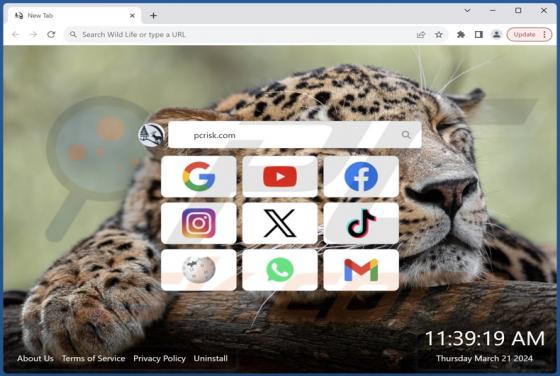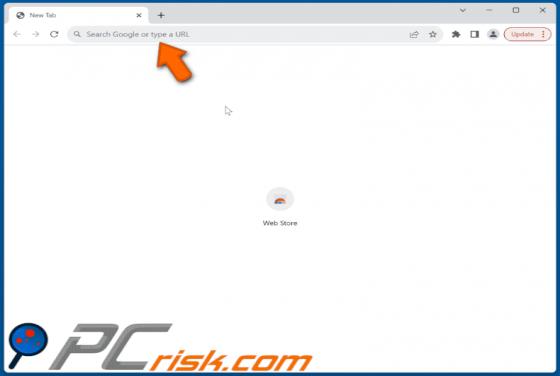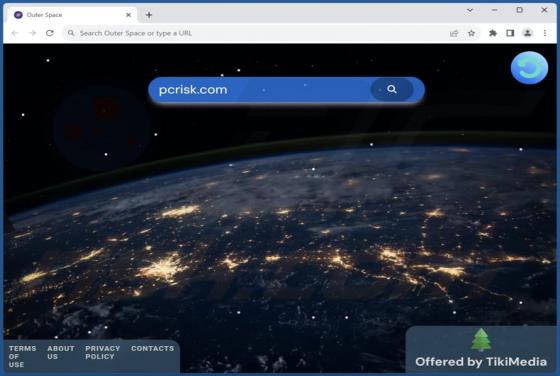
Outer Space Browser Hijacker
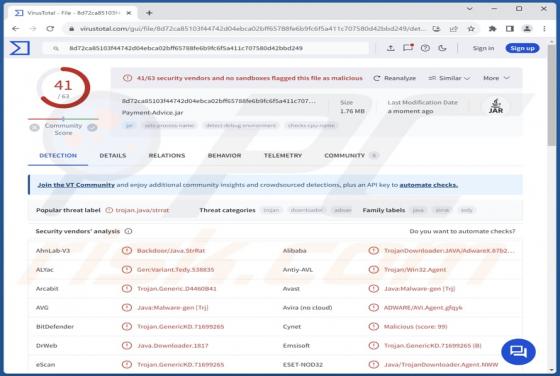
In our analysis of the Outer Space application, we identified characteristics typical of a browser hijacker. Once added, Outer Space alters the browser settings to promote a particular web address. Alongside browser hijacking, Outer Space may collect browsing-related and other pertinent informatio