NanoCore Proves Hard to Kill
Remote Access Trojans, or RAT, are a favored malware variant of hackers and other cybercriminals across the globe. The use of such trojans is as varied and diverse as those using them illegally. They have been seen in cyber espionage campaigns to financial fraud campaigns and are a stable tool in any hacker’s bag of tricks. Simply put a RAT is merely is a back door to a targeted system that gives the hacker administrative control over the system. They are normally downloaded invisibly and predominantly spread via malicious emails.
Often when security researchers discuss an interesting aspect of a piece of malware, those infected will see it as more frustrating than interesting. NanoCore can remain on a system even once its processes are killed is such an aspect. Interesting to some, frustrating to those affected. In a report published by researchers at Fortinet noticed that a recently found sample of the NanoCore RAT which is able to prevent users from killing its processes.
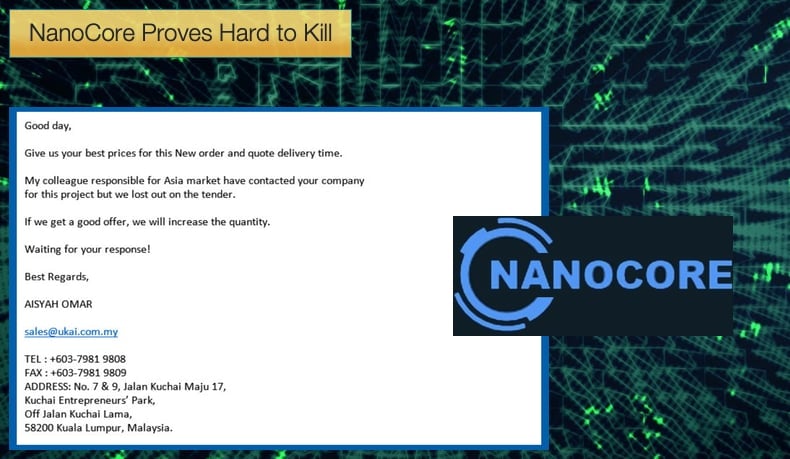
The sample seen by researchers was been spread via malicious Microsoft Word document. The malicious document, ominously called “eml_-_PO20180921.doc” is spread via phishing campaigns and contains auto-executable malicious, obfuscated VBA code which initiates the Trojan. Once opened the document contains a security warning at the top informing the would-be victim that macros have been disabled, but should that individual click “enable content,” the infection process begins.
According to researchers at Fortinet, the version of NanoCore used in the sample is version 1.2.2.0, first launched in 2015, and is downloaded from the domain wwpdubai.com. It is then saved in the Windows temporary folder as a .exe file. Before the malware goes any further it checks to see if there is already a version of NanoCore on the computer and if a version of Avast antivirus is installed. If both conditions are answered in the negative the code will then extract an archive within the executable and retrieve another file which is the actual NanoCore RAT.
Once the actual NanoCore is installed two processes will begin running. The first is Netprotocol.exe which unzips the malware. The second process is dll.exe which is designed to keep the Trojan running. The process starts netprotocol.exe, injects NanoCore into memory, and runs the code. One of the process' classes is called “ProtectMe” with a function “ProtectMe.Protect()” which prevents the process from being killed off by the victim. During testing, researchers were unable to kill the netprotocol.exe even though it is not a system service or having higher privileges than the user. It was discovered that the process uses a function called ZwSetInformationProcess which is able to modify the state of the process and prevent it from being disabled.
Further researchers discovered that,
“There is a function named ‘RunPE.doIt()’ that is used to run and protect the NanoCore RAT client. It calls the API CreateProcessA to start a new ‘netprotocol.exe’ and then suspends it. Next, it allocates memory in the new "netprotocol.exe" and puts the entire NanoCore into the newly allocated memory using the API WriteProcessMemory. Finally, it modifies the entry point of the thread context to NanoCore's entry point and resumes NanoCore running inside the second "netprotocol.exe" by calling the API ResumeThread.”
NanoCore’s Troubled Past
Initially sold cheaply on forums the first cracked versions of NanoCore emerged in 2013. Originally been sold for 25 USD was it leaked and was cracked it now become free to any looking to leverage the malware. Proving free is almost always better than cheap and that there is little honor among thieves simultaneously. The first leaked version was nothing to write home about with very few capabilities enabled. By February 2014, a beta version with more capabilities was released. Some after that the source code was leaked and now free to use. Throughout 2014 a tug of war occurred with the malware author and those leaking the code. In March 2015, version 1.2.2.0 was leaked to the hacking public. This was to be the last version released and the one used in the most recent campaign analyzed by Fortinet.
There would be now versions following 1.2.2.0 due the malware author been arrested. Taylor Huddleston, 27, of Hot Springs, Arkansas, admitted that he was the developer of NanoCore and attempted to sell the malware over popular hacker forums. In the court papers, Huddleston’s case was presented as follows,
“By developing NanoCore and distributing it to hundreds of people, some of whom he knew intended to use it for malicious purposes, Huddleston knowingly and intentionally aided and abetted thousands of unlawful computer intrusions and attempted unlawful computer intrusions, including intrusions and attempted intrusions that occurred within the Eastern District of Virginia... Huddleston agrees the evidence would show that NanoCore was used in a massive “spear phishing” scheme designed to infect and attempt to infect thousands of victim computers, including computers within the Eastern District of Virginia.”
Huddleston was ultimately sentenced to 33 months in jail, with the reason for his guilt being that he knowingly distributed the malware with the knowledge that it would be used for malicious purposes.
Despite there been no subsequent versions, 1.2.2.0 is still a nasty piece of code. Not only, as seen above, is the malware capable of resisting attempts to kill processes, it also boasted many desirable features and capabilities including:
- a keylogger that allowed customers to record all keystrokes typed
- a password stealer that extracted passwords saved and sent them over the Internet to customers
- the ability for customers to remotely turn on webcams and spy
- the ability to view, delete, and download files
- the ability to lock infected computers until users paid customers a ransom
- a "booter" or "stressor" that allowed infected computers to participate in distributed denial-of-service attacks
It is little wonder why NanoCore is still in demand despite not having a substantial update since 2015.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion