GamaPOS More Dangerous than Ever Thanks to the Andromeda Botnet
As summer slowly comes to a close, retailers are already ramping up for their most profitable quarter of the year…the holiday shopping season. This is a notoriously busy time for cybercriminals looking to cash in on the large amounts of payment data sent across the Internet during this time of year but hackers aren’t waiting until the holidays to begin install POS malware in as many retail locations as possible; months before the shopping frenzy even begins. The notorious Andromeda botnet has been used for years to deliver malicious payloads across multiple industries and platforms. GamaPOS is one of the newest and most dangerous POS scraping malware variants in the wild. The problem with GamaPOS is that is has a low success rate when attempting to infect new systems because there are very few POS backdoors (not to mention that media coverage of major retail breaches over the last several months have put everyone on high alert).
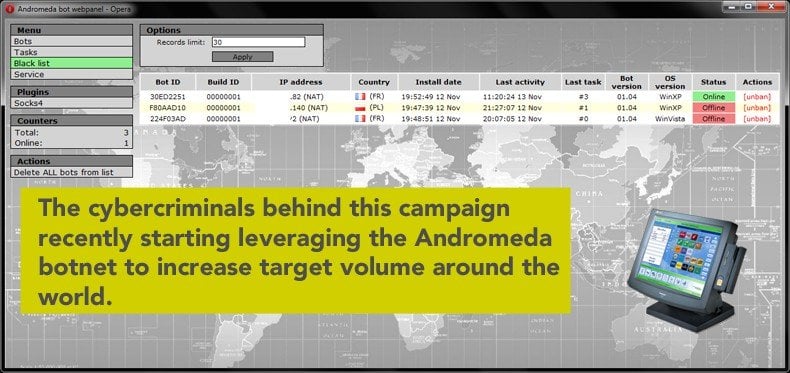
The cybercriminals behind this campaign recently started leveraging the Andromeda botnet to increase target volume around the world – subsequently increasing the number of reported infections in 13 U.S. states as well as in several other countries. Andromeda has been a long-term successful botnet campaign, mostly due to persistence. The botnet works by spamming large companies with emails that include bogus attachments. These attachments are typically meant to look like Payment Card Industry Data Security Standard (PCI DSS) compliance documentation although variations that appear to be updates for back-end office systems have also been spotted in the wild. Once an employee opens this bogus attachment, a series of malicious scripts automatically create a network backdoor. From that moment forth, the infected machine is part of the Andromeda botnet.
GamaPOS is a powerful piece of malware that scrapes the RAM of infected POS machines in search of payment card information that is subsequently uploaded to a command and control server controlled by the hackers behind the GamaPOS campaign.
As previously mentioned, GamaPOS’ weakness is in its low infection rate. This can be attributed to the significant rise in POS attacks over the last few years. Companies are now more focused on hardening the backdoors inherent to popular POS systems and for the most part, this security effort has been rather successful. As a result, hackers have been looking for new attack angles to infiltrate these systems–systems that could be worth millions of dollars in stolen payment credentials to the cybercriminals running the campaign. One of these angles is the coupling of Andromeda to GamaPOS as a way to reach more targets than GamaPOS could ever hope to on its own.

It’s worth noting that very few current POS systems are actually vulnerable to Andromeda. And according to Trend Micro, very few Andromeda-infected systems are also vulnerable to GamaPOS (slightly less than 4%). Even though this may make the GamaPOS/Andromeda threat seem less dangerous, the fact remains that businesses in California, Arizona, Florida, Colorado, and nine other states have already been infected by this combination. Infected systems have also been identified in Canada and a handful of other countries. The businesses affected by this threat so far range from pet care businesses to furniture sellers to credit unions. So although the percentage of systems that could potentially fall victim to this attack is relatively small, the results of an infection could be disastrous for businesses around the world in the coming months. This combination malware attack starts by leveraging networking tools such as PsExec and Mimikatz – tools designed to collect sensitive network data. If the collected data looks promising to the hackers, the GamaPOS malware is deployed in search of specific data associated with electronic payment information.
Primarily, GamaPOS looks for active processes involving Track 2 and the American Banking Association (ABA) credit card data. These file contain the credit card user’s account number, PIN, and other discretionary data that can be used to commit credit fraud.
Once located, this information is stored in a .txt file and uploaded to the hacker’s server for retrieval. Unlike many of the popular POS malware variants that have made headlines over the last several months, GamaPOS does not rely on the Luhn algorithm to validate credit card data. Instead, this malware variant filters the compromised data by comparing the first few numbers of the scraped card data to see if they match cards being targeted by the attackers. According to Trend Micro, GamaPOS shares many similarities to another POS malware variant known as NitLovePOS. Discovered by security firm FireEye in May, NitLovePOS also uses spam-based malware campaigns for distribution and the initial stage of the attack leverages the same IP block.
Also of note is that the powerful algorithms behind GamaPOS were written exclusively using Microsoft’s .NET platform. GamaPOS is the first malware ever detected that uses the .NET platform as its backbone but according to researchers from Trend Micro, it will not be the last. This claim is based on the fact that Microsoft recently announced that the .NET will be available as an open source platform, meaning that more developers will begin using .NET for proprietary application development projects. It also means more hackers will begin leveraging the platform to create new and powerful malware strains such as GamaPOS and NitLovePOS. The bottom line is that although this attack is certainly dangerous, the combination of GamaPOS and Andromeda requires two completely separate factors that don’t typically occur in POS systems. That said, any company currently running a POS backbone that is vulnerable to Andromeda should take note of GamaPOS as a serious threat that could be responsible for millions of dollars in stolen payment card data in the coming months.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion