Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What kind of malware is LokiBot?
LokiBot is trojan-type malware designed to infiltrate systems and collect a wide range of information. Note that this virus targets the Windows and Android operating systems. LokiBot typically infiltrates systems without users' consent - it is distributed via spam emails (Windows OS), various private messages (SMS, Skype, etc.), and malicious websites.
LokiBot on Windows OS:
A main feature of LokiBot is to record sensitive data. This behavior is very common to trojan-type viruses. LokiBot gathers saved logins/passwords (mostly in web browsers) and continually tracks users' activity (for instance, recording keystrokes). Recorded information is immediately saved on a remote server controlled by LokiBot's developers.
LokiBot on Android OS:
As with the Windows OS version, LokiBot collects sensitive information relating to user accounts. In this case, however, the entire process is much more advanced. This malware simulates the interface of applications that require logins/passwords.
For example, LokiBot might display false notifications informing victims that someone is supposedly transferring money into their account. After clicking the notification, users are asked to login to their accounts, however, since the login screen is fake, all information is immediately recorded and sent to a remote server.
This malware is capable of simulating a number of other apps, including Outlook, Skype, WhatsApp, etc. The scam model is identical - users are notified and then asked to log in. In addition, LokiBot can use the infected device to proliferate itself via spam (SMS messages, emails, and so on).
Once a user attempts to remove LokiBot from the device, the malware asks for administrator permissions. If the user does not grant them, LokiBot locks the device screen and encrypts stored data. It then displays a ransom-demand message. To restore compromised files and unlock the device, users are encouraged to pay a ransom of ~$100 in the Bitcoin cryptocurrency.
Fortunately, the encryption process is not flawless - LokiBot leaves copies of compromised data under different names. Therefore, restoring files is not difficult. Furthermore, this malware can be removed using Android Safe Mode.
In summary, LokiBot's presence is very dangerous - collected data can lead to serious privacy issues and significant financial losses.
Cyber criminals can exploit received data to transfer money from victims' accounts. In addition, they can misuse victims' email addresses and other accounts (e.g., social networks) to proliferate malware by tricking contacts/friends into downloading various executables or clicking links.
Cyber criminals might also misuse victims' identities to contact other people and ask them to transfer money into certain accounts (for example, using these assumed identities, they claim to be in trouble and ask to borrow money). Note that the LokiBot's executable is sold on the 'Dark Web' for $2000.
Therefore, any aspiring cyber criminal can purchase it and start proliferating this malware. It is difficult to determine what the collected data is used for, since LokiBot is not particularly advanced malware. Nevertheless, it can cause serious problems for the user. Fortunately, most reputable anti-virus/anti-spyware suites are capable of detecting and removing LokiBot.
Therefore, we strongly advise you to have this software installed and running at all times. You are also advised to periodically run full system scans to check for any infections that have found their way into your system.
| Name | LokiBot trojan |
| Threat Type | Trojan, password-stealing virus, banking malware, spyware. |
| Detection Names | Avast (Win32:Trojan-gen), BitDefender (Trojan.GenericKD.41149271), ESET-NOD32 (A Variant Of Win32/Injector.EEMP), Kaspersky (Backdoor.Win32.Androm.rlsi), Full List (VirusTotal) |
| Malicious Process Name(s) | objectindvarsle.exe (the process name may vary). |
| Symptoms | Trojans are designed to stealthily infiltrate the victim's computer and remain silent, and thus no particular symptoms are clearly visible on an infected machine. |
| Distribution methods | Infected email attachments, malicious online advertisements, social engineering, software 'cracks'. |
| Damage | Stolen passwords and banking information, identity theft, the victim's computer added to a botnet. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Similarities with other malware
There are dozens of trojan-type viruses that share similarities with LokiBot. The list of examples includes (but is not limited to) Emotet, Pony, Adwind, and TrickBot. All gather information and store it remotely. In most cases, these viruses have just one purpose: to help developers steal unsuspecting users' money.
Some trojans, however, have additional features. For example, they often misuse system resources to mine cryptocurrencies. This is done without consent and all revenue goes to the developers. Therefore, overall performance is significantly diminished and users receive nothing in return.
How did LokiBot infect my computer?
As mentioned above, LokiBot is distributed using spam emails/messages. Note that the email messages do not follow any specific pattern - the only common factor is that all are presented as invoices/bills. In most cases, these trojan-proliferating spam emails are virtually identical - the entire structure (text, alignment, etc.) is very similar and the malicious attachment is identical.
LokiBot can be distributed in any form - compressed executable, MS Office document, and so on - however, the result is identical: after clicking deceptive links and opening malicious attachments, the system is infected with LokiBot. Remember that the main reasons for computer infections are poor knowledge and careless behavior.
How to avoid installation of malware?
To prevent this situation, be very cautious when browsing the Internet and downloading/installing software. Think twice before opening email attachments. If the file seems irrelevant or has been received from a suspicious/unrecognizable email address, do not open it. These emails should be deleted immediately, without reading.
Furthermore, download your software from official sources only, using direct download links. Third party downloaders/installers often include rogue apps (that can cause chain infections), and thus should never be used.
Download Android applications from Google Play only. In addition, be very cautious - we strongly advise you to read the user reviews and see if there are any negative responses (although applications in Google Play are scanned before being posted, there still are some that are classed as rogue).
As mentioned above, having a legitimate anti-virus/anti-spyware suite installed and running is paramount. The key to computer safety is caution. If your computer is already infected with LokiBot, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
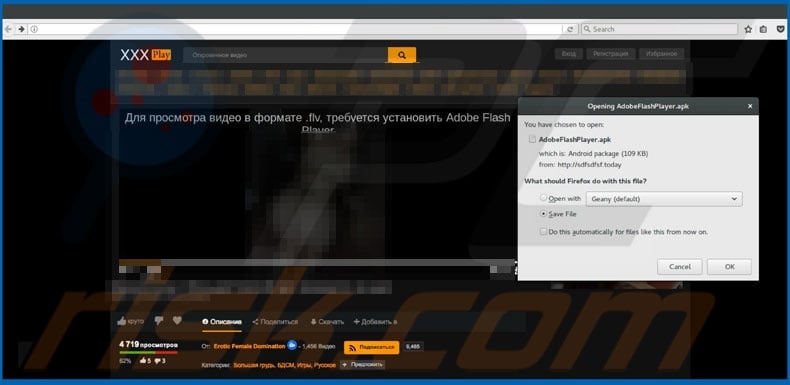
Malicious website used to distribute LokiBot Android version (presenting it as Adobe Flash Player):
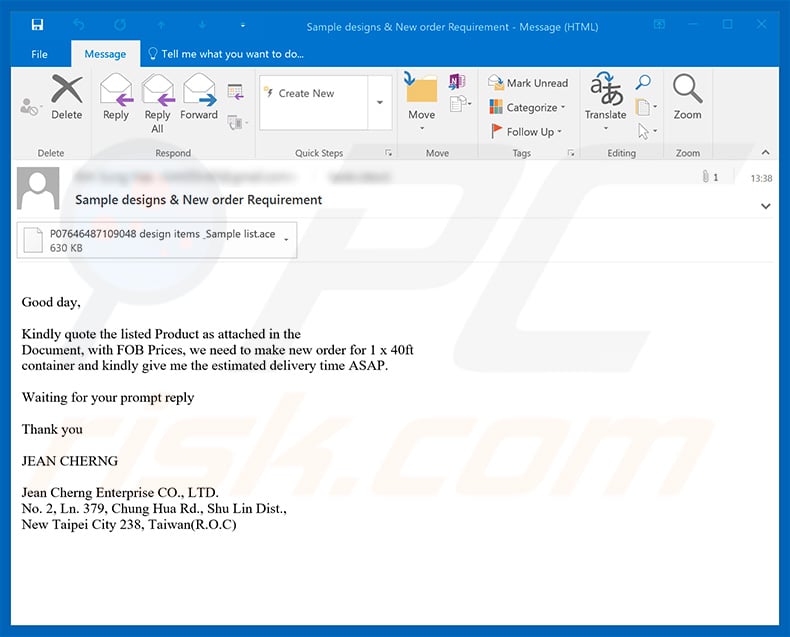
An example of deceptive email distributing LokiBot malware:

Text presented within this email:
Please find our urgent Inquiry and Purchase Order attached. We hope to get a reply today. I have sent this same document twice already without any reply. Our prices are based on your offer to our customer who is also your client We received your contact from your customer's recommendation for the parts we need_ Can you ship to our country? Please confirm
I have called you severally and written your email without reply_ Can you give me the right person to contact for our inquiries and our Purchase Order?
In the attached order, the items marked yellow can be skipped if not available_ I await your reply with order confirmation.
Thanks & Regards!! Priti Patel
M.R. Organisation (U.S.A) LLC. 800 West Cummings Park Suite 1650, Woburn MA 01801 U.S.A.
Cell: +1-857-389-1763 I Office # 1-339-999-2798, 1-339-999-2799 I Fax # 1-978-945-832 I Email : sales3(iemrocompparts.com www.mrocompparts.com
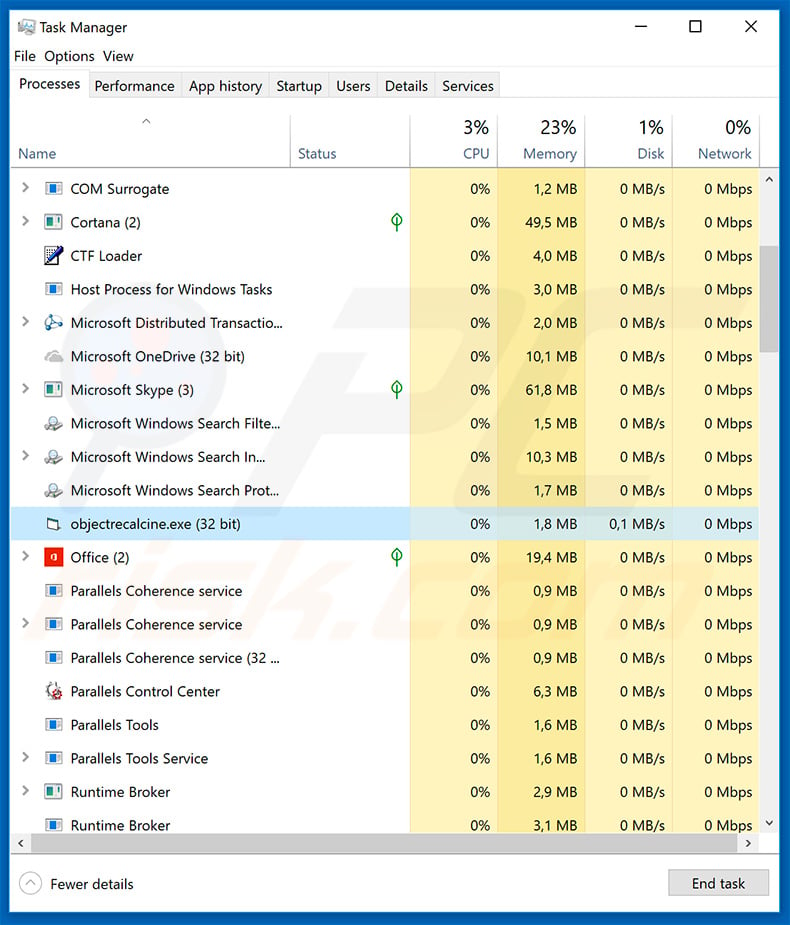
Example of LokiBot's process ("objectrecalcine.exe") in Windows Task Manager:
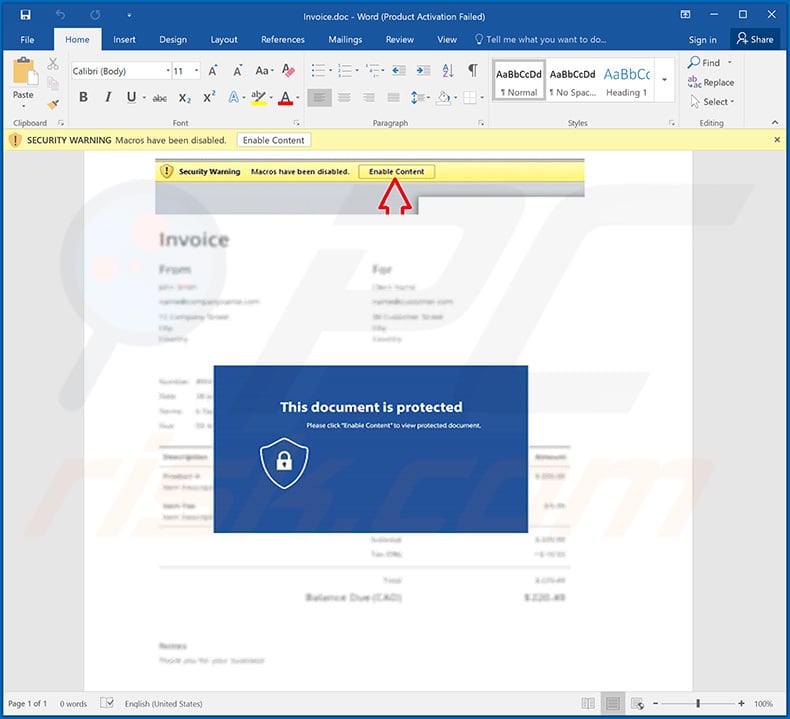
Example of a malicious Microsoft Word document (fake invoice) distributing LokiBot malware:
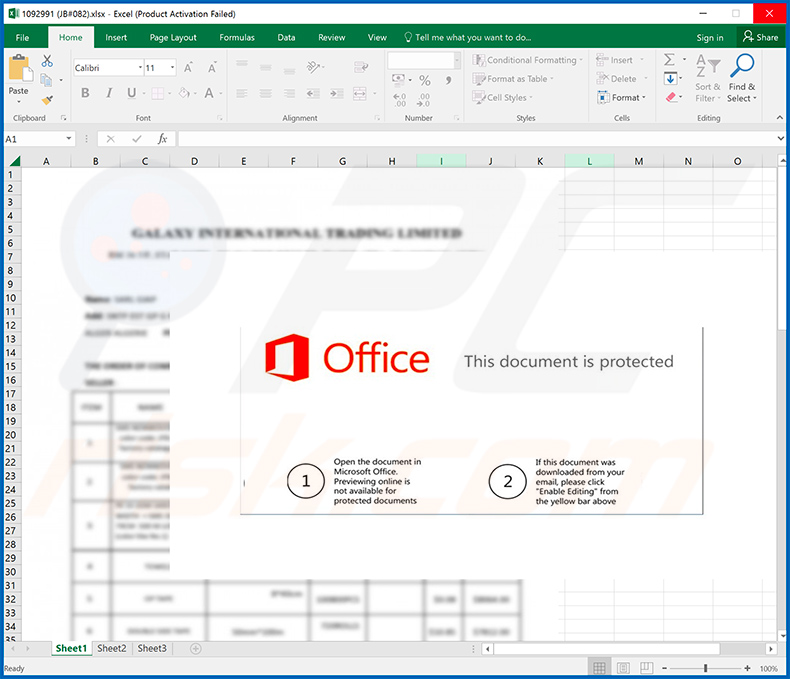
Example of a malicious Microsoft Excel document ("1092991 (JB#082).xlsx") used to spread LokiBot malware:
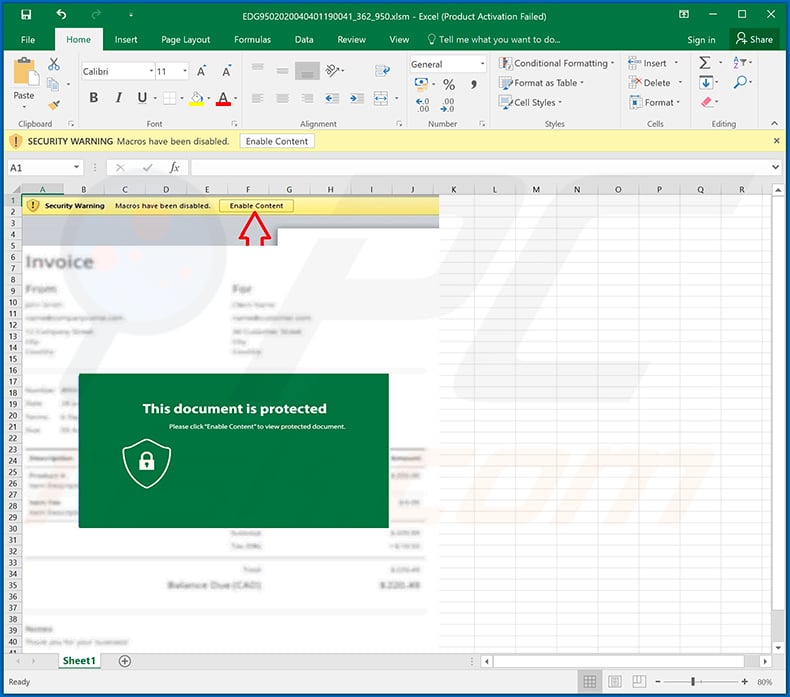
Example of another malicious Microsoft Excel document ("EDG9502020040401190041_362_950.xlsm") which spread LokiBot malware:
Examples of Coronavirus-themed spam emails used to spread LokiBot trojan via attached files:
Example 1:
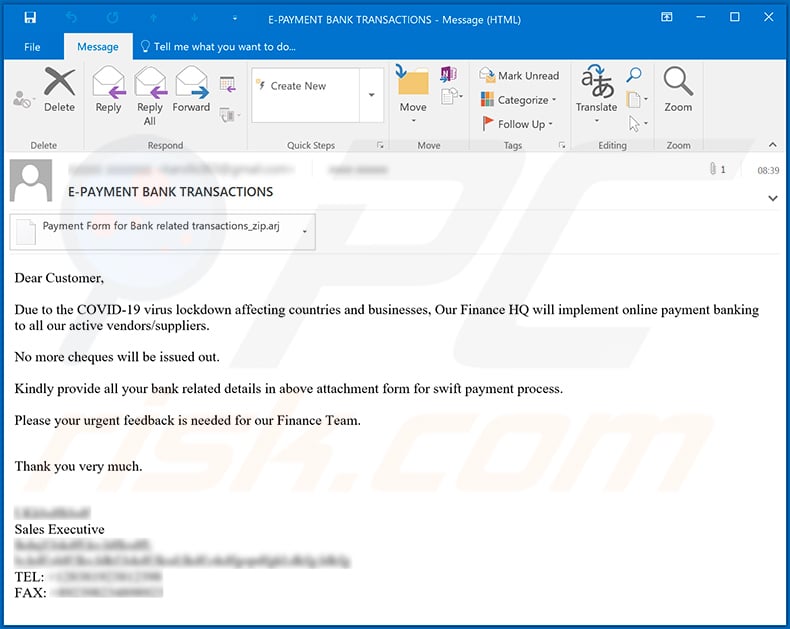
Text presented within:
Subject: E-PAYMENT BANK TRANSACTIONS
Dear Customer,
Due to the COVID-19 virus lockdown affecting countries and businesses, Our Finance HQ will implement online payment banking to all our active vendors/suppliers.
No more cheques will be issued out.
Kindly provide all your bank related details in above attachment form for swift payment process.
Please your urgent feedback is needed for our Finance Team.
Thank you very much.Sales Executive
Example 2:
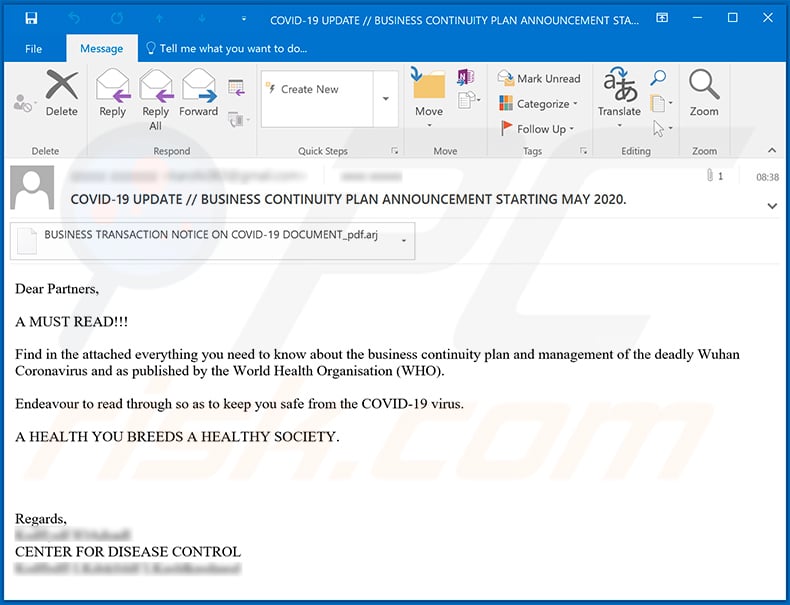
Text presented within:
Subject: COVID-19 UPDATE // BUSINESS CONTINUITY PLAN ANNOUNCEMENT STARTING MAY 2020.
Dear Partners,
A MUST READ!!!
Find in the attached everything you need to know about the business continuity plan and management of the deadly Wuhan Coronavirus and as published by the World Health Organisation (WHO).
Endeavour to read through so as to keep you safe from the COVID-19 virus.
A HEALTH YOU BREEDS A HEALTHY SOCIETY.
Regards,
CENTER FOR DISEASE CONTROL
Example of a DHL-themed spam email used to spread LokiBot trojan via attached .dmg file:
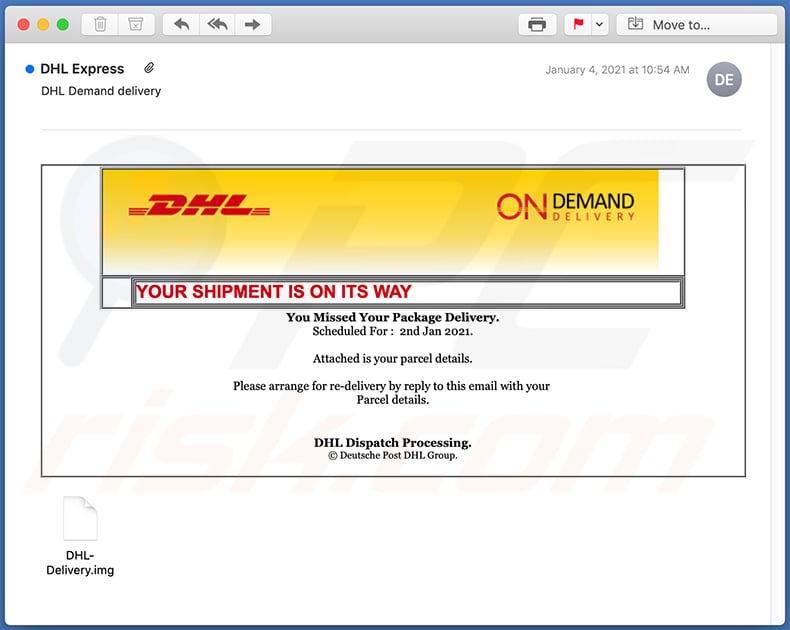
Text presented within:
Subject: DHL Demand delivery
On Demand Delivery
YOUR SHIPMENT IS ON ITS WAY
You Missed Your Package Delivery.
Scheduled For : 2nd Jan 2021.Attached is your parcel details.
Please arrange for re-delivery by reply to this email with your
Parcel details.
DHL Dispatch Processing.
© Deutsche Post DHL Group.
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is LokiBot?
- STEP 1. Manual removal of LokiBot malware.
- STEP 2. Check if your computer is clean.
How to remove malware manually?
Manual malware removal is a complicated task - usually it is best to allow antivirus or anti-malware programs to do this automatically. To remove this malware we recommend using Combo Cleaner Antivirus for Windows.
If you wish to remove malware manually, the first step is to identify the name of the malware that you are trying to remove. Here is an example of a suspicious program running on a user's computer:

If you checked the list of programs running on your computer, for example, using task manager, and identified a program that looks suspicious, you should continue with these steps:
 Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:
Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:

 Restart your computer into Safe Mode:
Restart your computer into Safe Mode:
Windows XP and Windows 7 users: Start your computer in Safe Mode. Click Start, click Shut Down, click Restart, click OK. During your computer start process, press the F8 key on your keyboard multiple times until you see the Windows Advanced Option menu, and then select Safe Mode with Networking from the list.

Video showing how to start Windows 7 in "Safe Mode with Networking":
Windows 8 users: Start Windows 8 is Safe Mode with Networking - Go to Windows 8 Start Screen, type Advanced, in the search results select Settings. Click Advanced startup options, in the opened "General PC Settings" window, select Advanced startup.
Click the "Restart now" button. Your computer will now restart into the "Advanced Startup options menu". Click the "Troubleshoot" button, and then click the "Advanced options" button. In the advanced option screen, click "Startup settings".
Click the "Restart" button. Your PC will restart into the Startup Settings screen. Press F5 to boot in Safe Mode with Networking.

Video showing how to start Windows 8 in "Safe Mode with Networking":
Windows 10 users: Click the Windows logo and select the Power icon. In the opened menu click "Restart" while holding "Shift" button on your keyboard. In the "choose an option" window click on the "Troubleshoot", next select "Advanced options".
In the advanced options menu select "Startup Settings" and click on the "Restart" button. In the following window you should click the "F5" button on your keyboard. This will restart your operating system in safe mode with networking.

Video showing how to start Windows 10 in "Safe Mode with Networking":
 Extract the downloaded archive and run the Autoruns.exe file.
Extract the downloaded archive and run the Autoruns.exe file.

 In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.
In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.

 Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
You should write down its full path and name. Note that some malware hides process names under legitimate Windows process names. At this stage, it is very important to avoid removing system files. After you locate the suspicious program you wish to remove, right click your mouse over its name and choose "Delete".

After removing the malware through the Autoruns application (this ensures that the malware will not run automatically on the next system startup), you should search for the malware name on your computer. Be sure to enable hidden files and folders before proceeding. If you find the filename of the malware, be sure to remove it.

Reboot your computer in normal mode. Following these steps should remove any malware from your computer. Note that manual threat removal requires advanced computer skills. If you do not have these skills, leave malware removal to antivirus and anti-malware programs.
These steps might not work with advanced malware infections. As always it is best to prevent infection than try to remove malware later. To keep your computer safe, install the latest operating system updates and use antivirus software. To be sure your computer is free of malware infections, we recommend scanning it with Combo Cleaner Antivirus for Windows.
Frequently Asked Questions (FAQ)
What are the biggest issues that malware can cause?
It can encrypt files, steal sensitive information (e.g., credit card details, login credentials), infect computers with additional malware, mine cryptocurrency, and more. It depends on the type of malware (its capabilities).
What is the purpose LokiBot malware?
LokiBot collects information. On Windows computers, it can steal saved logins/passwords (mostly from web browsers) and continually track activity. On Android devices, it attempts to steal login credentials by simulating the interface of various apps (e.g., Skype, Outlook, WhatsApp). Also, LokiBot can lock the device screen and encrypt stored data. More information about LokiBot is provided in our article above.
How did LokiBot infiltrated my computer?
LokiBot is distributed via email. Threat actors send emails containing malicious attachments (MS Office documents). LokiBot infects computers after opening a malicious MS Office document and enabling macros commands. Another popular way to distribute malware is to upload it to various cracked software distribution pages or use fake installers, torrent sites, P2P networks, and similar channels.
Will Combo Cleaner protect me from malware?
Yes, Combo Cleaner can detect and eliminate almost all known malware. High-end malware usually hides deep in the system. A computer must be scanned using a full scan to remove malware of this kind from it.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion