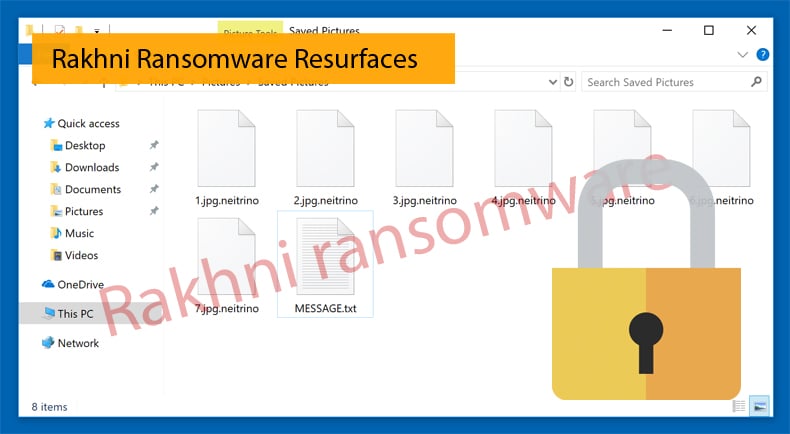
Rakhni Ransomware Resurfaces
In a few days after the publication of an article on how malware authors are adapting ransomware in more targeted attacks, another ransomware family also changes with the times. This time the Rakhni ransomware has changed, yet again, but this time it includes a coin miner. While numerous other ransomware strains picked up a lot of media attention, be they Locky or Cerber, Rakhni has kept a far lower profile. Despite the low profile it continued to be changed and adapted for certain other tasks the malware authors deem appropriate.
Rakhni was first seen in the wild in 2013 were analysts gave it the codename Trojan-Ransom.Win32.Rakhni. It was not known then but Rakhni was to become a long-lived malware family known for keeping a low profile. Since it had been spotted in the wild the ransomware has been changed by its authors to include numerous features over the years. Some of the changes include:
- How the trojan itself gets keys, this changed from locally generated keys to those received from the C&C
- Algorithms used, from initially using only a symmetric algorithm to a total of 18 symmetric algorithms used simultaneously
- The crypto-libraries have changed over the years to include LockBox, AESLib, DCPcrypt
- The distribution method favored by the authors has changed from spam email campaigns to remote execution.
Recently researchers at Kaspersky Labs have detected samples of Rakhni that include a crypto miner, or coin miner, in an attempt to make more money by utilizing the victims CPU. In a report published by the Russian firm, they have seen this new variant in Russia, Kazakhstan, Ukraine, Germany, and India. It has been distributed via a spam email campaign, in one instance the spam email was disguised as a financial document. This is an indicator that the authors behind Rakhni appear to be targeting corporate entities rather than individuals.
The spam emails from Rakhni's authors contain malicious file attachments in the form of Word DOCX documents. Opening the DOCX file opens a contained PDF document that in turns tries to run an EXE file. Users should be safe, as long as they don't enable macros in the first DOCX file. To ensure that macros are not enabled users should not click on the enable editing button in Microsoft Word. This is solid advice for preventing numerous other malware types from infecting a targeted computer.
Will it Mine or Encrypt?
Once the PDF document is opened it will first display an error message to say that the file cannot be opened. Then, the malware will disable Windows Defender and install forged digital certificates. The malware then will attempt to keep a low profile and avoid detection. If the malware remains undetected for a period of time it will either mine or encrypt.
How the malware decides to mine or encrypt is rather interesting if rather simple. If Rakhni finds a folder named Bitcoin on the PC, it runs the ransomware module. If not, then the malware will run the crypto miners module. The reasoning behind the decision is unclear, but it may have to do with the ransomware attempting to encrypt a user's wallet private keys and prevent the user from accessing his Bitcoin funds. Another reasoning and the more obvious one is that by finding a Bitcoin folder, the Rakhni authors may believe the user is an owner of cryptocurrency funds. It is then assumed that the user may not have problems obtaining the funds to pay the ransom after his files are encrypted.
If the malware runs the mining module once it has been unable to detect any file with Bitcoin in the name, it will first see if the victim’s computer will be able to handle intense coin-mining operations. Then it will download the module from a remote server and install it. Researchers at Kaspersky say that the miner will mine cryptocurrencies such as Monero, Monero Original, or Dashcoin.
The malware itself has a few more surprises. One of those being a worm component that will attempt to detect and spread across the network to infect other computers. In order to do this, the trojan module contained within the malware will create a list of all the computers on the network which share resources. For each computer listed in the file the trojan checks if the folder Users is shared and, if so, the malware copies itself to the folder \AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup of each accessible user. The second surprise to researchers was that the malware is self-deleting. Before shutting down the malware creates a batch file that deletes all ‘temporary’ files created during the infection process.
Miners Everywhere
While Kaspersky has seen a drop in roughly 30% of ransomware detections in the period of April 2017 to March 2018 ransomware can still be a valuable tool in a hacker’s arsenal. The latest changes to Rakhni would indicate this. Those behind the ransomware are looking to cover all their bases it would seem and ensure some kind of profit at the end of the day be it by ransom or the slower, stealthier mining route. While ransomware detections may be down, crypto miner detections are increasing at an alarming rate. Imperva at the start of the year released research which revealed that crypto miners were driving nearly 90% of all remote execution attacks the firm detected. It is little wonder the authors of Rakhni also wanted to get in on the action.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion