY TO SATURDAY: OFFICE HOURS MONDAY TO SUNDAY: THIS IS POST OFFICE DELIVERY COMPANY OF NIGERIA.THE MANAGEMENT OF THIS COMPANY, WISHES TO INFORM YOU THAT, WE RECEIVED A CEL CONTAINING AN ATM MASTER CARD VALUED $10.5 MILLION USD WITH SOME VITAL DOCUMENTS ATTACHED ON IT, FOR SAFETY DELIVERY TO YOUR RESIDENTIAL ADDRESS IN YOUR COUNTRY.THIS IS (PAYMENT OFFICE ) I AM DIRECTED TO INFORM YOU THAT YOUR PAYMENT VERIFICATION AND CONFIRMATIONS IS.YOUR ATM CARD NUMBERS IS: 4848422551596784, THIS PARCEL WAS BROUGHT TO US THIS MORNING BY UNITED BANK OF AFRICA (UBA) ,WITH SOME INSTRUCTION FROM UNITED NATION AND INTERNATIONAL MONETARY FUND(IMF) WITH THE BELOW INFORMATION'S,PLEASE RECONFIRM THE BELOW INFORMATION, TO AVOID DELIVERY YOUR ATM MASTER CARD TO A WRONG HAND.
FULL NAMES......
PARCEL OWNER ADDRESS....
TEL Phone Number....
.
A COPY OF YOUR WORKING ID CARDWE WILL REGISTER YOUR PACKAGE AND SEND YOU THE TRACKING NUMBERS BEFORE WE PROCEED FOR SAFETY DELIVERY OF YOUR PACKAGE AS SOON AS YOU RECONFIRM THE REQUIRED INFORMATION'S FOR SAFETY DELIVERY.POST OFFICE IS ONE OF THE WORLD'S GREAT SUCCESS STORIES,THE START UP THAT REVOLUTIONIZED THE DELIVERY OF PACKAGES AND INFORMATION.IN THE PAST 30 YEARS, WE HAVE GROWN UP AND GROWN INTO A DIVERSE FAMILY OF POST OFFICE THAT'S BIGGER, STRONGER,BETTER THAN EVER.
MR CHRIS OBI
Post Office Delivery Company
Sample 4:
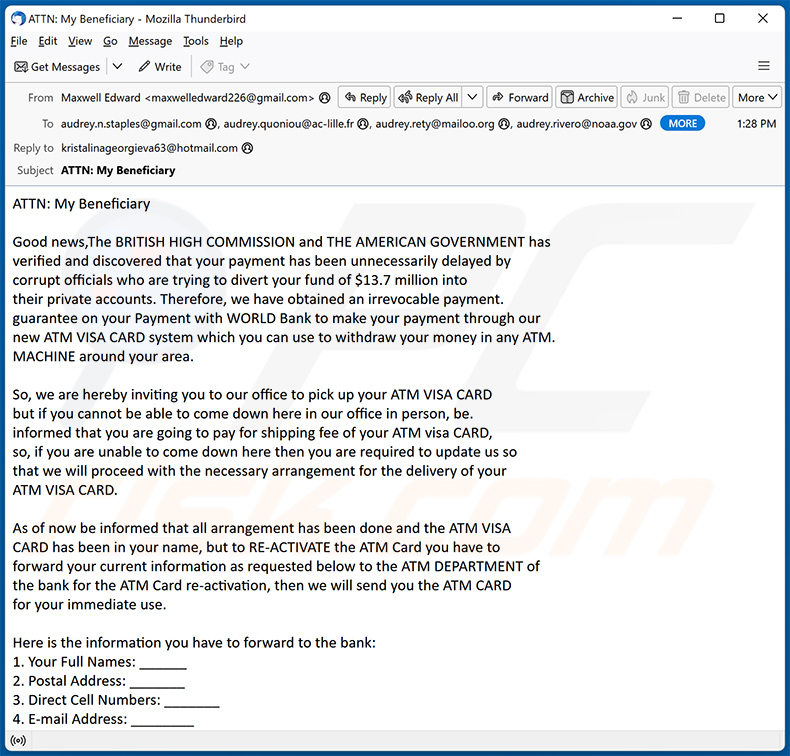
Text presented within:
ATTN: My Beneficiary
Good news,The BRITISH HIGH COMMISSION and THE AMERICAN GOVERNMENT has verified and discovered that your payment has been unnecessarily delayed by corrupt officials who are trying to divert your fund of $13.7 million into their private accounts. Therefore, we have obtained an irrevocable payment. guarantee on your Payment with WORLD Bank to make your payment through our new ATM VISA CARD system which you can use to withdraw your money in any ATM.
MACHINE around your area.So, we are hereby inviting you to our office to pick up your ATM VISA CARD but if you cannot be able to come down here in our office in person, be. informed that you are going to pay for shipping fee of your ATM visa CARD, so, if you are unable to come down here then you are required to update us so that we will proceed with the necessary arrangement for the delivery of your
ATM VISA CARD.As of now be informed that all arrangement has been done and the ATM VISA CARD has been in your name, but to RE-ACTIVATE the ATM Card you have to forward your current information as requested below to the ATM DEPARTMENT of the bank for the ATM Card re-activation, then we will send you the ATM CARD for your immediate use.
Here is the information you have to forward to the bank:
1. Your Full Names: ______
2. Postal Address: _______
3. Direct Cell Numbers: _______
4. E-mail Address: ________
5. Sex: _____
6. Age: _____
7. Occupation: ________
8.Nationality: ________CONTACT PERSON:
International Monetary Fund Director
E-mail:(kristalinageorgieva63@hotmail.com)
Sample 5:
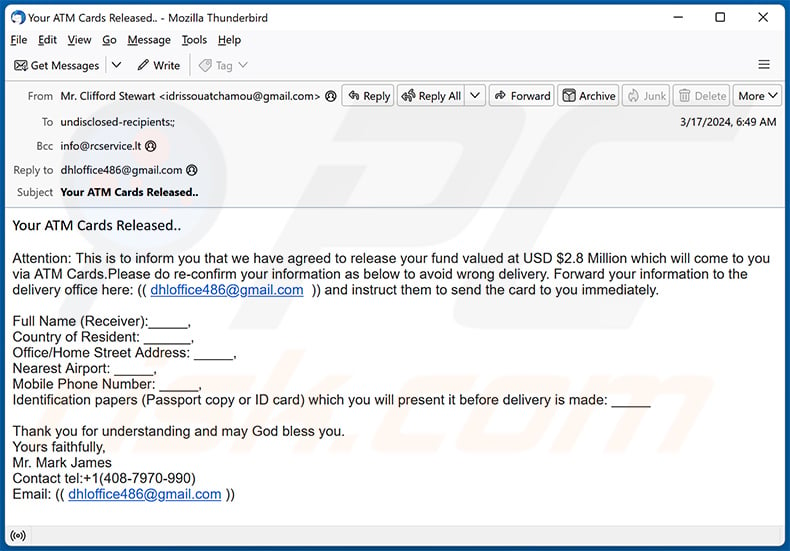
Text presented within:
Your ATM Cards Released..
Attention: This is to inform you that we have agreed to release your fund valued at USD $2.8 Million which will come to you via ATM Cards.Please do re-confirm your information as below to avoid wrong delivery. Forward your information to the delivery office here: (( dhloffice486@gmail.com )) and instruct them to send the card to you immediately.
Full Name (Receiver):_____,
Country of Resident: ______,
Office/Home Street Address: _____,
Nearest Airport: _____,
Mobile Phone Number: _____,
Identification papers (Passport copy or ID card) which you will present it before delivery is made: _____Thank you for understanding and may God bless you.
Yours faithfully,
Mr. Mark James
Contact tel:+1(408-7970-990)
Email: (( dhloffice486@gmail.com ))
Sample 6:
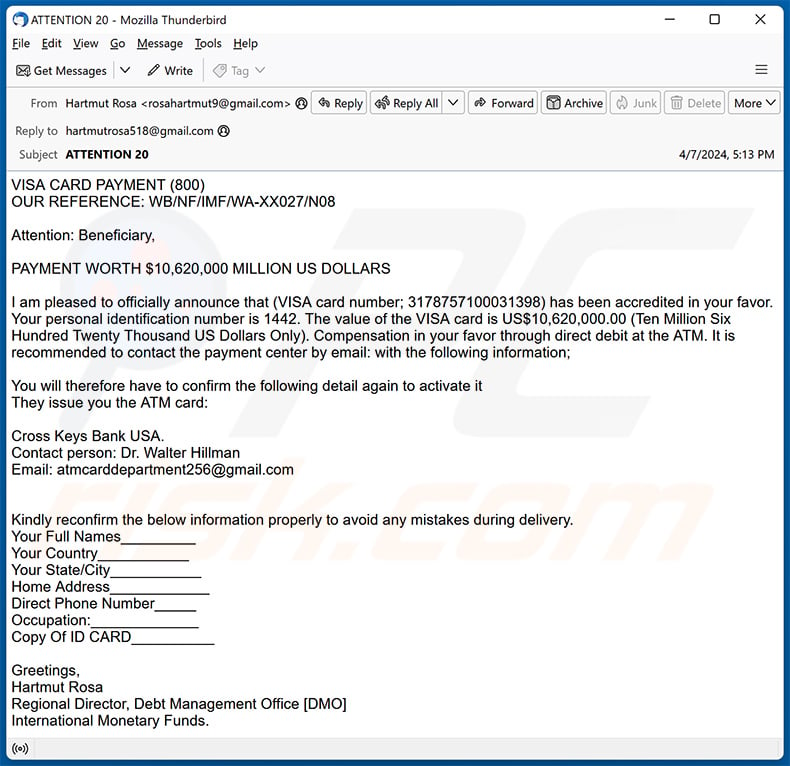
Text presented within:
Subject: ATTENTION 20
VISA CARD PAYMENT (800)
OUR REFERENCE: WB/NF/IMF/WA-XX027/N08
Attention: Beneficiary,
PAYMENT WORTH $10,620,000 MILLION US DOLLARS
I am pleased to officially announce that (VISA card number; 3178757100031398) has been accredited in your favor. Your personal identification number is 1442. The value of the VISA card is US$10,620,000.00 (Ten Million Six Hundred Twenty Thousand US Dollars Only). Compensation in your favor through direct debit at the ATM. It is recommended to contact the payment center by email: with the following information;
You will therefore have to confirm the following detail again to activate it
They issue you the ATM card:
Cross Keys Bank USA.
Contact person: Dr. Walter Hillman
Email: atmcarddepartment256@gmail.com
Kindly reconfirm the below information properly to avoid any mistakes during delivery.
Your Full Names_________
Your Country___________
Your State/City___________
Home Address____________
Direct Phone Number_____
Occupation:_____________
Copy Of ID CARD__________
Greetings,
Hartmut Rosa
Regional Director, Debt Management Office [DMO]
International Monetary Funds.
Sample 7:
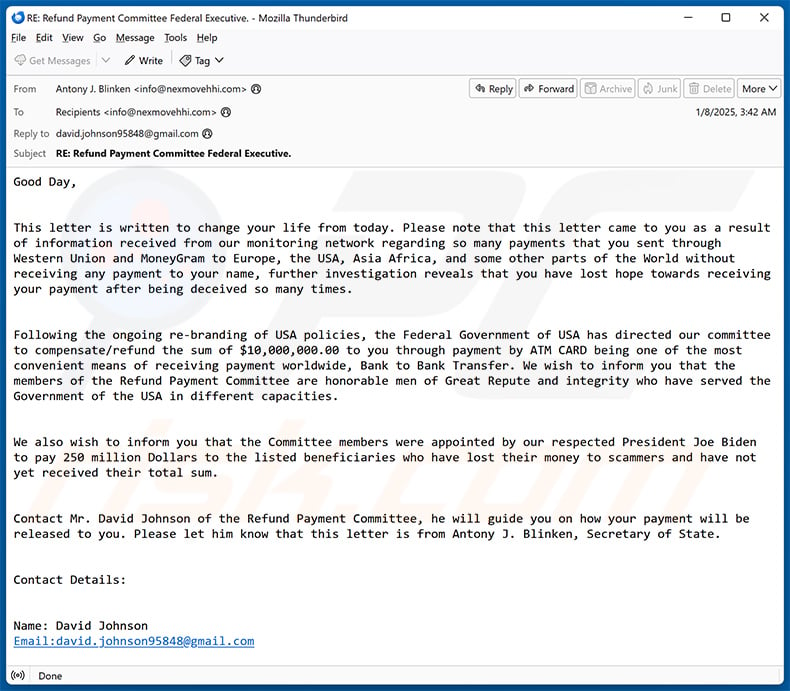
Text presented within:
Subject: RE: Refund Payment Committee Federal Executive.
From Desk Of Antony J. Blinken
USA Secretary of State
Refund Payment Committee
Federal Executive Council Washington DC USA.Good Day,
This letter is written to change your life from today. Please note that this letter came to you as a result of information received from our monitoring network regarding so many payments that you sent through Western Union and MoneyGram to Europe, the USA, Asia Africa, and some other parts of the World without receiving any payment to your name, further investigation reveals that you have lost hope towards receiving your payment after being deceived so many times.
Following the ongoing re-branding of USA policies, the Federal Government of USA has directed our committee to compensate/refund the sum of $10,000,000.00 to you through payment by ATM CARD being one of the most convenient means of receiving payment worldwide, Bank to Bank Transfer. We wish to inform you that the members of the Refund Payment Committee are honorable men of Great Repute and integrity who have served the Government of the USA in different capacities.
We also wish to inform you that the Committee members were appointed by our respected President Joe Biden to pay 250 million Dollars to the listed beneficiaries who have lost their money to scammers and have not yet received their total sum.
Contact Mr. David Johnson of the Refund Payment Committee, he will guide you on how your payment will be released to you. Please let him know that this letter is from Antony J. Blinken, Secretary of State.
Contact Details:
Name: David Johnson
Email:david.johnson95848@gmail.comTo receive your payment this week, you are advised to contact David Johnson on his email and make sure you ANSWER the Questions below.
(1) Your Full Name:
(2) Your Direct telephone. Fax Number ( if any):
(3) How Many Months Or Years in which You Have Been Expecting your Payment:
(4) The Place you sent Money Last whether Nigeria or London, Malaysia, Benin Republic, etc:
(5) The Last Amount of Money You sent indicating What Month and Year:4From Antony J. Blinken
USA Secretary of State
Refund Payment Committee
Federal Executive Council Washington DC US
Sample 8:
Text presented within:
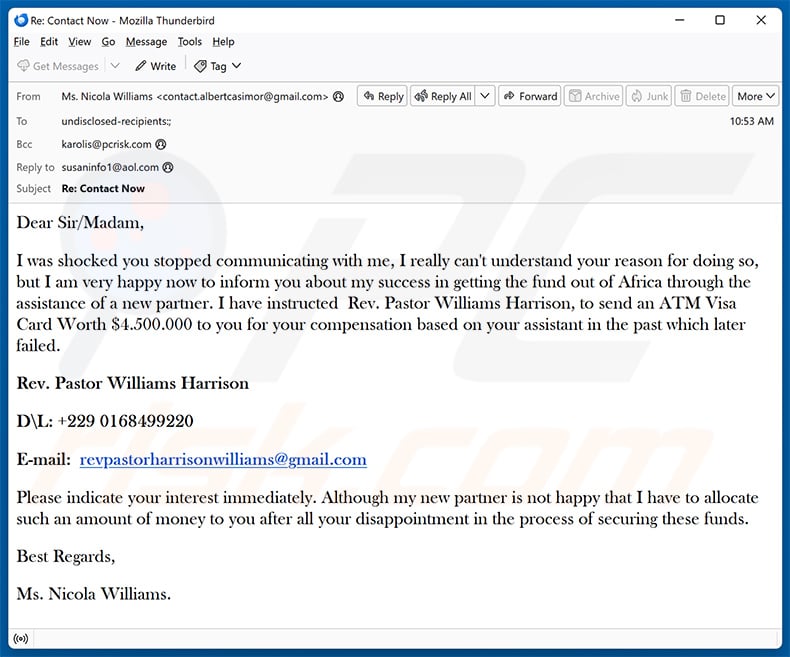
Subject: Re: Contact Now
Dear Sir/Madam,
I was shocked you stopped communicating with me, I really can't understand your reason for doing so, but I am very happy now to inform you about my success in getting the fund out of Africa through the assistance of a new partner. I have instructed Rev. Pastor Williams Harrison, to send an ATM Visa Card Worth $4.500.000 to you for your compensation based on your assistant in the past which later failed.
Rev. Pastor Williams Harrison
D\L: +229 0168499220
E-mail: revpastorharrisonwilliams@gmail.com
Please indicate your interest immediately. Although my new partner is not happy that I have to allocate such an amount of money to you after all your disappointment in the process of securing these funds.
Best Regards,
Ms. Nicola Williams.
Sample 9:
Text presented within:
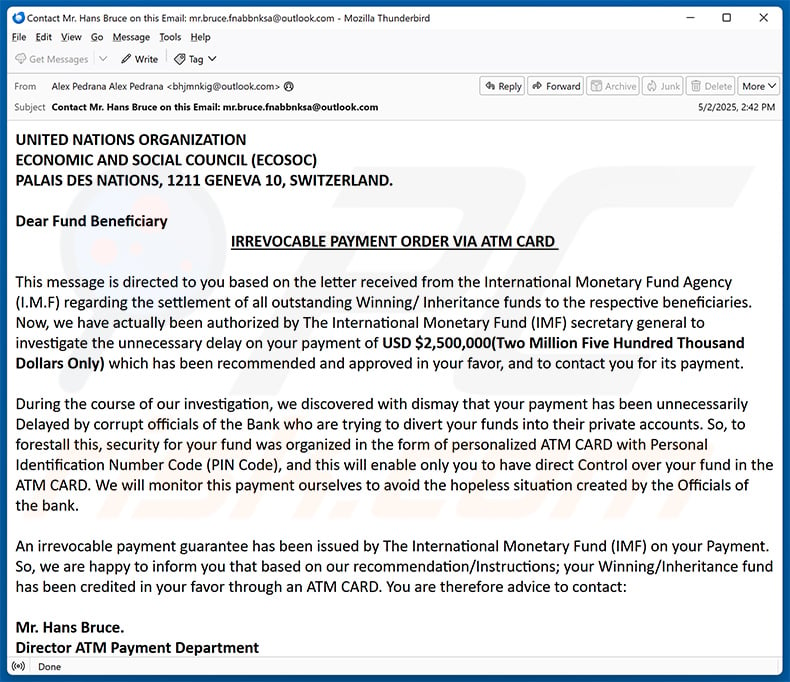
Subject: Contact Mr. Hans Bruce on this Email: mr.bruce.fnabbnksa@outlook.com
UNITED NATIONS ORGANIZATION
ECONOMIC AND SOCIAL COUNCIL (ECOSOC)
PALAIS DES NATIONS, 1211 GENEVA 10, SWITZERLAND.Dear Fund Beneficiary
IRREVOCABLE PAYMENT ORDER VIA ATM CARDThis message is directed to you based on the letter received from the International Monetary Fund Agency (I.M.F) regarding the settlement of all outstanding Winning/ Inheritance funds to the respective beneficiaries. Now, we have actually been authorized by The International Monetary Fund (IMF) secretary general to investigate the unnecessary delay on your payment of USD $2,500,000(Two Million Five Hundred Thousand Dollars Only) which has been recommended and approved in your favor, and to contact you for its payment.
During the course of our investigation, we discovered with dismay that your payment has been unnecessarily Delayed by corrupt officials of the Bank who are trying to divert your funds into their private accounts. So, to forestall this, security for your fund was organized in the form of personalized ATM CARD with Personal Identification Number Code (PIN Code), and this will enable only you to have direct Control over your fund in the ATM CARD. We will monitor this payment ourselves to avoid the hopeless situation created by the Officials of the bank.
An irrevocable payment guarantee has been issued by The International Monetary Fund (IMF) on your Payment. So, we are happy to inform you that based on our recommendation/Instructions; your Winning/Inheritance fund has been credited in your favor through an ATM CARD. You are therefore advice to contact:
Mr. Hans Bruce.
Director ATM Payment Department
(Co-operative Bank United Kingdom)
Contact Email: mr.bruce.fnabbnksa@outlook.com
Telephone line: +44 720 905 84134
Fax Number: +44-80487982102Contact him now for the delivery of your ATM Card. As soon as you establish a contact with him, an ATM card will be issued to you immediately which you can use to withdraw your funds in any Bank ATM Machine in your Country. So if you like to receive your funds through this means, you are advised to contact (Mr. Hans Bruce) with the following information as stated below:
1. Your Full Name:
2. Your Receiving Address:
3. Postal Code of your Address and the country:
4. Your Age:
5. Occupation:
6. Cell/Mobile Number:
7. Alternative Email:NOTE: You are advised to furnish Mr. Hans Bruce with your correct and valid details. Also be informed that the amount to be paid to you now is USD $2,500,000(Two Million Five Hundred Thousand Dollars Only) We expect your urgent response to this email to enable us monitor this payment effectively thereby making contact with Mr. Hans Bruce as directed to avoid further delay.
Yours in Services.
His Excellency, Ambassador Martin Sajdik
President.- Economic and Social Council (ECOSOC)
United Nations Organization
Sample 10:
Text presented within:
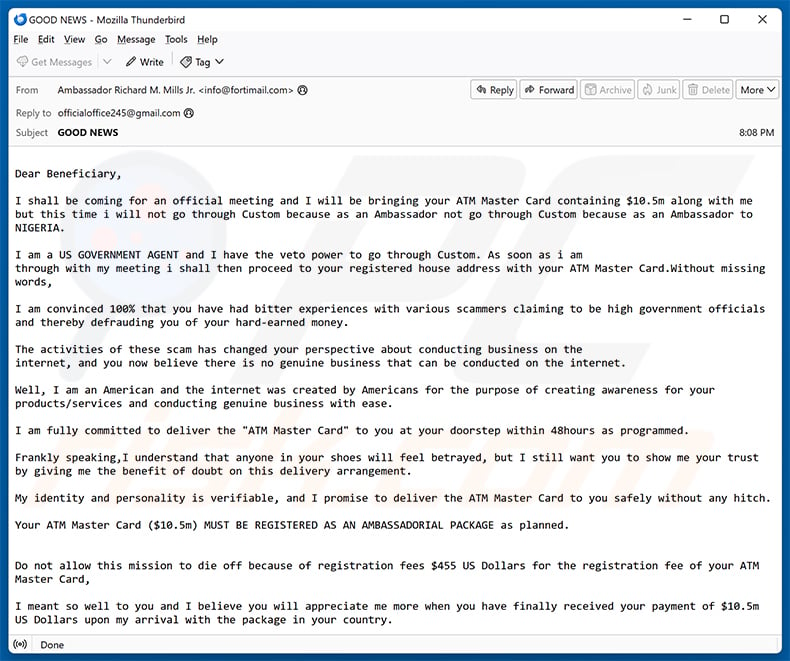
Subject: GOOD NEWS
Dear Beneficiary,
I shall be coming for an official meeting and I will be bringing your ATM Master Card containing $10.5m along with me but this time i will not go through Custom because as an Ambassador not go through Custom because as an Ambassador to NIGERIA.
I am a US GOVERNMENT AGENT and I have the veto power to go through Custom. As soon as i am
through with my meeting i shall then proceed to your registered house address with your ATM Master Card.Without missing words,I am convinced 100% that you have had bitter experiences with various scammers claiming to be high government officials and thereby defrauding you of your hard-earned money.
The activities of these scam has changed your perspective about conducting business on the
internet, and you now believe there is no genuine business that can be conducted on the internet.Well, I am an American and the internet was created by Americans for the purpose of creating awareness for your products/services and conducting genuine business with ease.
I am fully committed to deliver the "ATM Master Card" to you at your doorstep within 48hours as programmed.
Frankly speaking,I understand that anyone in your shoes will feel betrayed, but I still want you to show me your trust by giving me the benefit of doubt on this delivery arrangement.
My identity and personality is verifiable, and I promise to deliver the ATM Master Card to you safely without any hitch.
Your ATM Master Card ($10.5m) MUST BE REGISTERED AS AN AMBASSADORIAL PACKAGE as planned.
Do not allow this mission to die off because of registration fees $455 US Dollars for the registration fee of your ATM Master Card,
I meant so well to you and I believe you will appreciate me more when you have finally received your payment of $10.5m US Dollars upon my arrival with the package in your country.
I expect you to comply before then so that the delivery will be
completed. If you do not comply, then it will not be my fault if you
do not receive your Package.Signed
Ambassador Richard M. Mills Jr.
US AMBASSADOR TO FEDERAL REPUBLIC OF NIGERIA
officialoffice245@gmail.com
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is "ATM Card" spam email?
- Types of malicious emails.
- How to spot a malicious email?
- What to do if you fell for an email scam?
Types of malicious emails:
![]() Phishing Emails
Phishing Emails
Most commonly, cybercriminals use deceptive emails to trick Internet users into giving away their sensitive private information, for example, login information for various online services, email accounts, or online banking information.
Such attacks are called phishing. In a phishing attack, cybercriminals usually send an email message with some popular service logo (for example, Microsoft, DHL, Amazon, Netflix), create urgency (wrong shipping address, expired password, etc.), and place a link which they hope their potential victims will click on.
After clicking the link presented in such email message, victims are redirected to a fake website that looks identical or extremely similar to the original one. Victims are then asked to enter their password, credit card details, or some other information that gets stolen by cybercriminals.
![]() Emails with Malicious Attachments
Emails with Malicious Attachments
Another popular attack vector is email spam with malicious attachments that infect users' computers with malware. Malicious attachments usually carry trojans that are capable of stealing passwords, banking information, and other sensitive information.
In such attacks, cybercriminals' main goal is to trick their potential victims into opening an infected email attachment. To achieve this goal, email messages usually talk about recently received invoices, faxes, or voice messages.
If a potential victim falls for the lure and opens the attachment, their computers get infected, and cybercriminals can collect a lot of sensitive information.
While it's a more complicated method to steal personal information (spam filters and antivirus programs usually detect such attempts), if successful, cybercriminals can get a much wider array of data and can collect information for a long period of time.
![]() Sextortion Emails
Sextortion Emails
This is a type of phishing. In this case, users receive an email claiming that a cybercriminal could access the webcam of the potential victim and has a video recording of one's masturbation.
To get rid of the video, victims are asked to pay a ransom (usually using Bitcoin or another cryptocurrency). Nevertheless, all of these claims are false - users who receive such emails should ignore and delete them.
How to spot a malicious email?
While cyber criminals try to make their lure emails look trustworthy, here are some things that you should look for when trying to spot a phishing email:
- Check the sender's ("from") email address: Hover your mouse over the "from" address and check if it's legitimate. For example, if you received an email from Microsoft, be sure to check if the email address is @microsoft.com and not something suspicious like @m1crosoft.com, @microsfot.com, @account-security-noreply.com, etc.
- Check for generic greetings: If the greeting in the email is "Dear user", "Dear @youremail.com", "Dear valued customer", this should raise suspiciousness. Most commonly, companies call you by your name. Lack of this information could signal a phishing attempt.
- Check the links in the email: Hover your mouse over the link presented in the email, if the link that appears seems suspicious, don't click it. For example, if you received an email from Microsoft and the link in the email shows that it will go to firebasestorage.googleapis.com/v0... you shouldn't trust it. It's best not to click any links in the emails but to visit the company website that sent you the email in the first place.
- Don't blindly trust email attachments: Most commonly, legitimate companies will ask you to log in to their website and to view any documents there; if you received an email with an attachment, it's a good idea to scan it with an antivirus application. Infected email attachments are a common attack vector used by cybercriminals.
To minimise the risk of opening phishing and malicious emails we recommend using Combo Cleaner Antivirus for Windows.
Example of a spam email:

What to do if you fell for an email scam?
- If you clicked on a link in a phishing email and entered your password - be sure to change your password as soon as possible. Usually, cybercriminals collect stolen credentials and then sell them to other groups that use them for malicious purposes. If you change your password in a timely manner, there's a chance that criminals won't have enough time to do any damage.
- If you entered your credit card information - contact your bank as soon as possible and explain the situation. There's a good chance that you will need to cancel your compromised credit card and get a new one.
- If you see any signs of identity theft - you should immediately contact the Federal Trade Commission. This institution will collect information about your situation and create a personal recovery plan.
- If you opened a malicious attachment - your computer is probably infected, you should scan it with a reputable antivirus application. For this purpose, we recommend using Combo Cleaner Antivirus for Windows.
- Help other Internet users - report phishing emails to Anti-Phishing Working Group, FBI’s Internet Crime Complaint Center, National Fraud Information Center and U.S. Department of Justice.
Frequently Asked Questions (FAQ)
Why did I receive this email?
Spam emails are not personal. Cyber criminals distribute this mail in mass-scale campaigns – hence, thousands of users receive identical messages.
I have provided my personal information when tricked by this spam email, what should I do?
If you have disclosed your account credentials – change the passwords of all possibly exposed accounts and inform their official support without delay. If the exposed information was of a different personal nature (e.g., credit card numbers, passport photos/scans, credit card numbers, etc.) – immediately contact the appropriate authorities.
I have read a spam email but didn't open the attachment, is my computer infected?
While opening/reading an email is harmless, opening/clicking a malicious attachment or link will trigger malware download/installation processes.
I have downloaded and opened a file attached to a spam email, is my computer infected?
If the opened file was an executable (.exe, .run, etc.) – most likely, yes – your device was infected. However, you might have avoided it if the file was a document (.doc, .xls, .one, .pdf, etc.). These formats may need additional actions to initiate infection chains (e.g., enabling macro commands, clicking embedded content, etc.).
Will Combo Cleaner remove malware infections present in email attachments?
Yes, Combo Cleaner is capable of detecting and eliminating nearly all known malware infections. It must be stressed that running a full system scan is paramount since sophisticated malicious programs usually hide deep within systems.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion