Beware the Malicious Browser Extensions Targeting Millions
Browser extensions can be amazingly convenient applications in your browser. To-do lists, discount code auto-fill extensions, and numerous others add a high level of functionality to how we use our favorite browser, be it Chrome, Safari, Edge, or Firefox.
Sometimes this improved functionality and convenience can come at a cost as not all of them are designed to be helpful. Many are malicious and harmful. New research published by Kaspersky shows just how harmful an extension can be.
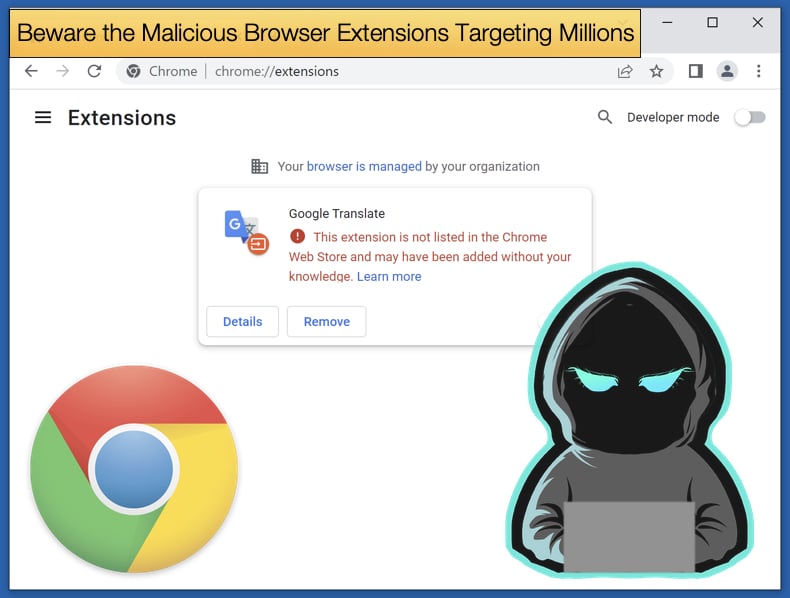
Despite being promoted as something helpful that has your best browsing interests at heart, an extension can be designed to steal credentials or redirect you to malicious adware.
This is still while the extension performs the helpful role it advertised as. This often makes it difficult for end users to determine whether the extension is malicious or not. In 2020, Google removed 106 malicious extensions from their Chrome Web Store.
Many of those removed were used to steal sensitive user data, such as cookies and passwords, and even take screenshots of pages visited by the now victim of the malware.
To make matters worse extensions were installed on corporate networks granting malicious actors sensitive data to organizations in the financial, energy, and defense sectors. In one instance an extension was discovered that could steal credit card and payment information entered by a victim.
Kaspersky shared their key findings noting that:
- Throughout the first half of this year, 1,311,557 users tried to download malicious or unwanted extensions at least once, which is more than 70 percent of the number of users affected by the same threat throughout the whole of last year.
- From January 2020 to June 2022, more than 4.3 million unique users were attacked by adware hiding in browser extensions, which is approximately 70 percent of all users affected by malicious and unwanted add-ons.
- The most common threat in the first half of 2022 was the WebSearch family of adware extensions, able to collect and analyze search queries and redirect users to affiliate links.
Kaspersky went on to note that the most common abuse of extensions resulted in the spread of malicious adware, that being unwanted software that promotes affiliates rather than any useful function.
The second most common threat encountered by Kaspersky was extensions that facilitate the installation of malware onto the victim's machine. The malware that is subsequently installed can steal data, credentials, and even log keypresses, known as keyloggers, to better steal sensitive information.
WebSearch
The most common malicious extension discovered by Kaspersky researchers is Websearch, which is a whole family of adware variants going by a variety of different names that seem to change hourly. Historically, this threat masquerades as tools for working with documents, such as DOC to PDF converters.
In reality, WebSearch extensions change the browser’s start page so that, instead of the familiar Chrome page, the user sees a minimalistic site consisting of a search engine and several links to third-party resources, such as AliExpress or Farfetch.
These links are affiliate links that earn affiliates money for clicks. The extension is no longer on the Chrome Web Store but can be downloaded from third-party websites. A favored distribution method is to bundle the extension along with pirated software or online streaming websites.
AddScript
Another malicious extension discovered by Kaspersky is AddScript. First discovered in 2019, it remains a popular tool for cybercriminals in 2022. Kaspersky’s data showed that 156,698 unique users encountered the malware in the first half of 2022.
Like with WebSearch the malicious aspects of the extension are bundled with potentially useful features. In AddScript’s case, the extension is advertised as a music downloader or video downloader that allows users to download content from social media profiles. As for the malicious side of the code, Kaspersky researchers noted,
“The malicious code is obfuscated. When the extension is running, it contacts a hardcoded URL to get the C&C server address. It then establishes a connection to the C&C server, receives malicious JavaScript from it, and runs it covertly. The only way the user can notice the execution of third-party instructions is by the increased consumption of processor power. The malicious script is updated from time to time and may perform various functions. For example, it can unobtrusively run videos on the victim’s computer, so that its owners profit from the video being “viewed.”
Other features included in the malicious side seen in the past include “cookie stuffers”, which insert an affiliate cookie when a website is visited. Kaspersky describes the process as,
“Traditionally, different brands promote affiliate products on their sites. When a visitor clicks the affiliate link, an affiliate cookie is saved on their device. If the user then makes a purchase on the partner’s page, the owner of the site that saved the affiliate cookie gets a commission. AddScript drops multiple affiliate cookies without the user clicking any links on any sites, in order to claim the commission for transactions that happen in the browser. Put simply, the fraudsters trick websites into thinking they have sent them traffic without actually doing so.”
In concluding, Kaspersky provided several recommendations for defending against malicious extensions. The first point made was to download extensions from trusted sources.
While some of the malicious extensions mentioned were briefly available by subverting Chrome’s security policies the important thing to remember is that Google has drastically improved detecting and remediating malicious extensions.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion