Hacked Wireless Routers Being Used to Distribute Malware
Hackers often rely on compromised websites as a way to host and distribute malicious software via drive-by download attacks. A drive-by download uses an exploit kit to exploit known vulnerabilities in popular Web browser plugins including Java, Silverlight, and Adobe Flash. Recently, security researchers discovered a group of cybercriminals that have chosen to take a different path. By exploiting vulnerable wireless routers, these criminals have found a way to distribute the notorious Dyre malware strain without the need for compromised websites to deliver the payload. Dyre, which is also known as Dyreza and Battdil, is typically installed by a payload-carrying Trojan that modern antivirus software detects as “Upatre.”
Upatre is typically distributed by malicious spam email campaigns containing a link that directs victims to a website hosting a string of malicious JavaScript designed to install the malicious payload on the PC. In other cases, the spam email directs victims to a fake file – possibly a bank statement, invoice, or fax – that installs Upatre upon extraction. According to a recent report by security firm Symantec, Dyre is a complex malware variant that is capable of hijacking browser sessions in Internet Explorer, Firefox, and Chrome.
Once the browser session is successfully hacked, Dyre’s main purpose is to intercept Internet traffic between the infected PC and online banking sessions in an effort to harvest login credentials. Once captured, these login credentials are sent to the attackers and used to initiate fraudulent wire transfers from the compromised accounts.
In many cases, Dyre is also used to download additional malware to the victim’s PC and can even add infected PCs to a botnet designed to participate in mass spam email campaigns that perpetuate the threat. Researchers at the Fujitsu Security Operations Center in the UK recently began tracking a Upatre/Dyre campaign that is being served from hundreds of compromised wireless routers. Although there are many different types of routers being used as part of this campaign, most of the routers appear to be powered by MikroTik and Ubiquiti’s AirOS.
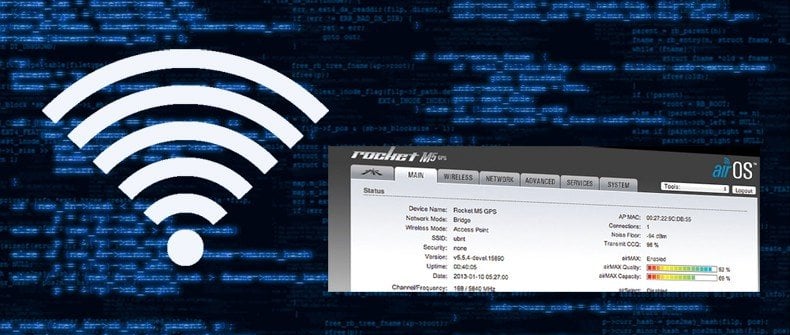
According to Bryan Campbell, a Threat Intelligence Analyst at Fujitsu, “We have seen literally hundreds of wireless access points, and routers connected in relation to this botnet, usually AirOS. The consistency in which the botnet is communicating with compromised routers in relation to both distribution and communication leads us to believe known vulnerabilities are being exploited in the firmware which allows this to occur.” Although it is difficult to pinpoint exactly why so many home wireless routers are implicated in this botnet, experts speculate that the hackers behind this campaign are simply exploiting routers with default login credentials. It’s also worth pointing out that most of the routers that have been verified as compromised have the telnet port (port 23) open. Telnet has been used as a backdoor into Windows systems since the introduction of the operating system 30 years ago. Some readers may recall that in January of this year, both Microsoft’s Xbox and Sony Playstation’s networks were knocked offline by an attack that relied on hacked routers. These routers were also compromised via remote telnet connections.
This proves that although unorthodox in today’s cybercriminal world, the use of hacked wireless routers is an effective way to spread malware campaigns without detection as these home routers are not equipped with intrusion detection systems and are usually managed by consumers without the forensic IT knowledge to diagnose a breach in the first place.
Although this campaign seems to focus mostly on Ubiquiti routers and the AirOS firmware, any router could be used to carry out this attack if it is left in a state that can be easily exploited by hackers. Primarily, this means ensuring that the default administrative login credentials have been changed (and adhere to secure password best practices). It also means ensuring the telnet port is closed and that remote administrative access is disabled unless absolutely needed by the router admin. To determine whether or not you have changed the default admin credentials (if you aren’t sure it means you probably haven’t changed them), go to www.routerpasswords.com to look up the make and model of your router.
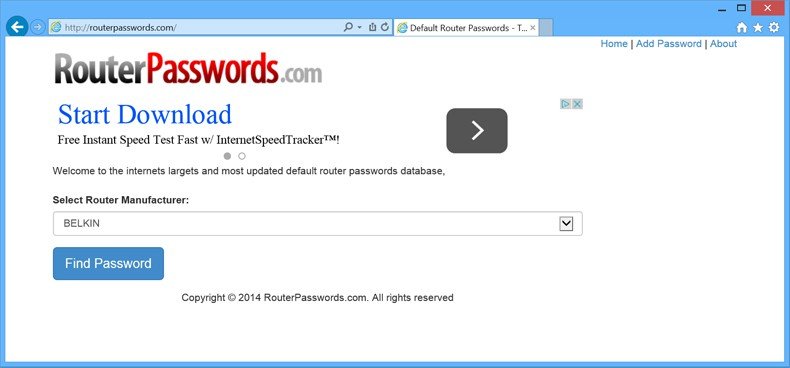
Once you have determined the default login credentials for your specific router, you must attempt to log into the router using these credentials. This is accomplished by opening a browser window and typing the LAN IP address for the router. In most cases, the default IP address of home wireless routers is 192.168.0.1, 192.168.1.1, or 192.168.1.2. When the correct IP address has been entered, a login prompt should appear asking for a username and password. Try to use the appropriate default credentials provided at the link above to login. If successful, the default credentials have not been changed and ultimately means that the router is susceptible to hacking by this group of cybercriminals to distribute Dyre and a multitude of other nefarious activities. Change these default values immediately to prevent hackers form accessing your home network.
It’s important to note that this threat still affects PCs in the end even though it relies on hacked home routers to distribute its payload instead of the more traditional compromised website attack. This means that to protect yourself from Dyre, the OS and all third party applications need to be regularly updated.
An appropriate antivirus solution should also be installed and the virus definitions must also be updated to protect against the latest malware signatures. Finally, ensure that all Web browser plugins not absolutely necessary to daily PC use are disabled or uninstalled completely as these are the primary means by which Upatre, and ultimately Dyre, infect PCs. Also remember to never open unsolicited email attachments or follow any links from emails that seem at all suspicious. In many cases, these emails are designed to appear as though they originate from legitimate websites but when a link is clicked, victims are redirected to a malicious server hosting Upatre.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion