Trojan Dropped via Context-Aware Phishing Campaign
Researchers have seen a new campaign dropping the Qbot banking trojan via a phishing email campaign. The campaign was discovered by the JASK Special Operations Team. The trojan is dropped via camouflaging the spam email as parts of previous conversations in order to help avoid detection. The Qbot trojan is by no means new, first appearing in 2009, despite its age it has gone through numerous updates and evolutions in order to steal financial data and banking credentials from their targets. Numerous updates have also enabled the trojan to drop additional malware, to log user keystrokes, and create a backdoor to compromised machines. According to the JASK Special Operations Team,
“The delivery mechanism for this Qbot infection was a phishing campaign where the targeted user received an email containing a link to an online document. Interestingly enough, the delivery email was actually a reply to a pre-existing email thread.”
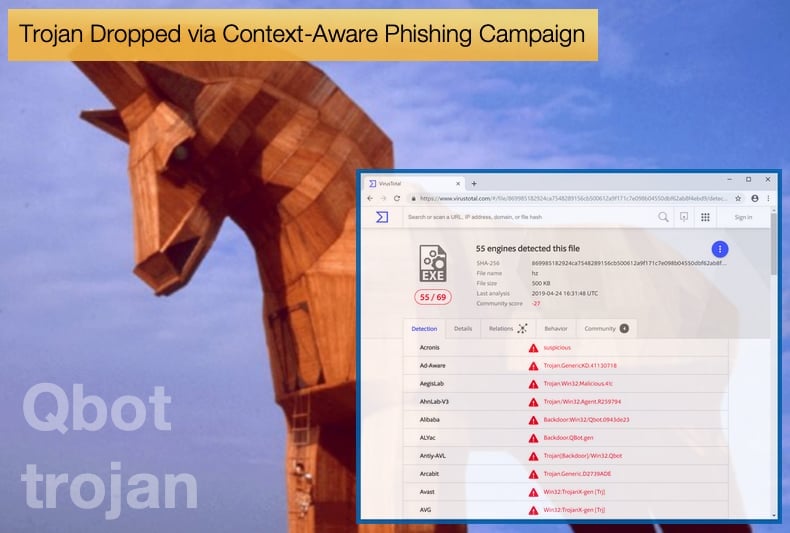
The team of researchers published their findings in an article which further showed that the link used by the hackers contained a VBScript-based dropper script packed as a ZIP archive and designed to drop the Qbot malware payload after being launched by the victim. The trojan is then downloaded by abusing the legitimate Windows BITSAdmin utility (bitsadmin.exe). The file that is used to hide the trojan is titled “August.png” and has up until the time of writing been detected 55 times on VirusTotal.
This latest version of Qbot has a number of interesting features, one such feature is how it ensures persistence on a system, it does this by copying itself and creating a registry value to have its loader launched when the user logs on, a scheduled task to relaunch itself every 5 hours, as well as a shortcut in the startup folder for good measure.
Further, the malware loader will inject itself into an explorer.exe process and will also overwrite its own executable with a 32-bit version. Once it has ensured its persistent presence on an infected computer the malware will start brute forcing network accounts for lateral movement purposes using a list of local account credentials.
The current version of Qbot will then employ various techniques to steal as much financial data as possible from its victims, which gets sent to its masters' command-and-control servers. These techniques include:
- Keylogging. Qbot captures and sends every keystroke that the victim enters and uploads them to the attacker.
- Searching for credentials or cookies. Qbot searches for saved credentials or cookies from browsers and sends them to the attacker.
- Hooking. The main payload injects to all the processes in the system with a code that hooks API calls and searches for financial/banking string the malware extracts the data, credentials, or session cookies from the process and uploads it to the attacker.
Context-Aware Phishing
As mentioned above the malware is dropped via context-aware phishing. This phishing technique is a highly targeted form of phishing where the attacker will use carefully crafted decoy content customized for each target recipient. Often the attacker will first perform a recon campaign in order to get information that they can then utilize to craft the customized emails that would make up the context-aware campaign. Upon deeper analysis, the attacker will often use the intended victim's social media profiles to gain more insight or by using a massed spam email that would link to what is called a non-critical website. Such websites are designed to harvest information and do not provide the attacker with an immediate financial reward. Another method of harvesting information is by analysing a victim’s browsing history. Too many malware variants have such a feature built-in to list here.
One of the earliest known context-aware phishing campaigns was discovered by Palo Alto Networks Unit 42 in 2017. In this instance, it was discovered that method was leveraged with a Microsoft Word Office/WordPad Remote Code Execution Vulnerability (CVE-2017-0199). This campaign targeted a bank based in the Middle East, trademark and intellectual property service companies based in Europe, an international sporting organization, and individuals with indirect ties to a country in North East Asia. Since then numerous other instances have been seen using this technique.
Returning to the Qbot trojan, the incident investigated by the JASK team is not the only time the malware has been seen in an active campaign this year. Security firm Varonis also discovered the trojan been deployed in a campaign in March 2019. According to researchers the campaign actively targeted U.S. corporations but has hit networks worldwide, with victims throughout Europe, Asia, and South America, with the trojan’s main goal of stealing proprietary financial information, including bank account credentials.
Fortunately, banking trojans can be defended against, and often involving simple changes to user’s online behavior. One of the easiest methods is enabling two-factor authentication where ever available. Many banks and their online banking channels have such security measures in place ready for customers to adopt. Another way to help prevent infections is by dedicating a non-Windows internet browser, like Google’s Chrome or Mozilla’s FireFox, to solely been used for online banking. Further having a robust anti-virus solution also decreases the chances of infection greatly. Users can also adopt the following good habits to not only prevent banking trojan infections but other malware infections as well:
- Make sure the system's anti-virus software is automatically updated to detect new strains of malware
- Keep operating systems and Web browsers fully patched.
- Use Web content filters to block ads that may contain drive-by downloads.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion