News Archive March 2014
Monthly Cyber Security News Archive: March 2014 Summary
Table of contents:
- A New Virus that spreads like the Common Cold
- Powerful Malware Updated with a New Set of Tricks
- Yahoo! Still Hasn’t Turned on Encryption for Instant Messaging
- Is the Russian Government Creating Malware?
- Smucker’s Hacked by Zeus-like Malware
- Spam Facebook Link Piggybacking on the Missing Malaysia Airlines Aircraft
A New Virus that spreads like the Common Cold
03.03.14
One of the good things about viruses is that they are reasonably easy to prevent by following some basic Internet/email best practices such as not downloading unfamiliar files and staying away from sites that may be compromised. Sure…this is sometimes easier said than done, but with a decent antivirus solution installed, most major threats can be stopped before they become serious. That all changes with the introduction of Chameleon. British researchers have created a computer virus that actually spreads through the air like a common cold. These researchers, from the University of Liverpool, have created malware that can jump from network to network using Wi-Fi access points. The speed that Chameleon can spread is something that is simply unheard of in the malware world and in the wrong hands, could represent a serious threat capable of hopping between homes and businesses in the blink of an eye.
In addition to spreading via Wi-Fi, Chameleon is even more dangerous because it is specifically designed to avoid detection (especially from software firewalls) and can even identify weak wireless networks that are extremely easy to exploit. The news of this new type of malware is scary to say the least. Until this proof-of-concept was created, it was long believed that a virus could not directly attack a Wi-Fi network; especially not autonomously. In a laboratory simulation, Chameleon was able to infect much of Belfast and London by jumping from wireless network to wireless network; focusing specifically on unsecured networks such as those found in airports and coffee shops.
Current antivirus programs are designed to look for malware on a physical device or on the Internet, but since Chameleon stays within the Wi-Fi network, it went completely undetected during the simulation.
While the simulation proved that Chameleon had trouble accessing secure wireless networks, the fact remains that many people do not understand the importance of IT security in the home or the office.

There are literally millions of public access networks that could be infected by Chameleon or a variant and many people use these networks to conduct personal and financial transactions. An infected network could easily transmit the compromised session data to a hacker on the other side of the world. Although this malware version was created in a lab and is unlikely to plague wireless networks for malicious purposes, the fact that the concept has been proven is a serious concern to security professionals around the world. Unlike “normal” viruses, a Wi-Fi based virus could theoretically spread across the globe in a matter of days; an alarming thought to say the least. It almost goes without saying, but assume that hackers worldwide are now working on a way to create a similar virus for malicious purposes.
The only way to secure your network right now is to ensure the router firmware is updated and secure passwords are implemented for network access and administrative access.
As this technology develops, antivirus manufacturers will likely find a way to detect this dangerous new threat, but as of now, a virus like Chameleon could spread like wildfire in no time at all.
Powerful Malware Updated with a New Set of Tricks
05.03.14
If you have been reading this blog for any time at all, undoubtedly you are familiar with Zeus (sometimes also known as Zbot) and it’s more dangerous derivative Citadel – which appeared online after the original Zeus code was leaked. These two malware variants are responsible for millions of dollars in online bank fraud and were specifically designed to avoid detection for most popular antivirus suites. Although much of the popularity of these two malware variants has receded within the hacking community recently, another variant known as the Gameover bot has become extremely popular. This malware variant is sometimes known as Zeus P2P because it relies heavily on peer to peer network conductivity for command and control. What makes Gameover so popular is that it has been based on the “tried-and-true” methods that initially made both Zeus and Citadel so dangerous.
The increased popularity of this malware bot has led hackers to try new techniques to maximize the effectiveness of the malware in a variety of IT environments. Most recently, hackers attempted to target logged in users of the cloud-based CRM Salesforce.com; a popular Software-as-a-Service (SaaS) solution used by sales professionals around the world. In their attempt to access session information from this site, hackers developed a kernel-mode rootkit which makes Gameover one of the most dangerous Zeus-variants to date. The code for this new rootkit is derived from another family of malware known as Necurs. While a rootkit was included in the initial release of Zeus, version 2 removed the user mode rootkit because it was ineffective in most attacks. By using the Necurs rootkit with Gameover, the developers are able to protect the malware files on disk and in memory. This makes Gameover difficult to detect and remove once activated on a system.
The current version of Gameover is distributed via spam email messages that contain fake invoices. When a user opens the email and ultimately the email attachment, a binary large object, or BLOB, is downloaded.
This BLOB is actually an obfuscated version of Gameover complete with a downloader that unscrambles and installs Gameover instantly. At this point, the previous version of Gameover would normally embed itself within Windows processes before exiting the installer.
Geographic distribution of ZeuS P2P network:
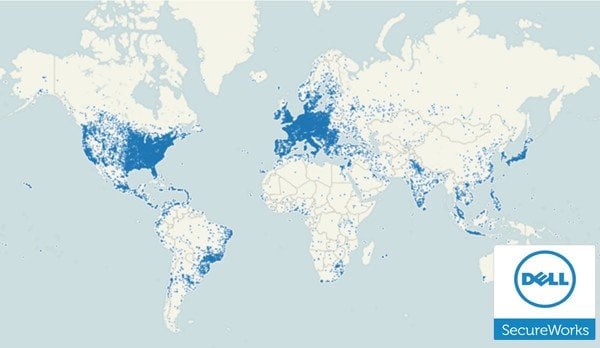
The new variant, however, drops and installs the Necurs rootkit as a kernel driver. The current version of Gameover installs both a 32-bit and 64-bit kernel driver. On 32-bit systems where the current user does not have Administrator privileges, Gameover attempts to use an old vulnerability (CVE-2010-4398) to elevate its session privilege and install the driver. If the vulnerability does not work, the user is prompted with a User Account Control prompt which should be a signal to most users that something isn’t right. 64-bit systems do not accept drivers without verified certificates, but Gameover tries to access the Boot Configuration Editor to change this setting prior to loading the driver.
Obviously, this new variant is much more dangerous than previous versions based on Zeus and if the rootkit is installed successfully, it is often impossible to remove without completely reformatting the Windows OS.
Failure to remove Gameover from an infected machine could result in stolen login credentials for online bank and credit accounts. As usual, do not download unsolicited attachments and never grant User Account Control access to programs you have not deliberately installed. Although it is not impossible to remove Gameover, the addition of a powerful rootkit makes it much more difficult and the loss of data to hackers is practically imminent.
Yahoo! Still Hasn’t Turned on Encryption for Instant Messaging
09.03.14
It’s been over nine months since Edward Snowden first revealed to the world the extent of government surveillance in everything Internet-related, yet some companies don’t seem too worried about the privacy of their users. Users of the popular Yahoo! Instant messaging service are vulnerable to government snooping and even malicious hackers on the same Wi-Fi network because the free service refuses to turn on encryption for the messaging service. What makes this even worse is that the lack of encryption was first discovered approximately 10 years ago and still has not been fixed (as per a CNET test conducted last week). Last week, an article reported that government agencies have been eavesdropping on Yahoo’s unencrypted video chats as well.
The article also describes a surveillance system known as “Optic Nerve” that has been responsible for intercepting and storing webcam images of millions of Internet users not suspected of wrong doing or on any known terrorist watch lists. While much of this information comes directly from reports released by Edward Snowden, it is no secret that Yahoo has failed to implement SSL technology into its instant/video messaging services despite pressure from users. Both Google and Microsoft have adopted SSL encryption (which scrambles information before its transmitted).
When used properly, SSL encryption is powerful enough that even the NSA shouldn’t be able to break the code; however, theories abound that the NSA has secret super computers capable of cracking traditional SSL encryption in a matter of minutes.
Yahoo just recently turned on HTTPS encryption for its webmail service by default last month despite pressure from security organizations to make this change years ago. It’s also worth noting that the protocols used for Yahoo’s encryption algorithm are older and have known vulnerabilities, but at least it’s a start. Yahoo CEO Marissa Meyer has pledged that Yahoo will offer users the option of encrypting all data to and from Yahoo servers by the end of Q1 2014 (a date which is fast approaching); however, Meyer failed to state that the encryption would be turned on by default.
Google and Skype, on the other hand, implemented encryption by default years ago. Yahoo has also failed to incorporate forward secrecy, a protocol that offers additional protection from government snoops (Google and Twitter both support forward secrecy).
Sadly, a story in the Washington Post late last year reported that the NSA’s Special Source Operations branch collected more email address books from Yahoo than from all other email providers combined.
The blatant lack of concern demonstrated by Yahoo executives when it comes to the security of end users from government intrusion and hacking activity should be a good enough reason for most people to stop using the service altogether. After all, there are many other options available that offer much better security without any fees. If you currently use Yahoo! Mail and instant messaging services, it is recommended that you migrate to Google or another email provider with a track record of security before your personal information falls into the wrong hands.
Is the Russian Government Creating Malware?
13.03.14
For many years, Russia has been home to many notorious underground cybercrime scandals and it seems that many of the dangerous breaches reported on this blog are at least tied to Russia somehow (even if they don’t necessarily originate there). A German security and antivirus detection firm known as G Data Security has uncovered data that seems to implicate the Russian government is behind the creation of a dangerous new malware variant known as Uroburos. Although G Data Security cannot definitively point a finger at the Russian government, there is ample evidence that certainly suggests Russian government involvement. The overall complexity of the malware, the presence of Cyrillic words within the source code, filename conventions, encryption keys and the overall behavior of the program all suggest the Russian government is involved in the creation of Uroburos.
Another key component of Uroburos that suggests Russian government involvement is that the malware checks for the presence of Agent.BTZ and remains inactive if this older malware version is installed. Agent.BTZ is an extremely damaging malware with Russian ties that was responsible for a severe attack against the Pentagon in 2008. Uroburos is a root kit comprised of two files including a driver and an encrypted virtual file system. The driver component of the malware is extremely complex and is specifically designed to avoid detection by even the most complex operating systems.
Among other things, Uroburos is capable of taking over an infected computer, executing arbitrary commands and hiding system activities.
It is considered a very flexible and modular malware variant because new malicious functions can be added very easily. Widely considered to be one of the most advanced root kits ever released, Uroburos is designed to work effectively against both x86 and x64 Windows computers. Based on test done in a sandboxed environment, it appears that the malware commands an infected computer to infect other networked computers even if those other computers do not have a direct Internet connection.
Once the malware has collected its assigned data it uses the same “hopping” method until it finds an infected machine with an Internet connection to transmit data back to its creators.
While it may seem alarming that the Russian government could be involved with the creation and deployment of this malware, remember that other countries (including the United States) have committed similar acts in recent years.
The Stuxnet worm was a government-sourced malware program designed to target specific software used to control nuclear facilities and it is widely believed that the United States and Israel worked together to create and distribute Stuxnet. Unfortunately, it appears that shadowy hackers hiding in remote parts of the world are not the only concern PC users have anymore. Although Russia has not confirmed or denied their involvement in the creation of Uroburos, the mere thought of large and powerful governments deploying malware around the world is a scary thought to say the least.
Smucker’s Hacked by Zeus-like Malware
18.03.14
The popular jam and jelly maker Smucker’s began notifying visitors that the website has been temporarily shut down because of a security breach that may have jeopardized customers’ personal financial information. While Zeus and other banking Trojans are designed to steal data from infected PCs, the information provided by Smucker’s about this breach states that the malware was actually designed to steal data from Web server applications. In case you are not familiar with banking Trojans, they typically operate by siphoning information using two techniques. First, these malware variants can snarf passwords stored in the browser cache. Also, banking Trojans use a technique known as “form grabbing” – which refers to the capturing of data entered into a form field within the web browser before it has been encrypted by the SSL session.
The malware that affected the Smucker’s website works very similarly; however, it works by infiltrating outdated web application platforms such as ColdFusion (an Adobe Systems product). This latest attack was able to capture form data submitted by visitors to the Smucker’s website including names, addresses, phone numbers, credit card numbers and card verification codes as customers were entering data in the online shopping cart.
While most of the malware variants covered on this blog focus on PC infection at the end user level, this exploit should serve as a reminder that even if you do everything “right” in terms of Internet security, your information may still be at risk if companies continue to use outdated, vulnerable web applications.
Malware like Zeus relies on capturing data prior to encryption by the web session, but this string of attacks (which also affected a large credit card processor based in Georgia) extracts sensitive information after had it has been decrypted on the server side of the SSL session. What’s especially unfortunate about the Smucker’s breach is that it was one of several websites that were publicly named as vulnerable after serious flaws were found in the ColdFusion web application platform.
In fact, this blog covered a story last year where Adobe Systems itself lost financial information for millions of customers enrolled in cloud-based software solutions including the popular Creative Cloud service. During the same breach, source code for some of Adobe’s top-selling software including Adobe Reader, Acrobat, Photoshop and ColdFusion were also stolen.
Apparently, this breach began sometime last year but Smucker’s only became aware of the problem late last month. Security experts have uncovered the control panel for a ColdFusion botnet that was built last year and is still being maintained by a group of hackers that has yet to be caught despite the FBI’s best efforts dating back to February of last year.
This botnet is responsible for the Smucker’s breach as well as a multitude of other websites worldwide. Again, attacks like this should serve as a reminder that despite your best computer security efforts, your information may still fall into the wrong hands. As a result, using alternative payment methods (such as PayPal or even crypto currency) is always a good idea. One time use credit card numbers for online purchases will also thwart identity theft in instances where the Web server has been compromised. Hopefully, companies are beginning to realize the importance of network security as the number of hacked websites continues in an upward spiral that doesn’t seem to be slowing any time in the near future.
Spam Facebook Link Piggybacking on the Missing Malaysia Airlines Aircraft
24.03.14
Hackers have traditionally used “hot” news stories as a way to trick unsuspecting people into clicking on fake emails with varied malicious intents. Many of these links take users to phishing pages or to exploited links full of drive-by downloads and other malware. One of the biggest stories around the world right now is Malaysia Airlines Flight MH370. For those who are unfamiliar with the story, a large commercial aircraft disappeared from radar and has yet to be recovered. The story is even more intriguing because experts are now reporting that the plane was apparently hijacked and flew for up to six hours in an unknown direction before seemingly disappearing from the face of the Earth. The popularity of this news story on both conventional and social media outlets has provided a perfect topic for hackers to focus on and so far, thousands of people have already been tricked as a result of this email scam.
The scam is actually a message circulating via Facebook that the missing Malaysia Airlines flight has been located in the Bermuda Triangle. The link also claims that the passengers are all alive and even includes pictures of a large airliner floating in the ocean as “proof” that the plane really has been located.
The fake message invites users to click on a link to view “breaking news footage” of the discovery of the crash site. Unfortunately, the actual plane has not been discovered yet despite thousands of people searching around the clock for the wreckage.
The images shown in the link are actually from an unrelated crash of a Lion Air flight that landed in the sea while heading for Bali in April of last year. In that crash, all passengers did survive so the images look real enough for many Facebook users to click on the link for more information. When a user clicks on the link, they are first taken to a fake Facebook page that forces them to share the message with Facebook friends before continuing. This step ensures that the scam continues to spread across social media at an alarming rate. After sharing the link as requested, users are redirected to another fake page that supposedly hosts the video. At this time, users are prompted to participate in an online survey or offer as a way of “proving that they are human.” Like so many other survey scams, it doesn’t matter how many surveys or offers the user completes – they never get to see the illusive video.

Instead, the surveys often ask for users’ cell phone numbers. Unfortunately, the small print at the bottom of the page that most people don’t notice states that by providing a phone number, users are actually signing up for a very expensive premium SMS subscription service.
Every time this service sends a text to the victim, that person’s cellular service is charged a large sum of money (as much as $10 per text).
These costs are passed directly on to the customer during their next billing cycle and can get very expensive quickly. Other surveys ask for other personal information that could result in targeted spam email campaigns and even telemarketing calls. The problem with this scam is two-fold.
First, it is very unfortunate that some people are willing to capitalize on tragedies such as the missing Malaysia Airlines flight. Second, many of these tactics are not actually illegal assuming the people responsible state somewhere what their intentions are.
Certainly, it represents the epitome of unscrupulous business practices, but most of the people behind these scams never face prosecution for their swindling tactics. The moral of story: Malaysia Airline Flight MH370 has not been found as of this writing and any links claiming that it has been found are fake and could result in financial loss or at the very least, some annoying emails and phone calls.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion