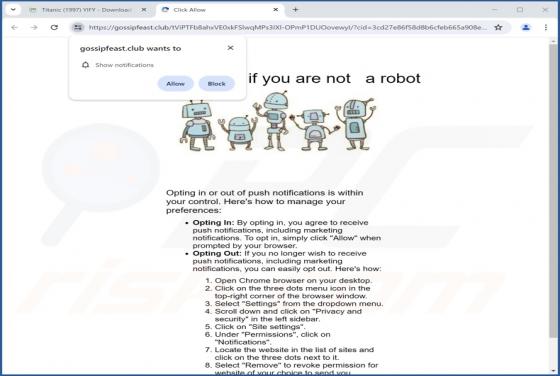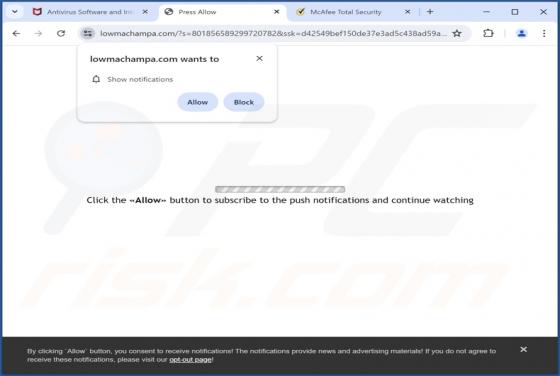
Lowmachampa.com Ads
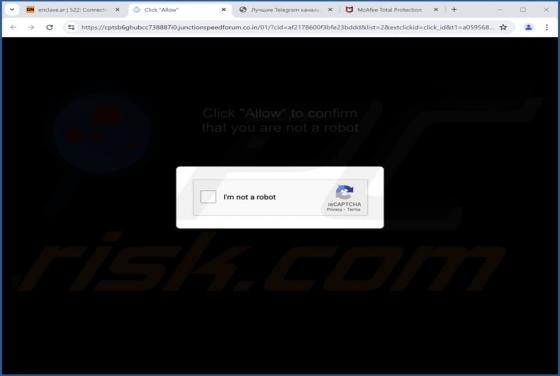
Lowmachampa[.]com is a rogue page that promotes browser notification spam and redirects to different (likely unreliable/hazardous) websites. Our researchers discovered this webpage while investigating suspicious sites. Most users access lowmachampa[.]com and websites akin to it through redirects