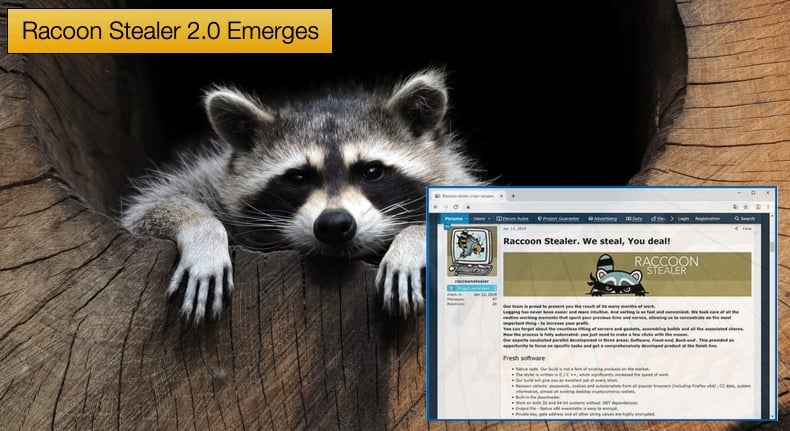
Racoon Stealer 2.0 Emerges
The last time Racoon Stealer made headlines was when its developers announced that they were ceasing operations following the war in Ukraine, more on this below. The last time this publication covered the malware was when its developers added features to target cryptocurrency wallets. Now, Racoon Stealer has emerged again with a completely new version built from the ground up in written in C/C++. Racoon Stealer 2.0 has officially emerged from dark web forums to steal your passwords.
In a recent series of blog posts security firm Sekoia detailed its reemergence and provided a detailed technical analysis of the new version.
The first part of the series describes the new versions announcement and subsequent new feature set while the second part goes into the technical aspects of the new malware.
Many of the more technical aspects of the malware will not be covered in this article so it is highly recommended that those interested in the nits and bolts of the malware read Sekoia’s technical analysis.
Returning to 2021 briefly, Racoon Stealer was one of the most popular malware-as-a-service offerings to cybercriminals looking to steal passwords, cryptocurrency, and other sensitive information we store on our computers.
Widely regarded as feature-rich, easy-to-use, and easily customizable the trojan with advanced spyware features proved to be a popular choice amongst cybercriminals. Version 1.0’s favored delivery method was through fake installers and cracker versions of popular software suites.
This popularity all came to a sudden stop following the outbreak of the Ukraine war when one of the malware’s admins made an announcement on a popular hacking forum, stating,
“Dear Clients, unfortunately, due to the "special operation", we will have to close our project Raccoon Stealer. The members of our team who are responsible for critical moments in the operation of the product are no longer with us. We are disappointed to close our project, further stable operation of the stealer is physically impossible.”
The announcement was followed by a further statement that those behind the malware were working on relaunching Racoon Stealer in the near future, to reiterate the admins said “don’t say goodbye forever” on several other forums as well. That near future has now become a reality.
On June 10, 2022, security researchers discovered servers hosting a webpage titled “Racoon Stealer 2.0.” Further analysis revealed several artifacts that linked this webpage to the original Racoon Stealer operation. SIx days later another security researcher came across what they believed to be a new malware sample.
This was later proved to be Racoon Stealer v2.0. Unfortunately, further analysis of this ample revealed that the new version of the malware was being distributed as early as mid-May in the wild. As for attributing the malware to Racoon Stealer’s malware developers researchers noted,
“Almost all the capabilities or technical details advertised by raccoonstealer, correspond to those observed during our malware analysis. Some properties of the malware are quite generic (collecting browser data and system information, capturing screenshot, encrypting the C2 address and strings) among the information stealing malware family, but others are rather specific and validate the attribution to Raccoon (sending data separately, the built-in file downloader, the file grabber going through all disks, and the specific loader).”
Feature Set and Attack Chain
Based on researcher analysis Racoon Stealer v2.0 shares many of the features of the previous version that made it so popular, including its focus on cryptocurrency wallets. In summary, the new version has the following feature set:
- Targeting of popular browsers (to steal passwords, cookies, auto forms, and credit cards);
- Targeting almost all desktop cryptocurrency wallets and extensions for cryptocurrency wallets (MetaMask, TronLink, BinanceChain, Ronin, Exodus, Atomic,
- JaxxLiberty, Binance, Coinomi, Electrum, Electrum-LTC, ElectronCash, etc.);
- File downloading;
- File loading (.cmd, .dll, .exe);
- File grabbing in all disks;
- Screenshot capturing;
- System fingerprinting;
- Installed application listing.
Researchers also provided a step-by-step attack chain seen in the wild of the new version. Researchers stated the chain is as follows:
- Dynamic Loading of DLLs;
- Run-Time Dynamic Linking of WinApi functions;
- Strings deobfuscation (base64 decoding and RC4 decryption);
- C2 server(s) deobfuscation;
- Checks (mutex, user privileges);
- Host fingerprint (MachineGuid, Username) and data exfiltration;
- Retrieving its configuration from its C2;
- Downloading, then loading the legitimate third-party DLLs;
- Fingerprint the infected host (CPU, RAM, OS version, Display info) and send this data to the C2;
- Collecting personal information and exfiltrating it (system information, browsers, crypto wallets);
- Capturing a screenshot and exfiltrating it;
- Removal of files created by the malware.
Given Racoon Stealer’s reputation amongst hackers, the use of the latest version can be expected to rise in the foreseeable future. Researchers believe future improvements will include a host of anti-analysis techniques and better code obfuscation.
Further, if v2.0 is to completely replace its older parent an increase in the criminal organizations infrastructure is to be expected so that users of the malware are not hampered in their information stealing by infrastructure growing pains. Upgrades to the malware to enable more efficient operations should be on security researcher radars.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion