Walliant Unwanted Application
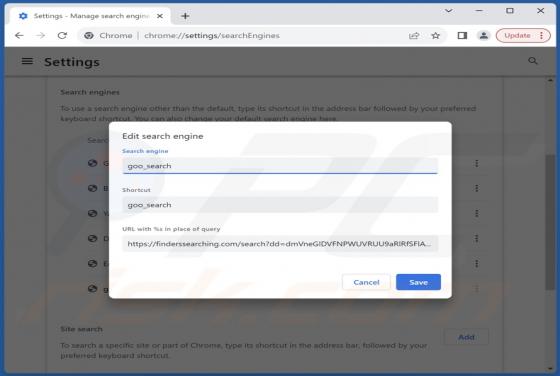
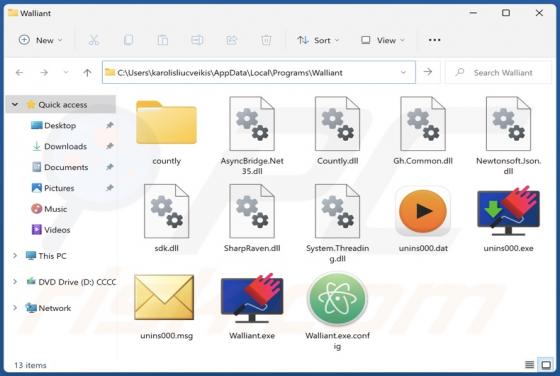
While browsing questionable websites, our researchers found the Walliant application. It is endorsed as an app that automatically changes desktop wallpapers to stunning images from around the world. However, Walliant operates as proxyware, i.e., it hijacks Internet bandwidth. This app might also