PyXie RAT Stealing Credentials and Passwords
Researchers have discovered a new remote access trojan (RAT), that is currently being used to steal login credentials, record video, and includes a keylogging component to assist in its objectives. Given the amount of news surfacing regarding ransomware and exploit kits most can be forgiven if they forgot RATs are still a threat. A RAT forms part of the trojan family of malware and includes a backdoor which grants administrative control of the machine infected. RATs tend to be downloaded invisibly via a user-requested program. They are also difficult to detect because they usually don't show up in lists of running programs or tasks. The actions they perform can be similar to those of legitimate programs. Furthermore, an intruder will often manage the level of resource use so that a drop in performance doesn't alert the user that something's amiss.
According to a blog post by researchers based at BlackBerry Cylance, a new RAT has been detected in the wild. Named PyXie, the malware was discovered in a campaign actively targeting healthcare and education organizations. The RAT is a Python-based custom build capable of keylogging, credential harvesting, recording video, cookie theft, and the ability to perform man-in-the-middle attacks. Further, it is believed that the malware can also be used to drop other malware families including ransomware if the hackers so chose. The malware is also designed to be stealthy in that it completes its tasks then clears evidence that it had been on the system to avoid detection. Despite these attempts to remain undetected researchers have managed to piece a fair amount of information about the RAT.
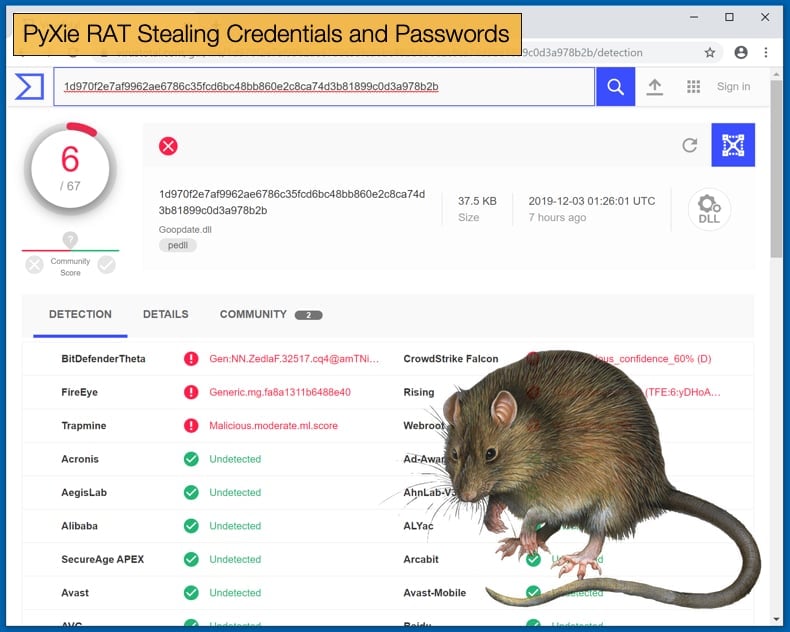
Researchers named the malware PyXie because of the way its compiled code uses a '.pyx' file extension instead of the '.pyc' typically associated with Python files. The malware has been active since 2018 and given that it is a highly customized bit of code it is safe to assume a lot of time and resources went into its development. This is often an indicator that the threat actors behind the malware are incredibly skilled. This skill is evident in how the malware infects the machine by using a method that will prevent antivirus software from detecting it. PyXie uses the technique known as side-loading where the malware leverages legitimate applications to gain a foothold on the targeted machine.
If all goes as planned antivirus software will detect the legitimate application but not the malware hiding behind it. In one instance researchers discovered the malware was been distributed by a trojanized version of a popular free online game. Once the game is downloaded it will secretly install the malware by abusing PowerShell to escalate privileges and grant admin rights to the attacker. This is followed by the third stage of the attack where the malware downloads final payload known as “Cobalt-mode” which connects to the attacker’s command and control server. In the so-called “Cobalt-mode” the hackers make use of a legitimate penetration testing tool called Cobalt Strike. This penetration testing tool has been a favorite amongst hackers as it makes attributing the attack far more difficult. To further complicate matters the downloader shares similarities with the Shifu Banking Trojan.
Misdirection
One of the reasons for using both Cobalt Strike and code similar to Shifu can be to allow the hackers to operate for longer periods without being detected. By using the same or similar code, like Shifu in this case, it forces researchers to ask whether it is the same group that built and deployed Shifu or different threat actors who either stole the code or used open-source code. In an interview with ZDNet Josh Lemos, VP of research and intelligence at Blackberry Cylance, noted that
“An advantage of utilizing a widely used tool such as Cobalt Strike is it makes attribution difficult since it is used by many different threat actors as well as legitimate pentesters. With the Shifu banking trojan similarities, it is unclear if it is the same actors or if someone else reused some of its code…This is a full-featured RAT that can be leveraged for a wide range of goals and the actors will have different motives depending on the target environment. The fact it has been used in conjunction with ransomware in a few environments indicates that the actors may be financially motivated, at least in those instances,”
The full extent of the campaign is not yet known. What is known is that researchers have identified attacks against over 30 separate organizations with hundreds of machines infected. As to who is responsible for the attack, currently, it is a guessing game. What is known is that they are skilled, well-funded, and well-organized, when this is combined with the tactics mentioned above determining who is responsible is going to be a long and difficult task for those involved.
PyXie can be defended against with researchers advising that correct cyber hygiene and best practices are adopted. It is further advised that organizations implement endpoint security suites if not already and ensure all software packages are up to date and correctly patched. Given that due to the size of healthcare and education organization’s networks this not often the case as legacy software packages are still used to save costs in certain instances. Given that the attackers seem to be focused on attacking organizations within these industries, known for at times sub-par cybersecurity measures, the hackers have picked a target to best further their aims.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion