Bug Bounties are not just for Legitimate Operations
For some time now major tech companies have offered monetary rewards to those who find flaws that lead to zero-day vulnerabilities within the company's product code. Often referred to as bug bounties they can net the finder thousands of dollars, more if the vulnerability is determined to be severe or critical to future security. Now the developers of the LockBit ransomware have instituted a similar program for their latest ransomware iteration LockBit 3.0.
In what may be a world-first the ransomware’s developers are offering a bug bounty along with leaking new extortion tactics and ZCash payment options as the defining traits upon release of the new ransomware version.
For those not clued up on all the cryptocurrency altcoins, ZCash is described as,
“ZCash emerged in 2016 when a group of scientists decided they wanted to create a cryptocurrency similar to Bitcoin but with some additional features. They developed a fork of the Bitcoin blockchain, with enhanced user security and anonymity. The scientists first invented Zerocoin, which became Zerocash not too long after its initial release. Eventually, the cryptocurrency was renamed ZCash.”
LockBit began operations in 2019 and has since risen to great prominence amongst other ransomware rivals. For May 2022, the ransomware variant was responsible for almost 40% of reported ransomware attacks.
The latest version, 3.0, was released over the past weekend after being beta tested for two months and according to Bleeping Computer it has already been used in attacks.
Due to the recent release of the updated LockBit, not much is known about any technical changes to the code at this point. The new bug bounty program stands out as a defining characteristic of the new release.
According to Bleeping COmputer bounties range from 1,000 USD to 1,000,000 USD and security researchers are asked to submit bug reports to claim any financial reward.
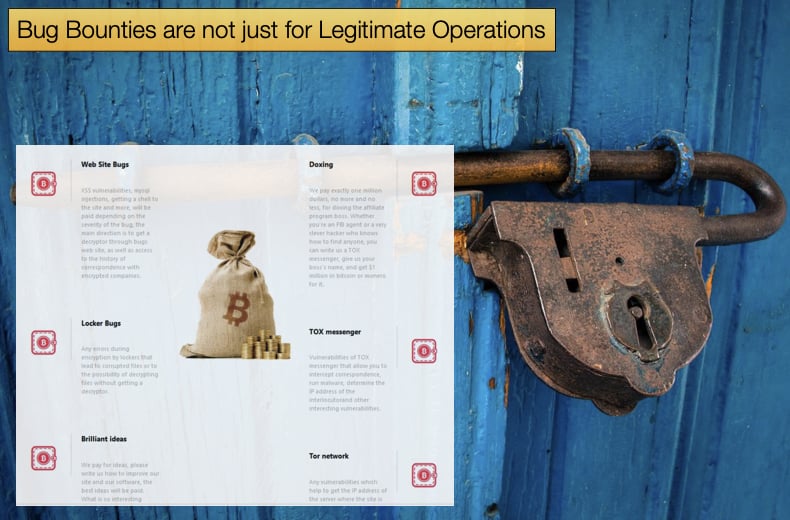
This announcement was made on a LockBit webpage announcing the bounty. The page further defined what type of bugs the developers are looking for in general, the page stating:
- Web Site Bugs: XSS vulnerabilities, MySQL injections, getting a shell to the site, and more, will be paid depending on the severity of the bug, the main direction is to get a decryptor through the bugs web site, as well as access to the history of correspondence with encrypted companies.
- Locker Bugs: Any errors during encryption by lockers that lead to corrupted files or to the possibility of decrypting files without getting a decryptor.
- Brilliant ideas: We pay for ideas, please write us about how to improve our site and our software, the best ideas will be paid for. What is so interesting about our competitors that we don't have?
- Doxing: We pay exactly one million dollars, no more and no less, for doxing the affiliate program boss. Whether you're an FBI agent or a very clever hacker who knows how to find anyone, you can write us a TOX messenger, give us your boss's name, and get $1 million in bitcoin or monero for it.
- TOX messenger: Vulnerabilities of TOX messenger that allow you to intercept correspondence, run malware, determine the IP address of the interlocutor, and other interesting vulnerabilities.
- Tor network: Any vulnerabilities which help to get the IP address of the server where the site is installed on the onion domain, as well as getting root access to our servers, followed by a database dump and onion domains.
In a “but wait…there’s more” infomercial moment, the developers are also offering awards for so-called “brilliant ideas” that further the ransomware’s operational capability and for doxing the affiliate program manager.
Doxing is when sensitive data and personal information of an individual is released to the public, what then tends to follow is abuse being directed at the know no longer anonymous individual.
The affiliate manager does not seem to be on the bad side of the developers but rather seems to be attempting to shore up their anonymity by seeing if anyone can discover their identity.
The individual is confident they have done their utmost to hide their identity as they are offering 1,000,000 USD as a reward. For those keen to take up the challenge that adding a criminal organization and receiving funds in exchange for services are illegal in a great many countries.
ZCash Options and New Extortion Tactics
The making of ZCash payment options should not come as a surprise seeing that authorities have proven capable of seizing Bitcoin from user wallets.
Monero the other favored cryptocurrency used by ransomware operators, while boasts more privacy features, is often not listed on exchanges, particularly those in the US.
ZCash offers a similar privacy feature making it harder to trace but is currently listed on some US exchanges including Coinbase.
However, if authorities see a spike in ZCash usage related to the criminal activity they will request exchanges to delist the cryptocurrency so it is currently unclear how long ZCash could be an effective payment option.
According to a French cybersecurity publication, LeMagIT's Valery Marchive, the LockBit 3.0 operation is utilizing a new extortion model, allowing threat actors to buy data stolen during attacks.
One of the JavaScript files used by the new LockBit 3.0 data leak site shows a new HTML modal dialog that allows people to purchase data leaked on the site.
At the time of writing there appears to be no victims and the writer is unsure how this new tactic will be implemented once data is published.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion