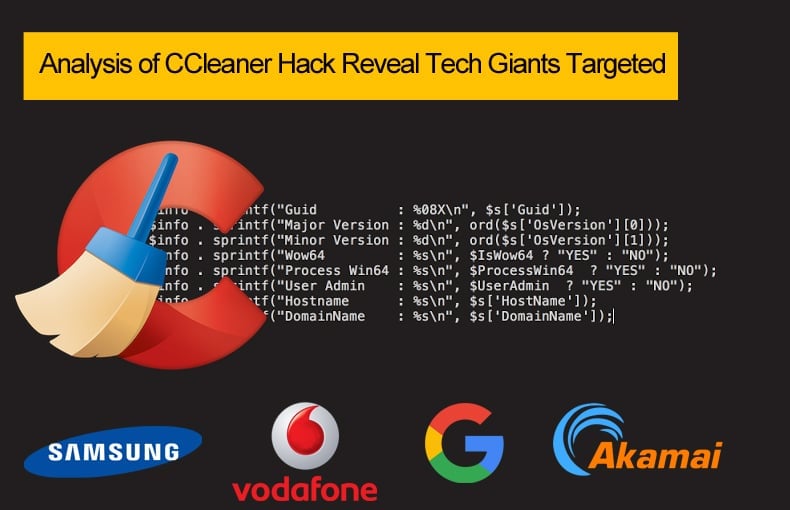
Analysis of CCleaner Hack Reveal Tech Giants Targeted
On Tuesday news broke that the latest version of CCleaner, a popular application owned by Avast, had been hacked, little was known as to the attacker’s intention. As is often the case with attacks conducted by knowledgeable and experienced attackers the targets and aim are exceptionally difficult to ascertain. Given time and dedicated research teams often these can be determined but determining who is responsible is harder.
The CCleaner hack was pulled off by modifying version 5.33 to include Floxif malware as reported by Cisco Talos and MorphiSec. Initially, it was believed that users who downloaded the jeopardized version merely downloaded a fake version of CCleaner. Researchers later determined that the version was indeed legitimate and CCleaner’s supply chain was jeopardized. Ultimately it was determined that Floxif, a malware downloader, was used in this instance to collect information such as computer name, a list of installed software, a list of running processes, MAC addresses for the first three network interfaces, and unique IDs to identify each computer in part.
Researcher’s also noted that the malware would only run on 32-bit systems and would also run on systems if the user who downloaded the update also had admin rights. If not the malware would quit execution.
A clean version of CCleaner released
Version 5.33 was initially available for download from August 15 to September 12, it was revealed that the compromised version was downloaded onto over 2 million machines. In response to the discovery, Avast released a new version which no longer contained the malware. Initial research revealed that Floxif could be used to download and run other binaries. When initially discovered there was no evidence that Floxif downloaded additional second-stage payloads on infected hosts.
While the hack itself did not cause much in the way of financial damage or massive reputational damage as we saw with the Equifax hack, researchers at Cisco Talos have warned that such supply chain hacks should be taken seriously. Even if little is understood about the attack initially given that the attackers could be described advanced adversaries the seriousness should not be assumed at face value.
New evidence emerges
New evidence published by researchers at Cisco Talos published on Wednesday this week may link the attack to an infamous cyberespionage group believed to be operating out of China. It also appears that the targets of the attack were all major companies within the tech sector. Based on how the attack was conducted and the malware used thin links have been established between the CCleaner hack and the group Axiom. The group has also been called APT17, DeputyDog, Tailgater Team, Hidden Lynx, Voho, Group 72, or AuroraPanda depending on which security firm is writing about the group.
Initially, it was Costin Raiu, Director of the Global Research and Analysis Team at Kaspersky Lab who discovered similarities in the code used in this instance and previous hack where Axiom is believed to be responsible. In Cisco Talos’ published report they confirmed that the code used was indeed similar but went on record to state “We are not definitively saying Group 72 was behind this, just that there was some shared code,” however, there is more evidence suggesting the group's involvement.
Researchers at Cisco Talos also were given a copy of a copy of the command and control server files, including its database via a third party. Analysis of the server revealed that tainted versions of CCleaner were sending information collected from infected hosts. Gathered info included computer name, a list of installed software, a list of running processes, MAC addresses for the first three network interfaces, and unique IDs to identify each computer in part. Cisco researchers were also able to verify the validity of this database by checking for data collected from their own test machines.
While it was initially believed that Floxif despite the ability to be able to download and execute other types of malware this feature was never used. Later developments revealed this to be false. Later research revealed that on 20 PCs around the globe the threat actors installed other malware. This was done by PHP files that ran on the C&C server would verify incoming users and identify suitable computers to download the second-stage malware, a lightweight backdoor. Researchers say that this second-stage backdoor would retrieve “an IP from data stegged into a github.com or wordpress.com search” and would download further malware on the system.
Tech Targets
In Cisco Talos’ latest published research it also listed who appeared to be the main targets of the attack. Victims were targeted based on their domain name, with victims coming from Singtel, HTC, Samsung, Sony, Gauselmann, Intel, VMWare, O2, Vodafone, Linksys, Epson, MSI, Akamai, DLink, Oracle (Dyn), Google, Microsoft, and ironically Cisco itself. Cisco notified those organizations of the potential dangers and potential breaches of their systems and networks.
Researchers are confident in their findings as within the C&C server tables were discovered which compared systems infected with the first stage malware and a second table which kept a record of systems further infected with second stage malware. Within the first table, a total of 700,000 computers were listed, while only 20 once duplicates are removed on the second table. Both tables only collected data from September 12 to September 16 with data appearing to be deleted predating the 12th. Just by running a simple SQL query would allow attackers to target anything they wanted. Cisco using the same method was able to identify 540 computers within governments and banks.
Given the attack vector, the similarity of code, and the targets suggest that Axiom may be behind the attack as these have been classified as hallmarks used previously by the cyber espionage group. The group spent a great deal of effort targeting tech companies in the early 2010s. Their efforts drew the attention of the following security firms Cisco, FireEye, F-Secure, iSIGHT Partners (now part of FireEye), Microsoft, Tenable, ThreatConnect, ThreatTrack Security, Volexity, Novetta, and Symantec. Together they joined efforts in operation SMN to determine the groups operating procedures. If the group is indeed responsible for this latest hack researchers may have to join forces once more.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion