725 Ransomware
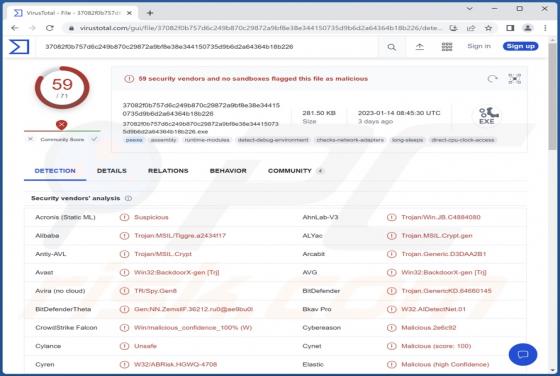
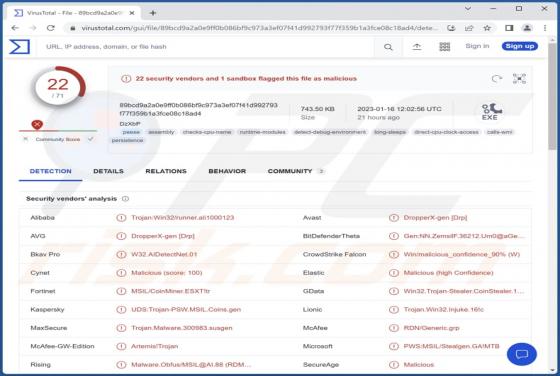
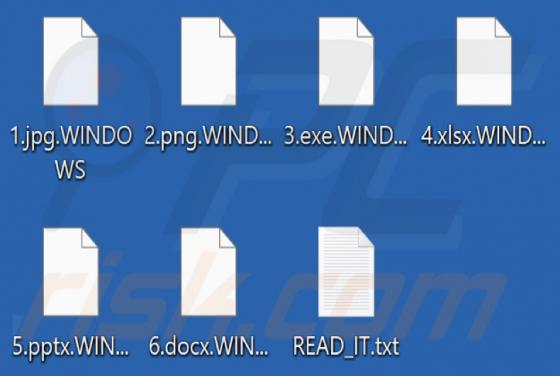
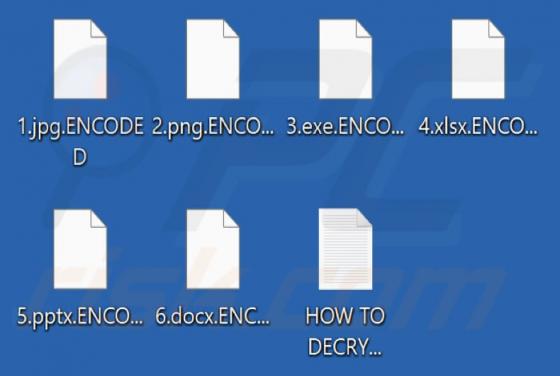
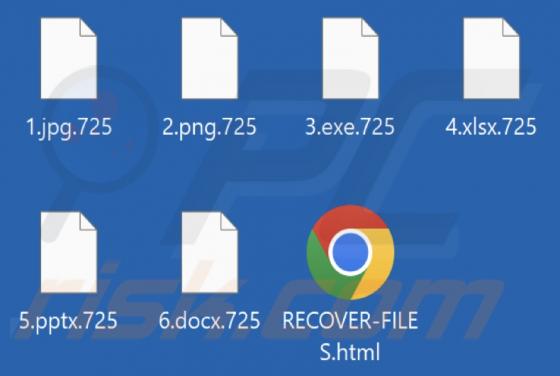
While checking out new submissions to VirusTotal, our researchers discovered the 725 ransomware. Evidence suggests that this malicious program could have been developed by the threat actors behind 32T ransomware. After we executed a sample of 725 on our test machine, it encrypted files and append