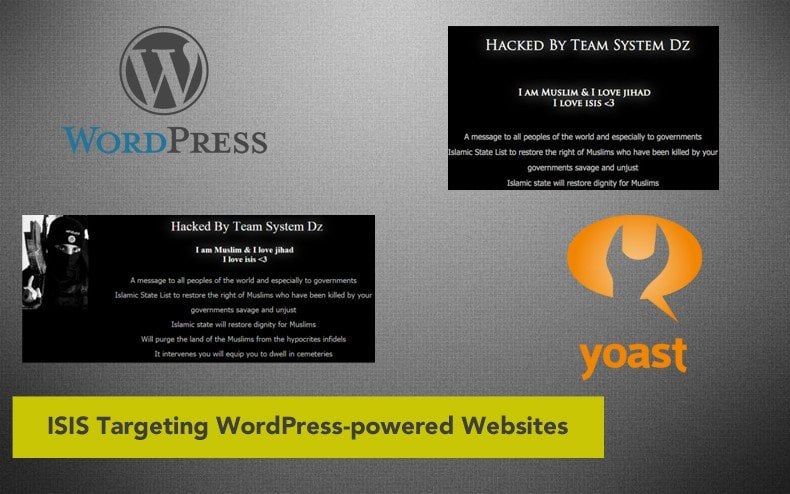
ISIS Targeting WordPress-powered Websites
The FBI recently released a warning to all WordPress users detailing a plot by terrorist organization ISIS to exploit vulnerable sites to display pro-ISIS messages. According to the FBI report, ISIS and its many sympathizers around the world are targeting WordPress sites – especially those operated by commercial entities, news organizations, religious institutions, and all levels of government (both foreign and domestic). So far, it appears that the individuals behind these attacks are not professional hackers. In other words, these are unskilled computer users that are leveraging known WordPress plugin flaws in readily-available hacking tools.
While most of these known vulnerabilities have already been patched by the WordPress developers, the responsibility of actually installing these updates falls on the webmasters operating the websites. If these vulnerabilities have not been patched on the server hosting the WordPress site, it is easy for even a non-skilled hacker to compromise the site and display pro-ISIS messages in lieu of the normal webpage content. WordPress originally started as an open-source blogging platform but has quickly evolved to accommodate all types of personal and commercial use websites.
A compromised WordPress site could provide hackers with all sorts of sensitive information; both about the business and its customer base.
This, in addition to the often derogatory pro-ISIS messages that have been popping up on affected homepages around the world. Most of the flaws in popular WordPress plugins (most recently the SEO by Yoast plugin – a plugin that has become a ‘standard’ tool for webmasters relying on the WordPress CMS) allow hackers to gain unauthorized access to backend infrastructure, inject scripts, steal cookies, and bypass security restrictions.
Once access is gained, the hacker is capable of creating new accounts with full user privileges and tamper with existing data. In addition to targeting existing WordPress-powered websites, pro-ISIS hackers are creating fake government websites in an attempt to trick users into providing personally identifying information – a tactic that ultimately leads to identity theft. Using Black Hat SEO techniques, many of these fraudulent websites appear at the top of search engine query results – making the site appear legitimate and attracting more victims than other phishing scams.
If you currently operate a WordPress-powered website (personal or business), the most important thing you can do to protect your website and your online reputation is to ensure that all WordPress plugins have been updated with the latest security patches.
This can typically be accomplished through the WordPress admin panel, although in some cases, plugins that come pre-installed with premium WordPress themes require a theme update before the patch can be installed. This happened recently with the Revolution Slider plugin, a dynamic home page slider that comes pre-installed with hundreds of premium WordPress themes. If you gave any doubt about updates provided by your WordPress theme developer, contact the company directly for more information to ensure your plugins all contain the latest security updates.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion