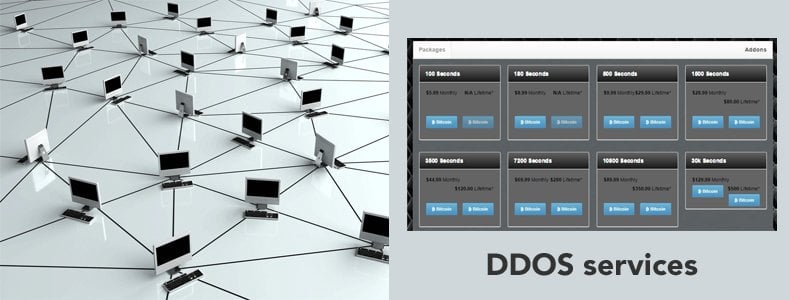
DDOS for Hire
You can hire hackers; you can hire DDOS services too. Why you would want to hire a DDOS service? It is difficult to say as only the criminal mind or otherwise deranged person would know why they would want to inflict damage for sport. Except some hacking is political in nature, in which case the motive is obvious, or even cyberwar such as the ISIS army and its enemies. Some DDOS service providers charge $38 for their botnet rental services. A botnet is a network of thousands of hacked computers. The weak spot here is the vast majority of internet users are ordinary people who do not know that they have been hacked and are unwitting accomplices in this. The reason someone would need to use a third party to launch this type of attack is you need as an attack from one or only a few IP addresses would be easy to shut down by the victim. Incapsula’s “2015 DDoS Threat Landscape” report tells us that that some attacks can last weeks or months. One Idaho kid shut down his school system’s computers for weeks and caused all the kids who took an aptitude test to lose their scores.
Perhaps the hacker lost his own score which would have been fitting punishment. One interesting thing they cite is that IoT devices are being used in some DDOS attacks. By definition there will be millions of those, more even eventually than internet human users. That could be an emerging security problem. Not all IoT device traffic is encrypted. And most use card computers like BLE Beacons or the Intel Edison running Linux, which, of course, has security problems, just like any other operating system does.
Lizard Squad’s Lizard Stresser
Brian Krebs reported that one too DDOS tool and service is Lizard Squad’s Lizard Stresser. It successfully brought down Microsoft and SONY gaming sites. It works using has hijacked routers around the world. That is possible when the router uses Linux, meaning it has an operating system that one can login to. The technical details of the explained are explained in this Russian to English translation.
Someone has bought up the domain now lizardstresser[dot]su or changed its DNS records as going there now redirects you to an options trading website. Kreb said the site is registered in Bosnia. But the MX and other DNS records all point to servers in Russia. Here is another explanation of the Linux.BackDoor.Fgt.1 virus.
Once the host is infected it looks for other hosts to infect by scanning the internet and then trying to log into routers with “admin/admin” or “root/12345” default passwords. It generates random addresses so it has no clever algorithm to detect working addresses, such as querying DNS registrars. It does not say how it uploads the virus to the router, but if you can get telnet access you can login and start the ftp service and upload it that way. Of course not all routers have a shell that you can login with telnet like the most popular home ones like most LinkSys models. Those only have firmware. Plus the OS would not be a scaled-down version of Linux that have some limitation on what a hacker might exploit.
The attackers also bought Google Cloud accounts with stolen credit cards. Their goal was to launch DDOS attacks from there, but Google shut them down. Google would not tell Brian Krebs how they spotted that. (Have you asked yourself why Google has apparently never suffered a major attack on its systems? I don’t mean a DDOS attack. I mean getting inside and stealing data. Whatever their security practices are they are the best practices. I wonder if they keep them secret as a way of not tipping off the hackers. Certainly other businesses could profit from what Google has learned.)
DDOS Defenses
Nothing can stop a DDOS attack. As far as elegance goes it’s not a very elegant way at all for a hacker to attack a system since it requires no original thinking. Yet some companies like Cloudflare offer DDOS services to keep your website working or perhaps limping along during an attack. They do this by changing your DNS records, if that is required (It would not be if you already use the Cloudflare CDN.) to route your traffic through their massive server farms. Then they apply whatever techniques they have to shut down malicious DDOS traffic. That would include not processing a DNS record that is obviously amplified nor malformed packets design to nothing but take up server time and shutting off sites that send a TCP ping with no response ACK acknowledgement.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion