The Story Behind Security Weaknesses in the Linux Kernel
There are two items on the internet that you need to see if you follow security. First there is this film on Youtube that gives the history of Linux. And then there is story in The Washington Post that explains that some people are concerned that the people who maintain the Linux kernel are not fixing security problems there. The procedure to fix bugs in the Linux kernel is so slow that the newspaper calls it “evolutionary.”
To understand the controversy, and to decide for yourself whether there are security problems with Linux, you have to look at the history of how it was developed and who maintains it now.
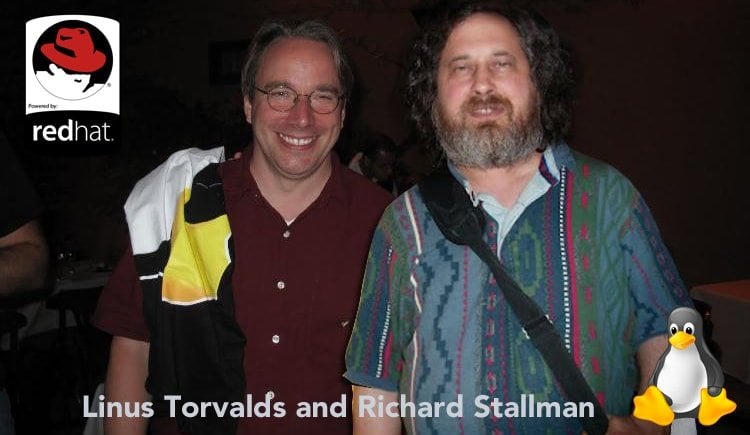
There are two people behind the Linux operating system: Richard Stallman and Linus Torvalds.
What Richard Stallman did was start the project to write the GNU operating system, which we now call Linux. He is annoyed that people do not call it by its correct name, GNU/Linux. But he is happy to have reached his overall goal, which to write something and give it away for free.
Richard Stallman started the GNU organization with the idea that no one should have to pay for Microsoft Windows or any version of UNIX, like Solaris. (AT&T invented UNIX but did not give it away or turn it into a commercial product.) Now lots of software is distributed under what is called the GNU license, meaning it is free if when you change that you are willing to give those changes away for free as well so they can be added back into the product.
Stallman and his team focused on writing everything in Linux except the kernel. They programmed the ls command, wrote Openoffice, built the GNOME desktop and all the other things that make Linux usable. But for whatever reason they did not write their own kernel. They must have done that one at one point, or it would not have been possible to start it on a PC. The kernel is the most important part. That is what make the hardware work with the operating system. It handles tasks like scheduling items in and out of memory and the CPU and writing data to disk. Stall turned to Linus Torvalds for that in large part to the elegance and simplicity of what he wrote.
Linus had written his own version of UNIX because doing that it interested him. He named it for himself then gave it away. Then he went looking for a way to make money off that, but ended up keeping it free and taking jobs from people who could help spread its adoption. Red Hat gave him some stock options, which gave him enough money to buy a house for cash.
Linus went to work for an organization that now has turned into the Linux Foundation. He oversees Linux kernel development there. There he has become a veritable god. Nothing gets into the Linux kernel without his approval. He has people close to him who take code submitted from thousands of programmers around the world and then pass on what they consider to be the necessary to Torvald for approval. Then the people who write Red Hat, Ubuntu, and so forth download the Linux kernel source code and add it to their source code when they build their version of Linux.
 As Linux has come to power everything from Debian, Ubuntu, Android, The New York Stock Exchange, medical devices, and lots more some people have been concerned that Linux has security problems that Linus has not fixed. Yet no one but Linus Torvald has any authority to do anything about it. If they went and wrote their own product they would be building something that is not supported by the worldwide community of Linux developers. That would be a huge responsibility.
As Linux has come to power everything from Debian, Ubuntu, Android, The New York Stock Exchange, medical devices, and lots more some people have been concerned that Linux has security problems that Linus has not fixed. Yet no one but Linus Torvald has any authority to do anything about it. If they went and wrote their own product they would be building something that is not supported by the worldwide community of Linux developers. That would be a huge responsibility.
This is where the controversy arises. Torvald does not distinguish between software bugs that just cause some kind of error and software bugs that expose a security weakness. His goal is to make sure that the software does not break, so he is very careful to introduce any change that would break what he calls user space, meaning the most basic functions.
Linus believes stability and performance are the most important items when considering what changes to make to the Linux kernel. You can see this sentiment when you look at Debian releases, which is the OS that powers most websites around the world. They have releases labelled stable and newest. Some of the Stable ones are quite old. So those might be missing drivers for the latest hardware, but they have been running for years, some of them without having ever been rebooted.
But this approach does not sit well with some people. For example, the NSA wrote their own version of Linux, with their own kernel, called SELinux, or secure Linux. Despite the NSA being an American spy agency they still gives away their software for free. (Most security like the RSA encryption algorithm, openssl, Tor, etc came from projects funded the US military. All of that is free.) Then there is GRSecurity.
The author of GRSecurity is particularly critical of the unwillingness of Linus Torvald to address security issues in Linux. So his version of Linux includes security hardening that he says should be in the official version of Linux. An example of that is memory address randomization. What that does is load shared libraries at random addresses in memory. Microsoft did that to try to keep hackers from hacking Windows. The idea is instead of loading, say, the subroutine that sends data to the network adaptor at address FFFF, store it at random places. Then a hacker cannot inject assembly language code into a web page and direct the browser to go to FFFF to load that or any subroutine that has a security weakness they can exploit. The hacker would have to search for that. Which they do. It’s called spraying.
When journalists, like The Washington Post, write about technical topics like this they should quote experts and not draw conclusions themselves. For example, they wrote:
“Versions of Linux have proved vulnerable to serious bugs in recent years. AshleyMadison.com, the Web site that facilitates extramarital affairs and suffered an embarrassing data breach in July, was reportedly running Linux on its servers, as do many companies.” But then they say something entirely different, and correct themselves too, “Those problems did not involve the kernel itself.”
That is the key question: whether there are security problems in the kernel or whether those are in the items that lie outside the kernel, like openssl or maybe a network or video driver. There have been some kernel bugs, including one found by the Italian firm The Hacking Team. They found a way to take over Android phones and turn on the camera and microphone. The Hacking Team is an espionage business who charges governments lots of money for their services.
Torvalds has been dismissive of security issues. He told the interviewer:
“The people who care most about this stuff are completely crazy. They are very black and white.”
You can imagine holding dominion over something as important for so long might make someone a little crazy. On occasion Linus Torvald has definitely flipped out. He has written emails like this:
“WE DO NOT BREAK USERSPACE! Seriously. How hard is this rule to understand? We particularly don’t break user space with TOTAL CRAP.”
So this is how the situation is today. The good news is that the Linux kernel is open source. So when someone finds a serious bug they can publicize that thus forcing the developers to it. If that takes too lot the developers of Red Hat and so forth can change it themselves and then add the official version when Torvald’s developers fix that.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion