BianLian Ransomware Decryptor Released by Avast
On January 16, 2023, cybersecurity firm Avast announced that they had released a decryptor for the BianLian ransomware, not to be confused with the Android trojan of the same name. The decryptor can be used by the victims of the ransomware strain to recover encrypted files that can no longer be accessed by the user as they require an encryption key for access.
The tool comes after half a year of increased activity by those behind the ransomware and several high-profile attacks on victims.
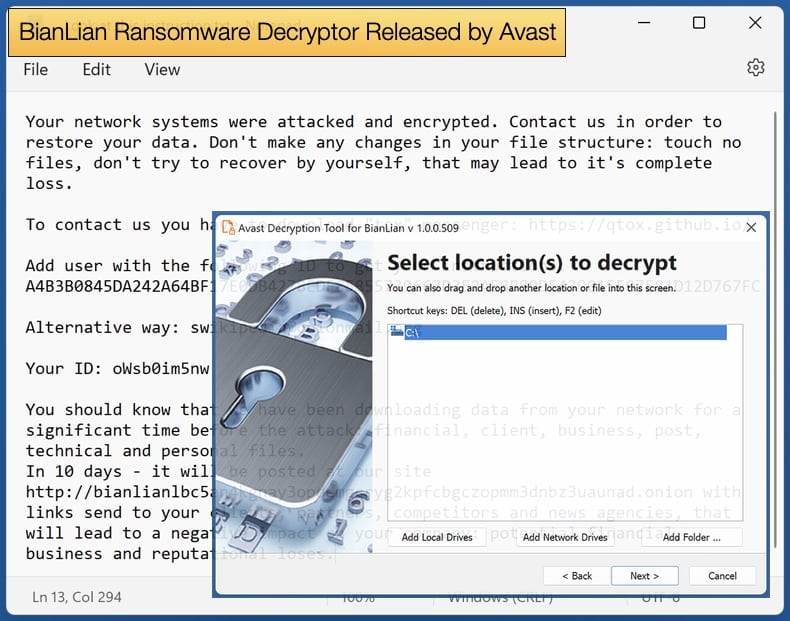
Further, the tool can also detect what version of the ransomware they have been infected with to make recovery operations easier, however, if the attackers are using the latest version of the ransomware there is little the decryptor can do.
As for the ransomware itself, Avast notes is written in the Go language and is a 64-bit Windows executable. This means that due to the language's structure strings are directly visible in the binary, including details about the directory structure of the author’s PC as well as references to asymmetric cryptography libraries in the sample.
Interestingly the malware itself doesn’t use the references to the RSA and elliptic curves mentioned in the code. Rather, the ransomware encrypts data with AES-256 in cipher block chaining (CBC) mode. The length of the encrypted data is aligned to 16 bytes, as required by the AES CBC cipher. As for the encryption behavior Avast researchers noted,
“Upon its execution, BianLian searches all available disk drives (from A: to Z:). For all found drives, it searches all files and encrypts all whose file extension matches one of the 1013 extensions hardcoded in the ransomware binary. Interestingly enough, the ransomware doesn’t encrypt the file from the start nor does it encrypt a file to the end. Instead, there is a fixed file offset hardcoded in the binary from which the encryption proceeds. The offset differs per sample, but none of the known samples encrypts data from the start of the file.”
By August 2022, it was reported that ransomware’s leak site had 23 victims listed. The list included several well-known companies from the United States, Australia, and the United Kingdom. At the time security researchers from BlackBerry concluded that BianLian was a relatively new threat actor that targets a wide range of industries.
The targeting of multiple industries possibly means that the group is financially motivated. This means that they will continue their efforts to exploit systems and networks they gain access to with the financial goal of extortion in mind. Their Golang-based ransomware utilizes several “goroutines”, which is a function that executes simultaneously with other goroutines in a program to improve performance.
The encryption routine is fast as files are encrypted in chunks. Their deployment method is manual infiltration of the system, and they use living-off-the-land (LotL) binaries to explore the networks and systems themselves. Once they find all the information they want, they deploy their ransomware, then begin the process of attempting to extort the victim.
MegaCortex Ransomware Decryptor Released by Bitdefender
BianLian was not the only ransomware recently to receive a free decryptor to help victims recover data. In early January Bitdefender, in conjunction with NoMoreRansom project, announced that it had released a free decryptor for the MegaCortex ransomware variant.
MegaCortex has not been in many headlines recently as in October 2021, Europol announced the arrest of 12 individuals linked to MegaCortex operations. Europol summarized the tactics of the individuals arrested as follows,
“The targeted suspects all had different roles in these professional, highly organised criminal organisations. Some of these criminals were dealing with the penetration effort, using multiple mechanisms to compromise IT networks, including brute force attacks, SQL injections, stolen credentials and phishing emails with malicious attachments…Once on the network, some of these cyber actors would focus on moving laterally, deploying malware such as Trickbot, or post-exploitation frameworks such as Cobalt Strike or PowerShell Empire, to stay undetected and gain further access…The criminals would then lay undetected in the compromised systems, sometimes for months, probing for more weaknesses in the IT networks before moving on to monetising the infection by deploying a ransomware. These cyber actors are known to have deployed LockerGoga, MegaCortex and Dharma ransomware, among others.”
The above quote reads like the current textbook attack for ransomware operators. Even if MegaCortex activity has dropped off it does not mean that victims who refused to pay the ransom could decrypt their files. With the new free decryptor, it is hoped that those who still cannot access important data as a result of a MegaCortex attack now can.
Bitdefender has made tried to make the process as easy as possible and for those who attempted to decrypt their files previously with mixed success, the new decryptor offers an advanced setting to replace them with clean files to further assist victims.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion