Cobalt Again Targeting Banks
The Russian-based hacking group Cobalt is again targeting banks in a new campaign. In this latest campaign, it would appear that the group has limited its targets to Russian and Romanian banks. Cobalt has been active since 2016 and already boasts a number of scalps. As it stands the group has been credited with the theft of 9.7 million USD from the Russian MetakkinvestBank; ATM thefts of 2.18 million USD from Taiwan banks; a SWIFT attack on Russian banks; and more than 200 other attacks on banks in Europe, Thailand, Turkey and Taiwan. The group has also been seen to target industries other than the banking sector. Last year it was reported that Cobalt had expanded its range into also targeting government, telecom/Internet, service providers, manufacturing, entertainment, and healthcare organizations, often using government organizations and ministries as a stepping stone for other targets. Many of these utilized supply chain attacks.
Latest Campaign
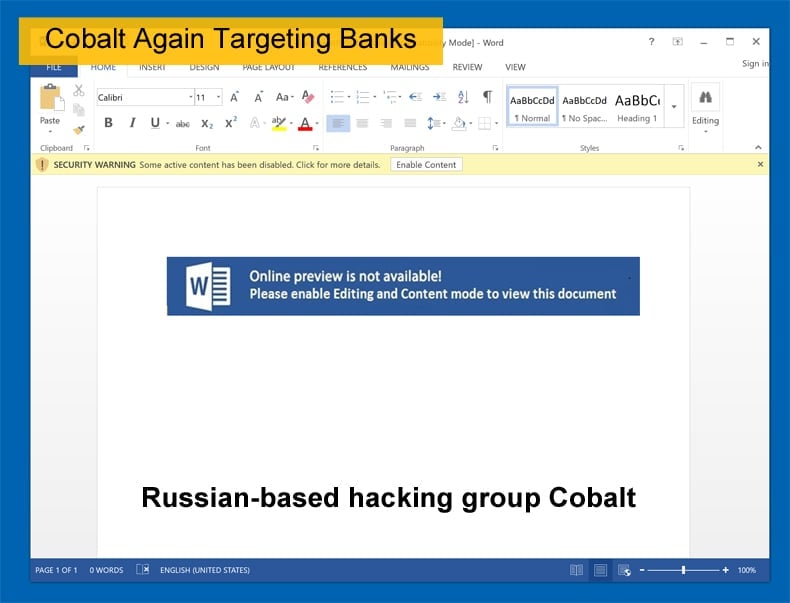
A traditional technique employed by the group is to start out with a spear phishing campaign. When targeting banks and other financial institutions the emails usually masquerade as other financial institutions or a financial supplier/partner domain to gain the target's trust. An analysis is the most recent campaign done by Netscout's ASERT researchers shows that this tried and true technique is still be used. However, in the new campaign, the emails may contain two malicious URLs. The first being a weaponized Word document, while the second is a binary with a .jpg extension.
Researchers discovered that with the two URLs there was also two malware variants been used. Both malware variants have been employed by Cobalt in the past, which can be seen as evidence linking Cobalt to the latest campaign. The first was a JavaScript backdoor that shares functionality with other backdoors. The second is COOLPANTS which researchers noted that COOLPANTS appears to be an evolution of Coblnt, another favored malware variant used by Cobalt. The researchers at ASERT found a new sample almost identical to COOLPANTS on August 13. Another interesting discovery surrounding this campaign is the domain names used, all of which, including newly added names, masquerade as legitimate financial services organization. These include compass[.]plus; eucentalbank[.]com; europecentalbank[.]com; inter-kassa[.]com; and unibank[.]credit. The real Interkassa is a payments processing firm based in Ukraine.
Analysis of the JavaScript backdoor was done by Trend Micro was done last year with researchers attributing its use to Cobalt. In Trend Micro’s analysis, it was termed “more_eggs” and is nearly identical to the one been used in this campaign. Both provide five commands that essentially allow attackers to take over an infected system. The commands are d&exec which downloads and execute a PE file; more_eggs which downloads an update for itself; gtfo which deletes itself and related registry entries; more_onion which executes the 'new' copy of itself; and vai_x which executes a command via cmd. The only difference occurring between the commands is there naming with the earlier one having the name more_power for vai_x.
How hacking Banks affects Consumers
There is sometimes a misbelief that by hacking a bank the hackers are some kind of digital Robin Hood figure. However, in some cases, it is often the consumer that might have to bear the brunt of such a heist. The consumer in these cases is invariably you and me in these scenarios. Central to this false belief is that the hackers stole directly from the banks themselves, meaning that the customers are left no way out of pocket. In an article published by CNBC that detailed how high profile hacks were impacting on victims years after the hack occurred. Many of the cases examined dealt with data leaks and how user data could be used for identity theft. Further, often the stolen personal details are sold via Dark Web marketplaces.
That is one scenario, another is where hackers manage to steal accounts directly from customers’ accounts. In 2016, UK based bank Tesco’s was forced to halt online payments for current account customers after money was taken from 20,000 accounts with approximately 40,000 accounts experiencing suspicious transactions. Often the bank will reimburse the customer but under certain conditions, the bank may not feel obliged to return stolen funds. This is often the case when an account holder unwittingly gave login details via a phishing campaign. Here the consumer is directly affected as they are out of pocket and have to change login details and open fraud cases with the bank or police.
What if the scenario when money is taken directly from the bank. While there is a potential for increased insurance costs or bank charges the consumer will not suffer directly. What is a concern is if the attack results in the bank having to close its doors for good. This could lead account holders losing savings or worse. According to some experts, the Financial Stability Oversight Council, associated with banking security in the US, has largely failed to acknowledge and plan for cyber attacks that threaten the solvency of a major bank. These attacks could target bank processing systems and disrupt critical financial transactions needed to avoid margin calls, for example, triggering a default. Further, Professor Richard Benhman, chairman of Britain’s National Cyber Management Center, told the BBC that “a major bank will fail as a result of a cyber attack in 2017 leading to a loss of confidence and a run on that bank.” While that may not have occurred to the best of the writer’s knowledge, the danger is present.
These are current threats which Russian and Romanian banks are having to deal with. ASERT researchers concluded that
“Cobalt Group will continue targeting financial organizations in Eastern Europe and Russia based on the observables in this campaign and their normal modus operandi.”
While bad news for those regional banks other banks is also targeted as, according to Trend Micro, Cobalt starts by targeting Russia and the old USSR states to test out its methodology before moving on to European and other targets.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion