Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is Phoenix Worm?
Phoenix Worm is malware written in the Go programming language. It is designed to function as an initial-stage component in an infection chain. Its primary purpose is to quietly infiltrate a system, establish persistence, and prepare the system for the deployment of additional malware later. If detected, Phoenix Worm should be removed immediately.
Phoenix Worm overview
At first, Phoenix Worm connects an infected computer to a remote server controlled by threat actors. This connection (a command-and-control, or C2, server) allows the malware to receive instructions and send information back. Once it is active, it generates a unique ID for each infected device, allowing attackers to track and manage multiple victims.
It also collects basic information about the system (e.g., operating system version, hardware details, installed software, and network information) and sends it back to cybercriminals. Additionally, Phoenix Worm can be updated remotely and used to download or run additional malicious programs.
Cybercriminals can use Phoenix Worm to infect devices with different types of malware. Ransomware may be deployed to lock (encrypt) files and demand payment for decryption. Spyware can also be delivered to monitor activity and steal sensitive data such as passwords or messages. Information-stealing malware may target browser data, saved logins, or cryptocurrency wallet details.
Remote access trojans (RATs) can give attackers full control of the infected system, allowing them to operate it remotely. Thus, having a device infected with the Phoenix Worm can lead to various issues, including financial losses, account hijacking, identity theft, and reputational damage.
| Name | Phoenix Worm dropper |
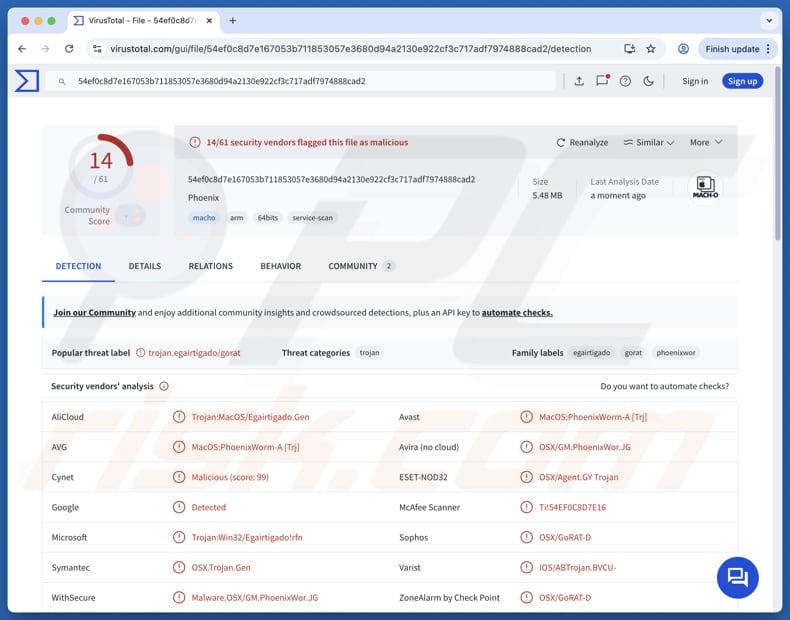
| Threat Type | Malware Dropper |
| Detection Names | Avast (MacOS:PhoenixWorm-A [Trj]), Cynet (Malicious (score: 99)), ESET-NOD32 (OSX/Agent.GY Trojan), Sophos (OSX/GoRAT-D), Symantec (OSX.Trojan.Gen), Full List (VirusTotal) |
| Symptoms | Droppers/loaders are designed to stealthily infiltrate the victim's computer and remain silent, and thus no particular symptoms are clearly visible on an infected machine. |
| Possible distribution methods | Infected email attachments, malicious online advertisements, social engineering, software vulnerabilities, software 'cracks'. |
| Damage | Additional infections (e.g., ransomware of spyware). |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Conclusion
Overall, Phoenix Worm is used by cybercriminals to infiltrate devices and add more malware later. It may be used as a component in malicious campaigns used to steal data, encrypt files, monitor devices, steal money, or for other malicious purposes. Thus, Phoenix Worm should be eliminated from infected devices immediately.
More examples of malware targeting macOS are MiniRAT, Overlord, and Infiniti.
How did malware infiltrate my computer?
Malware can be distributed through emails with malicious links or attachments, untrustworthy advertisements (e.g., fake warnings), tech support scams, or deceptive or compromised websites. Cybercriminals can also spread it through peer-to-peer sharing networks, infected USB drives, or by hiding it inside pirated software, cracks, and key generators.
In some cases, threat actors take advantage of unpatched or outdated programs to deliver malicious payloads. Malware is often hidden in infected documents, archives, scripts, or executables. Devices become infected when users open malicious files or take additional steps.
How to avoid malware?
Users should be careful with unexpected emails, especially if they come from unknown senders or include suspicious attachments or links. Applications should be downloaded only from trusted sources, such as official websites or well-known app stores. Using cracked software, pirated programs, or key generators should be avoided.
It is also important to keep the operating system and all installed software up to date and to avoid clicking on pop-ups, ads, or other content on dubious sites. Users should also refuse notification requests from sites that seem suspicious. If your computer is already infected, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate all threats.
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
Video showing how to remove adware and browser hijackers from a Mac computer:
Unwanted applications removal:
Remove potentially unwanted applications from your "Applications" folder:
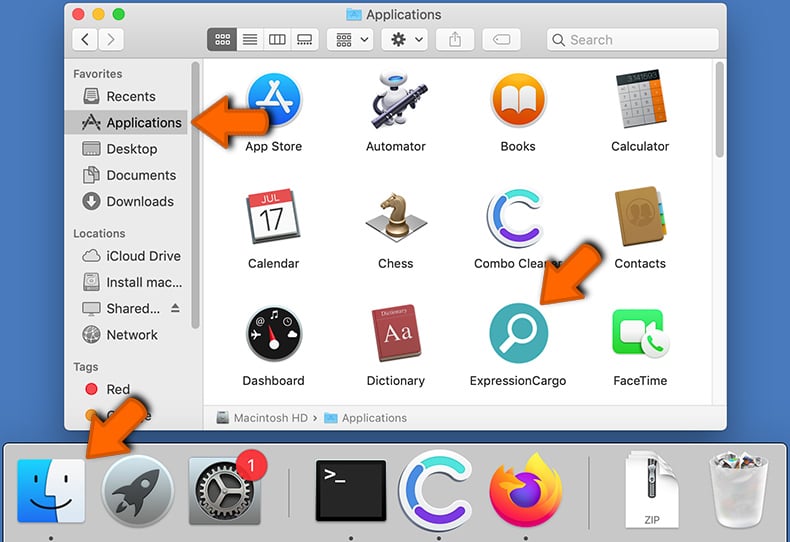
Click the Finder icon. In the Finder window, select "Applications". In the applications folder, look for "MPlayerX","NicePlayer", or other suspicious applications and drag them to the Trash. After removing the potentially unwanted application(s) that cause online ads, scan your Mac for any remaining unwanted components.
DOWNLOAD remover for malware infections
Combo Cleaner checks if your computer is infected with malware. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Frequently Asked Questions (FAQ)
My device is infected with Phoenix Worm malware, should I format my storage device to get rid of it?
While this method can fully eliminate Phoenix Worm, it also wipes all files and data stored on the device unless backups are available. Because of this, it should only be considered if trusted security software, such as Combo Cleaner, is unable to remove the infection.
What are the biggest issues that malware can cause?
Malware can serve different purposes, including encrypting files, stealing sensitive information, or installing other harmful programs. As a result, victims may encounter problems such as stolen accounts, financial damage, identity theft, data loss, and other serious consequences.
What is the purpose of Phoenix Worm?
The purpose of Phoenix Worm is to prepare systems for further attacks. It connects compromised devices to a remote server, collects system information, and can download or execute additional malware.
How did Phoenix Worm infiltrate my device?
Malware is spread through fraudulent emails, fake ads, tech support scams, compromised websites, infected USB drives, and pirated software. Attackers may also exploit outdated programs. Malware is often hidden in malicious documents, archives, scripts, or executable files that infect devices when opened (or when users take additional actions).
Will Combo Cleaner protect me from malware?
Combo Cleaner can detect and remove most malware infections, but advanced threats may sometimes remain hidden deep within the system. For this reason, running a complete system scan is important.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion