LokiBot Now Hidden in Images
State-sponsored actors have long known that hiding malware in images, a technique called steganography, is an effective way to distribute and infect users with malware. Steganography can be defined as the technique of hiding secret data within an ordinary, non-secret, file or message to avoid detection. The secret data is then extracted and sent to its target destination. This technique is often employed by including malware within the hidden text of an image, whether .jpg or other formats, the malware is often encrypted to prevent detection. Since the use of the technique was popularised by state-sponsored actors, hackers have since adopted the technique to further their goals.
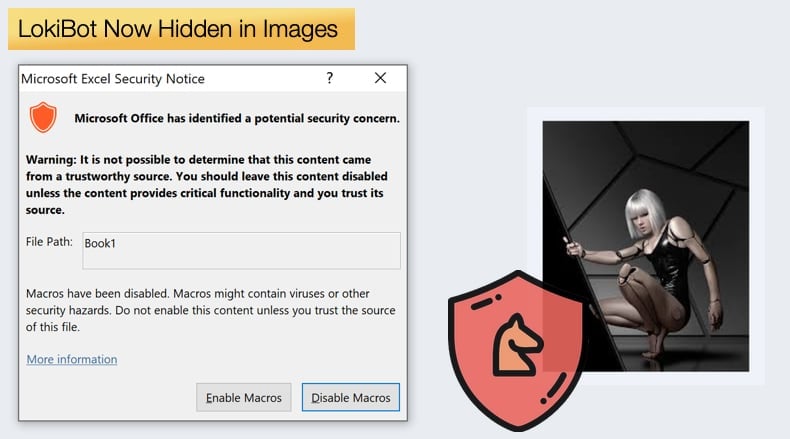
Now, according to an article published by security firm Trend Micro, the LokiBot malware family has been upgraded to use steganography to infect victims. Steganography is used for legitimate purposes, such as assisting in protecting intellectual property, this is not the case for LokiBot. A recent analysis of LokiBot has revealed that the latest variant has been encrypted and hidden in .png image files. Further, malicious archive files were also detected in spam emails. The latest variant was detected when a phishing email was sent to a company in South East Asia. The mail contained a Microsoft Word .doc attachment containing two objects, a Microsoft Excel 97-2003 Worksheet and a package labeled “package.json.” A scan on VirusTotal uncovered other, similar samples containing very similar if not the same steganographic elements.
If a user opens the malicious file the file is opened. Upon opening a script will install the malware as a .exe file in a temporary folder, alongside a .jpg file containing LokiBot source code. The image which hides LokiBot can be opened as an image but it still contains the LokiBot unpacking routine. The loader searches for a marker within the hidden text of the image, the marker is a string variable in this case.
Once the marker is detected the encryption process begins, but rather than using one of the many decryption processes available, the malware authors employ a custom decryption process to match the custom encryption. Once decrypted the code to LokiBot is unpacked and loaded to the computer’s memory. The researchers analyzing this new variant concluded,
“One likely reason for this particular variant's reliance on steganography is that it adds another layer of obfuscation -- wscript (the VBS file interpreter) is used to execute the malware instead of the actual malware executing itself. Since the autostart mechanism uses a script, future variants can choose to change the persistence method by modifying the script file on the fly.”
LokiBot is a particularly nasty information stealer and undergone numerous updates since its discovery to further enhance its capabilities. Beyond the use of steganography, LokiBot can act as a keylogger, and can establish backdoors in Windows systems to both maintain persistence and send stolen data to the attacker's command-and-control server. Trend Micro confirmed that phishing emails containing the new variant had been sent to 56 other organizations that Trend Micro was aware of. Researcher’s concluded that,
“As one of the most active information stealers in the wild today, LokiBot shows no signs of slowing down. The updates to its persistence and obfuscation mechanisms show that LokiBot is still being updated and will likely remain a threat to be dealt with in the near future.”
LokiBot Malware for Sale
LokiBot was first discovered in 2015 when it was advertised on underground forums as a password and crypto wallet stealer. Despite that, the fairly bland sales pitch seen countless times hid something more. Researchers published a white paper published in 2017. It was noted that LokiBot up until 2017 had successfully kept itself under the radar. Security researchers had not given the information stealer much thought or analysis. This posed a problem to those infected with LokiBot or defending against an ongoing campaign. The white paper makes for incredibly technical reading but allowed for a complete analysis of the malware. Despite this LokiBot remains a threat mainly due to the constant stream of updates. In 2018 researchers again from Trend Micro discovered the malware abusing Microsoft Installer to infect victims. The new installation method was used to bypass detection by security software packages. Due to numerous malware families using the same techniques, for example, been downloaded via Wscript, Powershell, Mshta.exe, Winword.exe, security software has become incredibly good at detecting such abuses. This means that if hackers want to be successful new evasion techniques need to be found. In this instance, it was abusing Windows Installer, with the latest variant the malware is encrypted and hidden in an image to do the same thing.
The good news is that those distributing LokiBot still rely on phishing email campaigns to distribute the malware. This means that users can mitigate infections before they happen by adopting cybersecurity best practices. According to Trend Micro users can do the following to prevent infection:
- Be wary of grammatical and typographical errors. Business emails, especially communications between a business and its suppliers, will usually be written professionally. An email that contains blatant grammatical or typographical errors could be a sign that it is a malicious email.
- Double-check the email address of the sender. The easiest way to determine if an email is authentic is to check the sender’s email address. If it doesn’t use the official domain of the sender’s organization or uses an unusual email, that’s a red flag.
- Context. If the email content fails to provide context regarding the discussion (such as a one-liner) and also includes a link or an attachment, then there is a high chance that it is a malicious spam attempt.
- Don’t click or download. Even if an email looks legitimate, it’s still prudent to avoid clicking on any links or downloading any files until the source is verified to be legitimate. Hacked email accounts have previously been used for spear phishing.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion