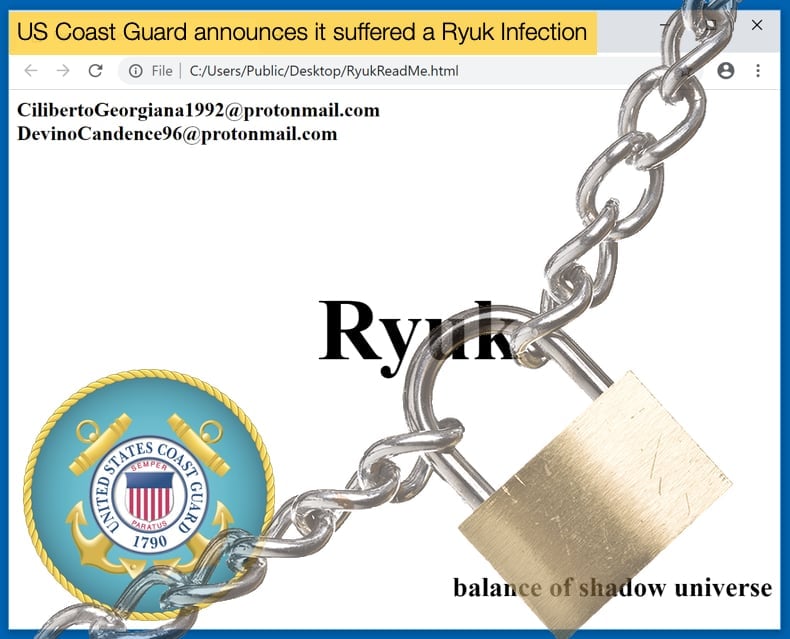
US Coast Guard announces it suffered a Ryuk Infection
The US Coast Guard announced that it had suffered a ransomware infection which resulted in the shutdown of a maritime facility for more than 30 hours. The security bulletin, published just before Christmas, also stated that the ransomware was Ryuk. The bulletin, however, makes no mention of the name or the location of the port authority, it merely described the incident as recent. The US Coast Guard noted that the security bulletin intended to inform other maritime authorities of the incident to act as a warning and hopefully prevent future attacks.
While the bulletin did not specify which port or maritime authority was impacted by the attack, it did state that they believe hackers gained access to the network via a phishing email sent to one of the authority’s employees. The agency further elaborated that,
“Once the embedded malicious link in the email was clicked by an employee, the ransomware allowed for a threat actor to access significant enterprise Information Technology (IT) network files, and encrypt them, preventing the facility's access to critical files. The virus further burrowed into the industrial control systems that monitor and control cargo transfer and encrypted files critical to process operations. The impacts to the facility included disruption of the entire corporate IT network (beyond the footprint of the facility), disruption of camera and physical access control systems, and loss of critical process control monitoring systems. These combined effects required the company to shut down the primary operations of the facility for over 30 hours while a cyber-incident response was conducted.”
During any malware infection, the spreading of malware to industrial control systems (ICS) is a nightmare scenario. These systems are designed to automate much of the industrial processes and monitoring processes. It is little wonder the unnamed port authority suffered such a period of extended downtime. Due to the value of ICS to the daily operations of corporate entities and governments often great care is taken to make sure those networks are not outwardly facing the Internet.
By separating the network from the Internet it is hoped cyber-attacks can be reduced, with the only way to gain entry would be via physical means. Based on statements made by the Coast Guard this was not the case with ICS been connected to an outwardly facing network to an extent.
Maritime Cybersecurity a Concern
The security bulletin was published on December 16, 2019, in the hope that by broadcasting the event to as many maritime facilities as fast as possible and get them to deploy countermeasures before they were targeted as well. Over the last two years ports, shipping companies and maritime authorities have become a primary target for many state-sponsored and cybercrime gangs. Predating even the last two years, security researchers raised concerns with the industry. Researchers at Kaspersky noted that trends in the sector were assisting in developing new vulnerabilities to exploit. As ships increase in size, so has the amount of crew decreased. To ensure safe sailing more electronic and automated systems have been incorporated into these ships to run less crew. Unfortunately, these new systems were easy to hack.
These security vulnerabilities did not only limit themselves to ships but port authorities and oil rigs. In September 2018, the ports of San Diego and Barcelona reported that they had suffered a security incident. Both were ransomware infections and both occurred within five days of each other. It was suggested by researchers at the time that the ransomware may have been Ryuk. Later in the same year, a conglomerate of 21 companies in the shipping and maritime sector published a report detailing measures the maritime industry must take in order o prevent cybersecurity incidents. Not only does the report contain security measures to be adopted but examples of what could happen if those measures are not comprehensively adopted.
While not a ransomware infection, the report details an incident of an unknown virus infecting the Electronic Chart Display and Information System (ECDIS) that ships use for sailing. The report elaborates further that,
“A new-build dry bulk ship was delayed from sailing for several days because its ECDIS was infected by a virus. The ship was designed for paperless navigation and was not carrying paper charts. The failure of the ECDIS appeared to be a technical disruption and was not recognized as a cyber issued by the ship's master and officers. A producer technician was required to visit the ship and, after spending a significant time in troubleshooting, discovered that both ECDIS networks were infected with a virus. The virus was quarantined and the ECDIS computers were restored. The source and means of infection in this case are unknown. The delay in sailing and costs in repairs totaled in the hundreds of thousands of dollars (US)”
While targeted by numerous malware strains, it would appear that Ransomware is still one of the more dangerous threats faced by the industry. This point was driven home when Maersk suffered a NotPetya infection. The biggest shipping company in the world landed up costing the company over 300 million USD for the recovery process. Before the company could once again resume operations IT staff had to reinstall 4000 servers and 45000 PCs. The US Coast Guard seems well aware of the problem facing the entire sector. The most recent security bulletin follows two others, released in May and July. It is hoped that through the combined effort of the authorities and corporate organizations that the ports and ships vital to the global economy become less of a target.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion