AnalyserKey Adware (Mac)
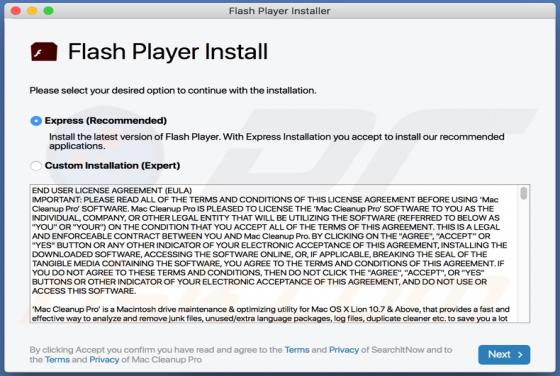
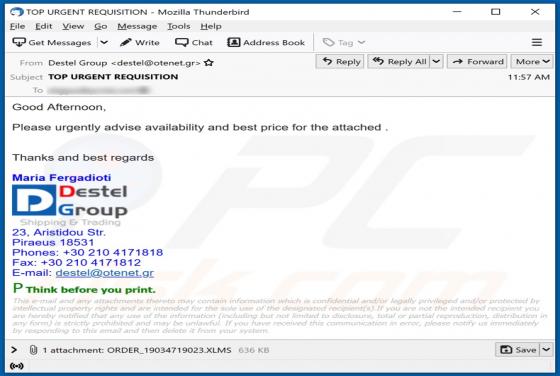
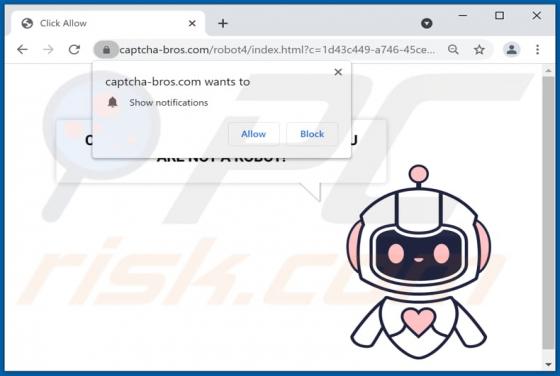
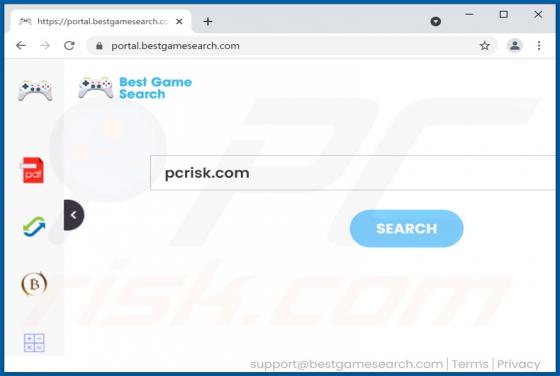
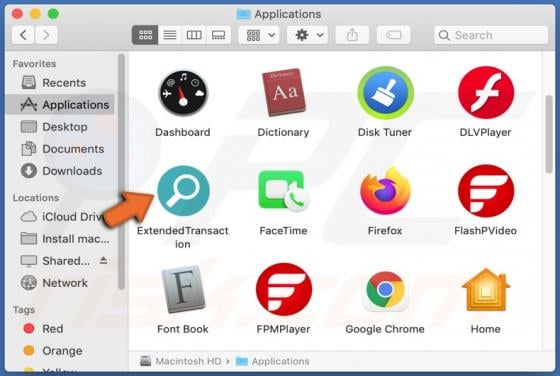
AnalyserKey is advertising-supported software - it generates advertisements. It also has the qualities of a browser hijacker - it changes a web browser's settings to promote a fake search engine. It is likely that AnalyserKey collects various information as well. Typically, users install adware-