Improved Vawtrak Trojan Spotted in the Wild
Last year this blog reported on a dangerous banking Trojan known as Vawtrak. Originally discovered by researchers at Trend Micro, Vawtrak works by targeting a feature of Windows known as Software Restriction Policies (SRP). Essentially, SRP prevents infected systems from running programs specified by the creators of malware. In the case of Vawtrak, blocked programs include over 53 antivirus and security programs including products from Trend Micro, AVG, ESET, Symantec, Intel, and Microsoft. The idea is simple: by disarming local security features found on most PCs, Vawtrak is able to perform its primary task – stealing online banking credentials – without so much as a peep from the operating system.
Victims usually never have any clue that the machine is infected until their bank accounts are suddenly drained of money and they are left with little in the way of recovery options because the transaction appears to be a legitimate wire transfer to a bank located off-shore (usually in Russia or the Ukraine). Vawtrak was dangerous enough when first reported last year as it is often used in conjunction with Rovnix; another powerful malware variant that leverages the Windows PowerShell command shell.
Recent versions of the malware have gone even further by combining Rovnix, Vawtrak, and macros for Microsoft Word to spread the malware even faster and without detection.
Although the use of macros to spread malware is actually one of the oldest hacking tricks in the book, we have seen a recent increase in the techniques popularity as hackers look for ways to circumvent improved network security measures. If a victim has macros enabled, malware is installed without any further user action and in the case of Vawtrak, this means that many popular antivirus products will stop working due to the way the malware manipulates the aforementioned Windows SRP. This makes it extremely difficult to detect or remove Vawtrak once installation has been completed successfully.
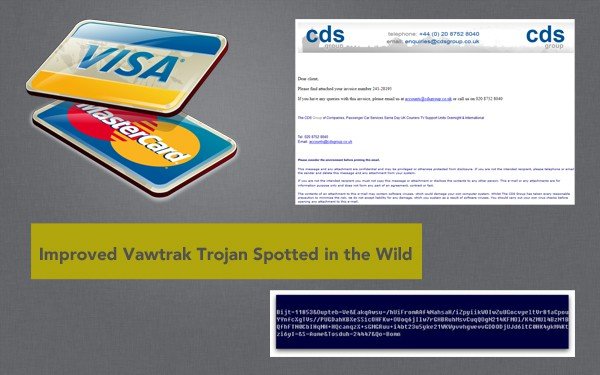
Macros aren’t the only way Vawtrak is being spread. A UK-based security firm recently spotted Vawtrak bundled in a spam email entitled “Invoice” which ultimately leads victims to a malicious website hosting the Blackhole exploit kit – one of the most powerful drive-by downloaders currently used by hackers. Other delivery methods include spam emails notifying recipients of a package delivery and Vawtrak has even been discovered tucked within pirated software downloads frequented by users of popular torrent downloading services. The point is that to protect yourself from Vawtrak, the best course of action is not to become overly focused on what the delivery method might be.
Rather, security experts agree that ensuring macros are disabled in Microsoft Office products and refraining from clicking on suspicious links embedded within suspicious emails are the best ways to avoid infection from this dangerous malware variant that is capable of draining your financial accounts in no time at all.
As always, ensure that all Windows OS and third-party application updates (especially those pertaining to antivirus and security products) are installed regularly. Also, make sure that Web plugins such as Flash and Java are disabled if not explicitly needed as these are the most common ways hackers perform drive-by download attacks when victims visit compromised websites.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion